AI as a Weapon: How One Hacker Breached 600 Firewalls in 5 Weeks

Amazon's threat intelligence team exposes a disturbing new template for AI-augmented cybercrime — and why your security fundamentals may be your only real defense.
KEY FACTS AT A GLANCE600+ FortiGate firewalls compromised across 55+ countriesCampaign ran January 11 – February 18, 2026 (38 days)No zero-day exploits used — only misconfigurations and weak credentialsThreat actor assessed as low-to-medium technical skill, augmented by AIActivity consistent with pre-ransomware staging operations

The AI-Powered Assembly Line for Cybercrime Has Arrived
On February 20, 2026, Amazon's Chief Information Security Officer CJ Moses published a report that should stop every security professional cold. In less time than it takes to complete a standard penetration test engagement, a single threat actor — or possibly a small group of Russian-speaking individuals — used commercially available artificial intelligence tools to compromise more than 600 Fortinet FortiGate firewalls spanning over 55 countries.
This wasn't a nation-state operation deploying classified zero-day exploits. There were no novel techniques, no undiscovered vulnerabilities weaponized at scale. What Amazon documented was arguably more alarming: a low-to-medium-skilled, financially motivated actor who used off-the-shelf AI services to punch so far above their technical weight class that the campaign achieved an operational scale that would have previously required a significantly larger and more skilled team.
The cybersecurity community has warned for years that AI would democratize advanced attacks. This campaign is the evidence.
How the Attack Worked: Fundamentals, Not Fireworks
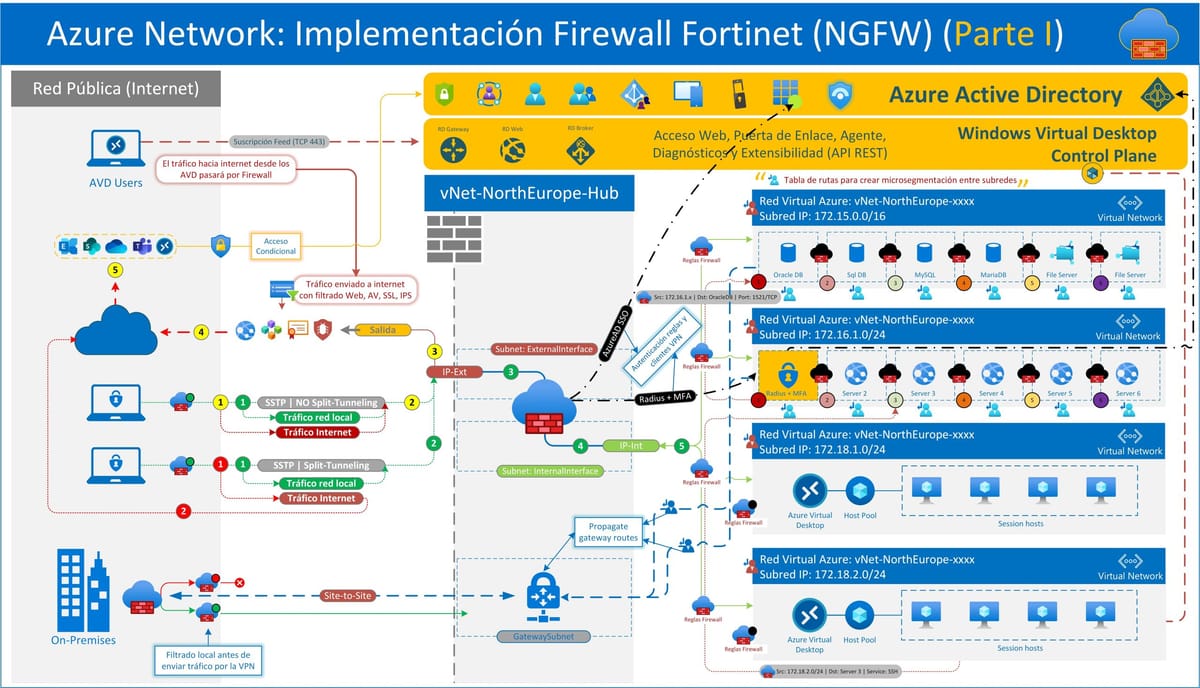
The mechanics of the compromise were almost insultingly simple — which is precisely the point. The attacker began with systematic scanning of FortiGate management interfaces exposed to the internet across ports 443, 8443, 10443, and 4443. They weren't hunting for a specific vulnerability; they were hunting for organizations that had failed to implement the most basic security hygiene: removing internet-facing management access and enforcing multi-factor authentication.
Where management interfaces were exposed and protected only by single-factor authentication with weak or reused credentials, the attacker gained access. Once in, the value they extracted was substantial. Full device configurations were harvested, containing:
- SSL-VPN user credentials with recoverable passwords
- Administrative credentials
- Complete network topology maps
- IPsec VPN peer configurations
- Firewall policy details revealing internal architecture
These configuration files were then parsed, decrypted, and organized using AI-generated Python scripts — turning what would have been time-consuming manual credential harvesting into an automated pipeline. The attacker didn't need to be an expert in Fortinet internals to extract and weaponize that data. The AI did the translation work.
The Role of AI: Two Providers, One Devastating Effect
Amazon's researchers identified a two-LLM operational structure throughout the campaign. One commercial AI provider served as the primary backbone, handling tool development, attack planning, and command generation. A second AI service functioned as a supplementary assistant, helping the attacker pivot within specific compromised networks when needed.
Critically, Amazon's visibility into this campaign came in part due to the attacker's poor operational security. The attackers left publicly accessible infrastructure that hosted not just their tools, but their AI-generated attack plans, victim configurations, and source code for custom tooling. Researchers could essentially read the attacker's playbook — and what they saw was a structured, AI-assisted methodology applied consistently across hundreds of targets.
The AI tools weren't generating novel attacks. They were generating scale. Scripts that would have taken days to write were generated in minutes. Attack paths that would have required expertise to identify were surfaced automatically. The human attacker's role shifted from technical execution to target selection and campaign management — and even that was likely AI-assisted.
Inside the Breach: Pre-Ransomware Staging
The post-exploitation activity followed a pattern that Amazon's researchers characterized as consistent with pre-ransomware operations. Using credentials extracted from the FortiGate configurations, attackers pivoted from the perimeter devices into victim internal networks. From there, they:
- Compromised Active Directory environments
- Extracted complete credential databases
- Specifically targeted backup infrastructure
This sequencing matters. Ransomware operators who understand their trade don't just encrypt files — they destroy the victim's ability to recover without paying. Targeting backup infrastructure before deploying ransomware is a signature of sophisticated, financially motivated operations. The fact that a low-skill actor executed this playbook successfully demonstrates how AI is compressing the knowledge gap between skilled ransomware crews and opportunistic criminals.
One telling behavioral indicator: when the attackers encountered hardened environments or more robust security controls, they didn't dig in or adapt. They simply moved on to softer targets. Their competitive advantage was breadth and automation, not depth of skill. AI gave them the ability to attempt hundreds of compromises; human expertise would have been needed to break through hardened defenses. They never developed that expertise — and didn't need to.
Geographic Reach and Target Profile
The campaign was explicitly opportunistic. Amazon identified no specific industry targeting — instead, the attacker went where the exposed management ports and weak credentials were. Concentrations of compromised devices were identified across:
- South Asia
- Latin America and the Caribbean
- West Africa
- Northern Europe
- Southeast Asia
Amazon also noted organizational-level compromise patterns, including clusters associated with managed service provider deployments — a concerning finding that suggests downstream victims may extend well beyond the 600+ devices directly compromised.
For managed service providers reading this: if you manage FortiGate deployments and have not audited your management interface exposure and credential practices in recent months, that audit needs to happen today.

Context: Fortinet Under Sustained Assault
This campaign did not occur in isolation. FortiGate firewalls have been under sustained pressure since late 2025, with multiple exploitation campaigns targeting authentication bypass vulnerabilities, including actively exploited CVEs. Amazon was explicit that the campaign they documented did not leverage any of these software vulnerabilities — meaning organizations that patched diligently were still at risk if they left management interfaces exposed to the internet without MFA.
This is a critical distinction. Patch management matters and remains essential. But patching alone cannot compensate for exposed attack surface and weak credential practices. The threat actor in this campaign bypassed all of Fortinet's software security improvements by simply finding organizations that hadn't addressed the fundamentals.
The broader trend is also worth noting: Google reported separately that threat actors are abusing Gemini AI across all stages of cyberattacks, mirroring what Amazon observed here. This is no longer an emerging threat. It is the current operating environment.
What This Means for Security Teams
The implications of this campaign are stark for anyone responsible for network security. The threat model has fundamentally shifted. Historically, the sophistication of an attack correlated roughly with the resources and expertise behind it. Nation-state actors could operate at scale with advanced capabilities; individual criminals were constrained by their own technical limits. AI has severed that relationship.
A single financially motivated individual can now execute what previously required a team. They can generate custom tooling, parse complex configuration data, automate credential harvesting, and manage a campaign spanning hundreds of targets across dozens of countries — all with commercial tools that cost a fraction of what a skilled penetration tester would charge for a single engagement.
For defenders, this means attack volume is going to increase, and it's going to increase in ways that look operationally sophisticated even when the human behind the keyboard is not. Automated, AI-generated attack scripts will be better-written, better-structured, and more consistent than what most individual attackers produced manually. Detection strategies that relied on attacker errors will become less reliable.
Defensive Recommendations: Hardened Fundamentals Win
Amazon's Moses was direct in his defensive guidance, and none of it is new — which is the uncomfortable truth this campaign underscores. These aren't advanced security engineering recommendations. They are the basics that this campaign exploited when organizations failed to implement them.
1. Remove Management Interface Exposure
FortiGate management interfaces should never be accessible from the public internet. If remote administration is required, it must be routed through a VPN with strong authentication. This single control would have prevented the initial access in this entire campaign.
2. Enforce Multi-Factor Authentication Everywhere
Single-factor authentication on perimeter devices is an unacceptable risk in 2026. MFA must be enforced on all management access, SSL-VPN access, and any interface exposed to credential-based attack. This campaign's success was predicated on the absence of MFA across hundreds of victim environments.
3. Separate VPN and Active Directory Credentials
VPN credentials that match Active Directory passwords create a direct bridge from perimeter compromise to internal network access. Enforce unique credential sets for VPN access that are not shared with domain accounts, limiting the blast radius of a FortiGate compromise.
4. Harden and Isolate Backup Infrastructure
Backup systems are a primary ransomware target for a reason. Ensure backups are segmented from the primary network, protected by separate credentials, and include offline or immutable copies that cannot be modified or deleted by a compromised domain admin account.
5. Monitor for Post-Exploitation Indicators
Invest in detection capabilities around Active Directory reconnaissance, bulk credential extraction (ntds.dit access, LSASS dumps), unusual administrative tool usage, and lateral movement patterns. If initial access prevention fails, post-exploitation detection is your last meaningful opportunity to limit damage before ransomware deployment.
6. Patch Perimeter Devices Aggressively and Continuously
Even though this campaign did not use software vulnerabilities, others in the ongoing wave of Fortinet-targeted attacks do. Perimeter devices must be prioritized in your patch management cadence — they are the first target and offer the highest-value access to attackers.
The Uncomfortable Bottom Line
There is a discomforting irony embedded in this research. Amazon documented an attacker using AI to exploit the most basic security failures — exposed management interfaces and weak credentials — at a scale that no previous low-skill actor could have managed alone. The sophisticated tool served deeply unsophisticated attack conditions.
That is both the good news and the bad news. The good news: strong security fundamentals still work. Organizations that had removed internet-exposed management access and enforced MFA were not compromised in this campaign, regardless of how sophisticated the attacker's AI toolchain was. The attacker moved on to easier targets. Defense-in-depth, properly implemented, holds.
The bad news: we already knew these fundamentals, and hundreds of organizations across 55 countries still hadn't implemented them. AI didn't create new attack vectors. It created the capacity to find and exploit existing ones at a scale that makes every unaddressed gap a liability.
As Moses put it, organizations should anticipate that AI-augmented threat activity will continue to grow in volume from both skilled and unskilled adversaries. The defenders who get ahead of this curve won't be those who match AI with AI — at least not yet. They'll be the ones who finally close the gaps that attackers have been exploiting for years, before an AI-powered campaign finds them at scale.
Sources: Amazon Security Blog (CJ Moses), The Hacker News, BleepingComputer, CyberSecurityNews, CSO Online