2026 State of Security: Geopolitical Fragmentation and the Redefining of Global Conflict
Executive Summary
The global security landscape in 2025 was defined by geopolitical fragmentation, a trend characterized by the unwinding of international norms and the rise of transactional diplomacy. This fracturing has moved risk across once-distinct domains, leading to a convergence of state objectives, criminal capabilities, and private-sector technology.
Critical takeaways from the current environment include:
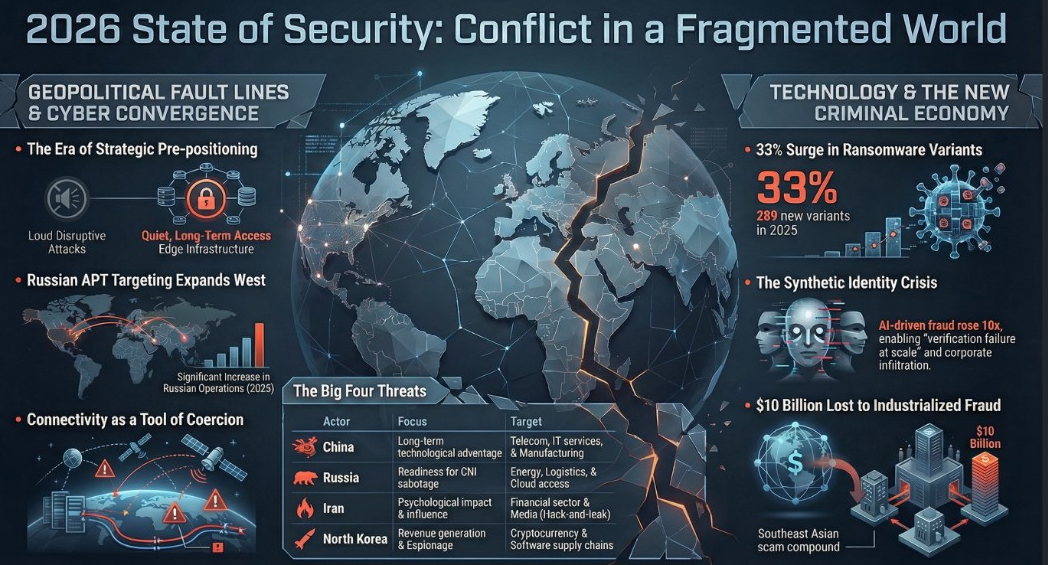
- Shift to Strategic Pre-positioning: State-sponsored cyber actors (China, Russia, Iran, and North Korea) have pivoted from immediate disruption toward the quiet accumulation of persistent access to identity systems, cloud environments, and edge infrastructure.
- Normalized Kinetic and Cyber Synchronicity: Cyber operations, influence campaigns, and hacktivism are now routinely embedded into kinetic conflicts, as seen in the Middle East, South Asia, and Southeast Asia.
- Fragmentation of Cybercrime: Law enforcement pressure has fractured large criminal enterprises, resulting in a more decentralized, modular, and resilient criminal ecosystem that leverages private infrastructure like Telegram.
- The AI "Verification Failure": While AI has not yet achieved full autonomy in cyberattacks, it has significantly lowered the barrier to entry for social engineering, leading to a tenfold increase in deepfake-enabled fraud and a 300% rise in synthetic identity document fraud in early 2025.
- 2026 Outlook: The threat environment is moving toward a baseline of simultaneous regional crises and "gray-zone" coercion, where connectivity disruptions (undersea cables, satellites) and identity abuse will drive systemic risk.
--------------------------------------------------------------------------------
I. Geopolitical Fragmentation and the Global Disorder
Geopolitical fracturing in 2025 was driven by the selective enforcement of norms and a greater tolerance for risk among major powers. This shift has transitioned the international system from deterrence-based stability toward a model of preemptive action and hybrid coercion.
Regional Flashpoints and Hard-Power Competition
- Russia and Ukraine: Russia maintains a strategic advantage by sustaining a protracted war to block Ukraine's NATO accession. Despite minimal territorial gains (approx. 4,669 sq km in 2025), Moscow uses drone strikes and cyber pressure on energy and logistics to strain Western resolve.
- The Middle East (Israel-Iran): The June 2025 conflict, including Israel’s Operation Rising Lion, marked the normalization of preventive strikes. The U.S. conducted its first-ever direct attacks on Iranian territory (Fordow, Natanz, Isfahan), significantly degrading Iran’s nuclear infrastructure and proxy networks.
- South Asia (India-Pakistan): Tensions reignited in May 2025 following the Pahalgam attack. Both nations engaged in missile strikes and nuclear signaling, while state-aligned cyber groups (APT36 and SideWinder) conducted preparatory espionage.
- Southeast Asia (Thailand-Cambodia): Border clashes near Chong Bok and the collapse of the Joint Boundary Commission led to a 99% collapse in cross-border trade, demonstrating how localized conflict generates immediate humanitarian and economic risk.
- The Western Hemisphere: The U.S. adopted a "primacy-focused" approach, reasserting dominance through unilateral military actions against drug cartels and the January 2026 operation to capture Venezuelan President Nicolás Maduro.
--------------------------------------------------------------------------------
II. State-Sponsored Cyber Operations
Hostile state actors have moved away from one-time disruptive attacks toward treating digital access as a long-term strategic asset.
The "Big Four" Threat Actors
Actor | Primary Objectives | Key Tactics and Trends |
China | Long-term strategic positioning; technological self-sufficiency. | Exploitation of edge devices (Cisco, Fortinet, Ivanti). The RedMike campaign targeted over 1,000 devices across 100+ countries. |
Russia | Intelligence collection; NATO destabilization; readiness for CNI disruption. | Shift toward stealthy, credential-based intrusions (BlueDelta, Sandworm). Targeting of U.S. and Canadian critical infrastructure increased in 2025. |
Iran | Regional signaling; psychological impact; proxy coordination. | Use of hack-and-leak fronts (Handala, Cyber Toufan) and exaggerated claims of ICS compromise to create a continuous pressure environment. |
North Korea | Revenue generation (crypto theft); industrial espionage. | Deployment of fraudulent remote IT workers; eighteen recorded cryptocurrency thefts in 2025; "Contagious Interview" social engineering campaigns. |
Commercial Spyware Proliferation
Despite international efforts like the Pall Mall Code of Practice, the commercial spyware market remains fragmented and active. Vendors such as Intellexa (Predator), Candiru (DevilsTongue), and Paragon Solutions (Graphite) continue to serve government clients, often routing traffic through CDNs to evade detection.
--------------------------------------------------------------------------------
III. Hacktivism and Influence Operations
The 2025 threat landscape saw a sophisticated synchronization of "patriotic volunteers" and state-aligned influence networks.
- Feedback Loops: Genuine intrusions are now routinely paired with exaggerated claims and disinformation to amplify conflict narratives.
- Case Study: India-Pakistan: Pro-India network Hidden Charkha and pro-Pakistan network Khyber Defender operated across the 2025 escalation window, using forged documents to overstate cyber impacts on electric grids.
- Case Study: Israel-Iran: The group Predatory Sparrow (aligned with Israel) targeted Iranian financial entities, while Iranian state media amplified hacktivist claims of breaching Israeli nuclear sites to sow domestic confusion.
--------------------------------------------------------------------------------
IV. The Evolution of Cybercrime
The cybercriminal ecosystem has transitioned from centralized forums to a modular, decentralized model.
English-Speaking Collectives and Social Engineering
English-speaking groups have moved from centralized boards (like BreachForums) to Telegram and private infrastructure.
- Scattered LAPSUS$ Hunters (SLSH): A self-proclaimed merger that targeted Salesforce, Jaguar Land Rover, and Salesloft Drift.
- Tactics: Reliance on help desk impersonation to bypass MFA and "one-to-many" exploits using compromised authentication tokens.
Ransomware-as-a-Service (RaaS) Innovation
While ransomware payments declined in 2025, the number of variants increased by 33% (289 new variants identified).
- Modular Tooling: Groups now share "AV killer" tools and offer flexible options like "extortion-only" or "legal assessment" services (e.g., Qilin).
- Industrialized Fraud: Chinese-speaking TCOs in Southeast Asia use coerced labor and AI automation to run massive scam compounds. The Huione Group in Cambodia served as a primary marketplace for money laundering until disrupted by U.S. sanctions in 2025.
--------------------------------------------------------------------------------
V. Artificial Intelligence: Hype vs. Reality
AI in 2025 acted as a force multiplier for efficiency rather than a source of autonomous, novel tradecraft.
The AIM3 Framework (AI Malware Maturity Model)
Insikt Group developed the AIM3 framework to assess the maturity of AI in malware. Most observed activity remains at Levels 1-3 (Experimenting to Optimizing):
- LLM-Translated: Localizing phishing content for higher convincingness.
- LLM-Generated: Support for writing or debugging code.
- LLM-Deployed: Delivering malware through AI ecosystems (e.g., poisoned training packages).
Strategic AI Competition
The U.S. and China are engaged in a race for AI dominance with distinct strategies:
- U.S. Advantage: Leads in private sector investment ($110 billion in 2024) and high-performing frontier models.
- China Advantage: Focuses on AI diffusion and open-source embedding. Modified Alibaba models on Hugging Face now outnumber those from U.S. tech giants combined.
--------------------------------------------------------------------------------
VI. Strategic Outlook for 2026
The following trends are forecast to dominate the security environment in the coming year:
- Connectivity Disruption as Coercion: State actors will target undersea cables and satellite PNT systems. Correlated, low-level disruptions should be viewed as potential rehearsals for signaling activity.
- The Synthetic Identity Crisis: AI-generated audio and video will make Business Email Compromise (BEC) more scalable. Hostile states will expand the North Korean model of embedding fraudulent workers into non-technical roles like HR and Finance.
- Fragmented Ransomware: The "big-game hunting" era is ending. Smaller, faster-moving groups will favor shorter attack cycles and lower demands to avoid law enforcement "Operation Endgame" style takedowns.
- AI as an Attack Surface: Vulnerabilities unique to LLMs (prompt injection and data poisoning) will become standard entry points for malicious operations.
- Quantum and Robotics: Quantum readiness will move from planning to spending, while space systems and robots will become contested "cyber-physical" terrain.
"Uncertainty is not a phase or a trope. It is the operating environment. And this year, fragmentation is driving it." — Levi Gundert, Chief Security & Intelligence Officer