Briefing: The Cyber Threat Intelligence Capability Maturity Model (CTI-CMM)
Executive Summary
The Cyber Threat Intelligence Capability Maturity Model (CTI-CMM) Version 1.3 is an industry-led, vendor-neutral framework designed to help organizations build, measure, and mature their CTI programs. Its core philosophy is a stakeholder-first approach, defining success by the CTI program's ability to provide demonstrable value to the business units it supports. The model is structured around 11 distinct domains, representing common organizational functions like Risk Management and Incident Response, and measures capability across four maturity levels (CTI0 to CTI3).
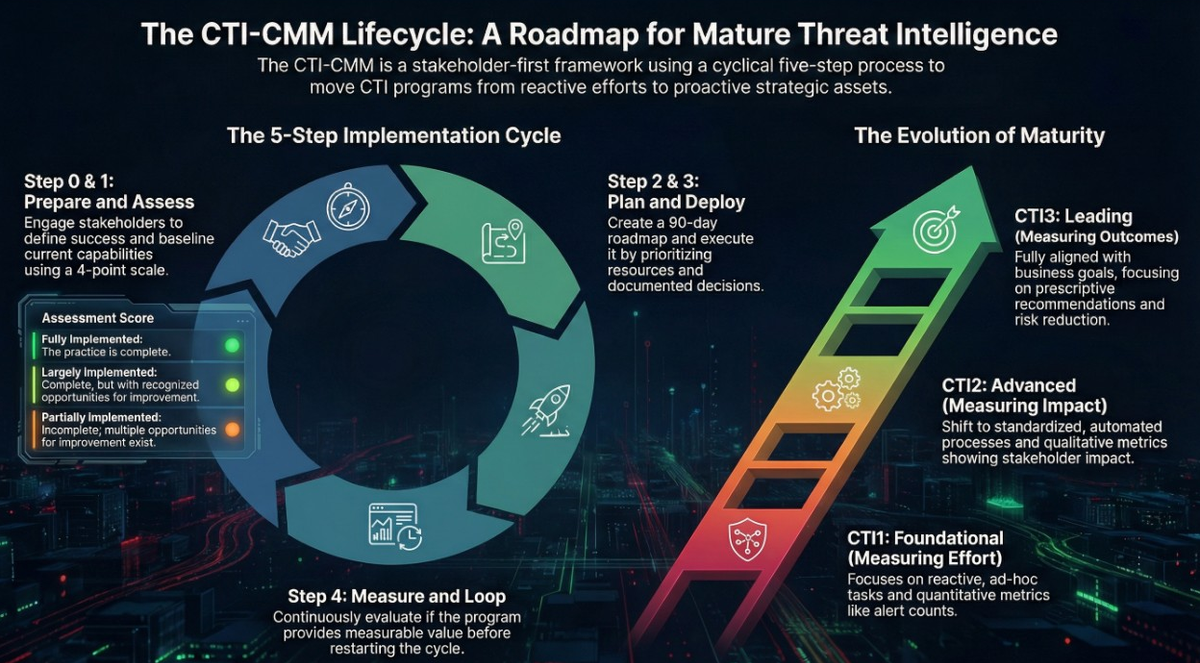
Progression through the maturity levels is characterized by a shift from reactive, ad hoc practices (Foundational) to proactive, standardized, and automated processes (Advanced), culminating in prescriptive, business-aligned strategies that drive long-term value (Leading). A key indicator of this progression is the evolution of metrics, which move from measuring basic effort (e.g., number of reports) to quantifying impact (e.g., reduction in detection time) and ultimately demonstrating strategic outcomes (e.g., risk reduction on vetted asset acquisitions).
Implementation follows a continuous, five-step cyclical process: Prepare, Assess, Plan, Deploy, and Measure. This lifecycle emphasizes explicit stakeholder engagement, critical self-assessment using a four-point scale, and data-driven planning. To ensure accuracy, the model recommends a critical mindset during assessment, notably the "lower score rule"—choosing the lower maturity level when in doubt to realistically identify areas for improvement. The CTI-CMM provides a comprehensive roadmap for aligning CTI capabilities with organizational objectives, bridging the gap between intelligence functions and business stakeholders to foster a more resilient and threat-informed enterprise.


--------------------------------------------------------------------------------
The CTI-CMM Framework and Core Concepts
The Cyber Threat Intelligence Capability Maturity Model (CTI-CMM) provides a structured framework for organizations to establish, refine, and measure the effectiveness of their CTI programs. Developed through industry collaboration and inspired by established frameworks like the U.S. Department of Energy's C2M2, its primary goal is to align CTI capabilities with the needs of specific business stakeholders, thereby creating impactful and demonstrable value.
Publication Details:
- Title: Cyber Threat Intelligence Capability Maturity Model
- Version: 1.3
- Date: © 2024 – 2026
- Motto: "Industry Inspired. Industry Led."
The model defines CTI as the "eyes and ears" of a proactive defense, a discipline focused on understanding adversary capabilities, intent, and TTPs to arm decision-makers and reduce organizational risk.
Core Principles and Structure
The CTI-CMM is built upon a set of shared values and principles, including:
- Collaboration: Intelligence provides value by supporting stakeholder decision-making.
- Continuous Improvement: Intelligence is never complete; constant improvement is crucial.
- Actionability: Intelligence must be actionable and based on stakeholder needs.
- Measurement: Effectiveness and impact must be measured both quantitatively and qualitatively.
The model is organized into three primary structural components: Domains, Maturity Levels, and a distinction between Strategic, Operational, and Tactical intelligence.
The 11 CTI Domains
The framework is organized into 11 domains, each representing a key business unit or function that CTI supports. For each domain, the model specifies a "Domain Purpose" and a corresponding "CTI Mission" that outlines how intelligence serves that function.
Domain | Abbreviation | CTI Mission |
Asset, Change, and Configuration Management | ASSET | Monitor the organization’s attack surface to rapidly detect at-risk assets and reduce exposures based on the current and anticipated threat landscape. |
Threat and Vulnerability Management | THREAT | Maintain comprehensive and contemporary knowledge of the relevant evolving threat landscape to reduce risk against new and emerging adversaries, malware, vulnerabilities, and exploits. |
Risk Management | RISK | Align CTI with the organization’s risk management strategies to inform and prioritize risk reduction efforts and improve assessments of likelihood and potential impact. |
Identity and Access Management | ACCESS | Proactively inform IAM strategies, reduce incident detection times, accelerate remediation, and enable continuous improvements to safeguard critical assets. |
Situational Awareness | SITUATION | Drive threat-informed decision-making for all stakeholders based on the current and forecasted threat landscape to create a commensurate state of security readiness. |
Event and Incident Response, Continuity of Operations | RESPONSE | Capture, correlate, prioritize, and enrich intrusion activity in the enterprise environment to create an advantage for incident responders and strengthen security posture. |
Third-Party Risk Management | THIRD-PARTIES | Strengthen third-party risk management by continuously monitoring, detecting, assessing, and mitigating potential incidents posed by vendors and suppliers. |
Fraud and Abuse Management | FRAUD | Create awareness around new and emerging trends in fraud and brand protection to reduce risk against employees, customers, and the brand. |
Workforce Management | WORKFORCE | Support hardening of the human element of the organization’s attack surface by enhancing workforce management initiatives with insights into adversary tactics. |
Cybersecurity Architecture | ARCHITECTURE | Support the development of a robust and resilient IT architecture by providing insights into cyber threats and recommending system and information security practices. |
Cybersecurity Program Management | PROGRAM | Ensure the organization’s resilience and success through a measurable CTI program that aligns strategic goals and fosters strong governance, planning, and collaboration. |
Maturity Indicator Levels (MILs)
The CTI-CMM uses a scale of four maturity indicator levels (0 to 3) to measure an organization's capability to perform practices consistently and repeatably.
Level | Characteristics |
CTI0: Pre-Foundational | Absence of practice: No practices are performed at this level. |
CTI1: Foundational | Ad hoc and reactive: Practices are undocumented, unplanned, and response-driven. They deliver short-term results for a limited subset of stakeholders. Metrics focus on effort and throughput, providing limited measurable value. |
CTI2: Advanced | Standardized and proactive: Practices are documented, planned, and standardized, often with automation at scale. They deliver short- and intermediate-term results through proactive and predictive intelligence. Metrics include qualitative feedback and demonstrate impact, providing moderate value. |
CTI3: Leading | Prescriptive and business-aligned: Practices are cross-functional, well-standardized, and aligned to business outcomes. They deliver long-term strategic results through prescriptive recommendations and continuous improvement. Metrics are comprehensive, map to future actions, and assess overall program effectiveness. |
Strategic, Operational, and Tactical Alignment
A mature CTI program demonstrates its ability to affect outcomes at all levels of the enterprise. The CTI-CMM defines these three distinct but complementary levels:
- Strategic: Focuses on long-term planning, informs senior leadership, guides policy development, and supports high-level risk assessments.
- Operational: Supports specific campaigns and provides actionable intelligence for security operations, incident response, and risk management.
- Tactical: Addresses immediate threats, offering real-time or near-real-time support to front-line defenders like SOC analysts with Indicators of Compromise (IoCs) and attack patterns.
--------------------------------------------------------------------------------
The 5-Step Implementation Lifecycle
The CTI-CMM advocates for a cyclical, five-step process to ensure continuous measurement, demonstration of value, and program growth.
Step 0: Prepare
This foundational stage occurs before any assessment begins. It involves recognizing the model as a frame of reference and engaging in three key discussions:
- Stakeholder Engagement: Explicitly identify stakeholders (e.g., SOC analysts, risk managers), establish relationships, and understand their reporting requirements and definitions of success.
- Setting Ambitions: Determine the "ideal end state" for the CTI program and a realistic timeframe for achievement, using the CTI-CMM to translate intangible goals into detailed actions.
- Program Planning: Create a tangible plan that maps actions to time, people, and cost, integrating with existing projects to report on value contribution.
Step 1: Assess
Perform a self-evaluation to baseline the current implementation of CTI practices for each domain.
- Scoring: Use the four-point scale: Not Implemented, Partially Implemented, Largely Implemented, and Fully Implemented.
- Best Practice: Be critical in responses. If torn between two scores, choose the lower score to ensure a realistic assessment and to clearly identify areas for improvement.
- Outcomes: The assessment produces two viewpoints: Domain Specific Maturity (the program's maturity relative to a single domain) and Enterprise Wide Maturity (an aggregated score for the entire organization).
Step 2: Plan
Chart a progressive path to improve capabilities based on the assessment results and stakeholder expectations.
- Prioritization: Identify strong domains, areas for improvement, and domains where the most progress can be made in the next 90 days.
- Alignment: Ensure the plan aligns with strategic information from business executives and contains clear descriptions of activities and their value propositions.
Step 3: Deploy
Execute the plan by prioritizing resources like data feeds, vendor solutions, and staffing to enable capability growth.
- Explicit Decision-Making: Document priority decisions in writing to avoid operating on assumptions and allow for flexibility.
- First 90 Days: For new programs, success during this initial period is critical for shaping stakeholder opinions on the program's value.
Step 4: Measure
Continuously monitor and assess the CTI program's maturity and value delivery.
- Value Assessment: Routinely ask if the program is providing measurable value and delivering on prioritized areas.
- Feedback Loop: If performance is not as expected, this stage provides an opportunity for feedback, learning, and readjusting priorities before beginning the cycle again.
--------------------------------------------------------------------------------
Evolving Metrics: From Effort to Outcomes
A central theme of the CTI-CMM is the evolution of metrics as a program matures. The progression moves from simply counting activities to demonstrating strategic business value.
- CTI1: Foundational (Measuring Effort)
- Focus: Metrics are primarily quantitative, tracking "throughput or level of effort." They prove the team is busy but result in "limited measurable value."
- Examples: Number of ad hoc alerts generated; percentage of IoCs gathered from external sources.
- CTI2: Advanced (Measuring Impact)
- Focus: Metrics become more qualitative and are improved by stakeholder feedback. They demonstrate how CTI impacts decisions and operations, providing "moderately measurable value."
- Examples: Reduction in Mean-Time-To-Detect (MTTD); estimated cost savings from fraud prevention; qualitative stakeholder feedback.
- CTI3: Leading (Measuring Outcomes)
- Focus: Metrics are comprehensive, aligned with business outcomes, and explicitly map to future actions. They assess the overall "effectiveness" of the program and its role in strategic decisions.
- Examples: Reduction in dwell time based on threat-informed detections; number of strategic asset acquisitions vetted against CTI risk assessments; correlation between intelligence-led actions and risk reduction.
Domain-Specific Metric Application
While the general progression from effort to outcomes is universal, the specific subjects of measurement are tailored to the mission of each of the 11 domains.
- ASSET: Focuses on inventory accuracy, attack surface exposure, and lifecycle decisions. (e.g., "Percentage of strategic asset acquisitions vetted against CTI risk assessments").
- THREAT: Focuses on detection logic efficacy, patch prioritization, and predictive capability. (e.g., "Percentage of adversary infrastructure...proactively identified and blocked").
- RISK: Focuses on quantification, framework alignment, and decision support. (e.g., "Number of risk-based decisions...where prioritization is based on the cyber threat landscape").
- ACCESS: Focuses on credential hygiene, authentication policies, and identity threats. (e.g., "MTTR [Mean Time To Respond to] identity-related threats after CTI alerting").
- SITUATION: Focuses on threat landscape completeness and the ROI of data sources. (e.g., "Reduction in security incidents through improved CTI-based situational forecasting").
- RESPONSE: Focuses on speed (dwell time), enrichment, and playbook efficacy. (e.g., "Percentage of IR case escalations that received CTI enrichment").
- THIRD-PARTIES: Focuses on supply chain exposure and vendor notification. (e.g., "Number of times CTI detected a third-party compromise before receiving notification from the third party").
- FRAUD: Focuses on financial loss prevention, takedowns, and brand protection. (e.g., "Percentage of fraud attempts reduced through CTI-informed automation").
- WORKFORCE: Focuses on human behavior, training relevance, and cultural awareness. (e.g., "Measured increase in security awareness among employees due to CTI-driven training").
- ARCHITECTURE: Focuses on design influence, blueprints, and structural resilience. (e.g., "Percentage of architecture design reviews that cite CTI inputs").
- PROGRAM: Focuses on CTI function governance, budget, and strategic alignment. (e.g., "Variance in CTI program budget and leadership support from year to year").
--------------------------------------------------------------------------------
Architecting a Cyber Threat Profile
A critical activity outlined in the CTI-CMM is the creation of a Cyber Threat Profile, defined as a characterization of the likely intent, capability, and targets for threats to the organization. This profile bridges the gap between raw intelligence and strategic risk management.
1. Gather Diverse Data Sources: A robust profile requires fusing information from multiple sources, including:
- Open and commercial intelligence
- Vulnerability and attack surface intelligence
- Cybercriminal underground activities
- Breach events and identity intelligence
2. Characterize and Rank Threats: The profile must go beyond a simple list to a prioritized ranking of threat groups and trends relevant to the organization's sector and locations. For each threat, three elements must be evaluated:
- Intent: What they want.
- Capability: What they can do.
- Targets: What they are aiming for.
3. Align with Risk Management: The profile must be integrated with existing risk frameworks (e.g., NIST 800-30, FAIR). At a leading maturity level (CTI3), the profile directly drives the prioritization of risk-based decisions and is integrated into risk management dashboards.
4. Operationalize the Profile: A mature profile is not a static document; it is regularly updated and drives operations by:
- Supporting gap analysis to prioritize detection controls against ranked threats.
- Providing prescriptive analysis to stakeholders with recommended actions.
- Informing offensive security and risk management with contemporary threat knowledge.
By building and maintaining this profile, a CTI program enables the risk department to accurately assess impacts, align with the organization's risk appetite, and implement controls that address the most severe and likely threats first.