Espionage in Europe (2008–2024): Motives, Methods, and Typologies
Executive Summary
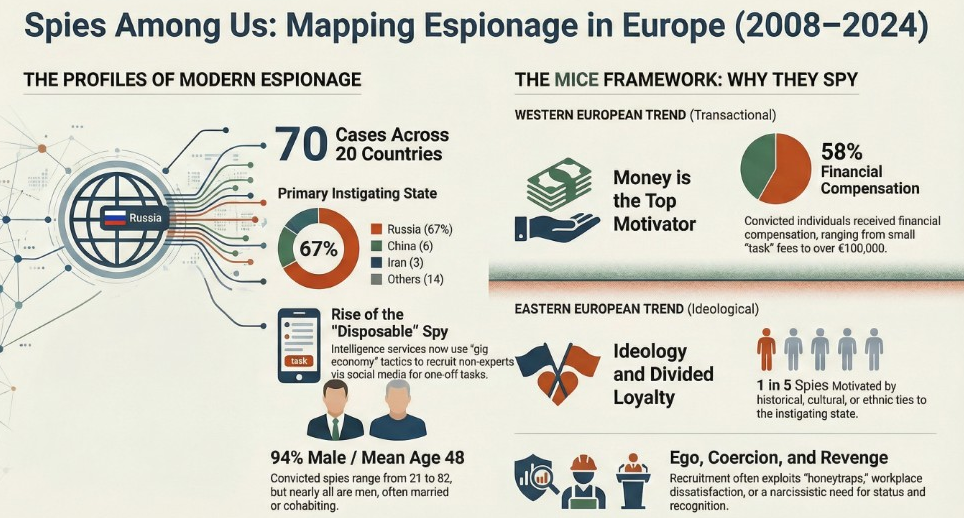
This briefing document synthesizes findings from a comprehensive study of 70 individuals convicted of espionage across 20 European countries between 2008 and 2024. The data reveals that espionage has evolved from a residual Cold War practice into a central element of contemporary European security, intensified by Russia’s 2014 annexation of Crimea and the 2022 full-scale invasion of Ukraine.
Critical Takeaways:
- Primary Instigator: Russia is the dominant threat, responsible for 47 of the 70 identified cases (approximately 67%). Other significant actors include China, Iran, and Turkey.
- Geographical Overrepresentation: The Baltic states, particularly Estonia, show the highest number of convictions. Conversely, Western European countries report fewer convictions, which may indicate differences in counterintelligence focus rather than a lack of activity.
- Shifting Agent Profiles: While "traditional insiders" (those with security clearances) still comprise nearly half of the cases, there is a marked rise in "disposable" and "single-use" agents recruited for low-level tasks via digital platforms.
- The Continental Divide: Motivation for espionage varies geographically. In Eastern Europe, historical and cultural ties to Russia drive "Ideologist" spies. In Western Europe, motives are more transactional, driven by financial gain or personal dissatisfaction.
- Digitalization of Tradecraft: Traditional human intelligence (HUMINT) is increasingly "cyber-enabled," utilizing social media for recruitment (LinkedIn, Telegram) and encrypted software for communication, though physical methods like dead drops and face-to-face meetings persist.
--------------------------------------------------------------------------------
1. The Geopolitical Context of Modern Espionage
The European espionage landscape is defined by a "New Cold War" dynamic. While Western intelligence services reoriented toward counterterrorism in the 1990s, Russian intelligence—inheriting the ethos of the KGB—maintained a permanent "wartime footing."
Key State Actors
State | Primary Focus/Methodology | Organizations Involved |
Russia | Operational/tactical intel; infrastructure; military logistics. | GRU (Military), FSB (Domestic), SVR (Foreign) |
China | Science, technology, industry, and intellectual property. | MSS (State Security), PLA (Military Intel) |
Iran | Mapping the Iranian diaspora; technological/military intel. | MOIS (Intelligence), IRGC (Revolutionary Guard) |
Turkey | Monitoring political opposition and extremist organizations. | MIT (National Intelligence) |
--------------------------------------------------------------------------------
2. Typologies of the Modern Spy
The study identifies ten distinct typologies of spies operating in Europe, moving beyond the stereotype of the high-level infiltrator.
- The Traditional Insider: Military or intelligence officers with privileged access to classified data.
- The Ideologist: Driven by nationalism or devotion to the instigating state; common in the Baltics.
- The Observer: Tasked with low-level monitoring, such as photographing NATO ports or rail movements.
- The Disposable: Low-value assets recruited for one-off missions, often acting unknowingly.
- The Intermediary: Facilitators who manage logistics or act as "runners" (e.g., family members of the primary spy).
- The Multi-criminal: Individuals engaged in espionage alongside smuggling, sabotage, or drug trafficking.
- The Specialist: Experts (electricians, interpreters, or researchers) who lack security clearance but have physical or technical access.
- The Mobile Spy: Non-nationals operating across borders within the Schengen area to complicate attribution.
- The Connected Agent: Targeted through cultural, religious, or historical ties to the antagonistic state.
- Espionage Rings: Coordinated networks of operatives (e.g., the North Macedonian ring of 2014).
--------------------------------------------------------------------------------
3. The Psychology and Motivation of Espionage
The "MICE" framework (Money, Ideology, Coercion, Ego) remains the primary tool for understanding why European citizens spy.
The Continental Divide of Motives
- Eastern Europe (Baltic States): Recruitment often exploits "divided loyalties" among ethnic Russians or Russian speakers. Intelligence services leverage nostalgia for the Soviet era and propaganda regarding the alienation of minorities.
- Western Europe: Espionage is more frequently "money-driven." Recruits are often "Disposables" or insiders motivated by debts, luxurious lifestyles, or personal dissatisfaction.
Primary Drivers
- Money: 41 out of 70 convicted individuals received financial compensation. Payments range from small amounts for "single-use" tasks to over EUR 100,000 for high-level military data.
- Ideology: Potent among those with cultural ties to Russia or those adhering to "us vs. them" narratives.
- Coercion: Includes "honeytraps" (romantic entrapment) and "kompromat" (blackmail). In one instance, an Estonian officer was coerced into spying after a fabricated rape allegation in Russia.
- Ego/Discontentment: Spies often exhibit "wounded pride" or a need for recognition. Disappointment with career progress is a recurrent factor (e.g., a British embassy security guard becoming depressed during COVID-19 lockdowns).
--------------------------------------------------------------------------------
4. Recruitment and Operational Methods
The "toolbox" of recruitment has expanded to include both classical long-term cultivation and "fast-food" digital recruitment.
Digital Recruitment Platforms
- LinkedIn: Used by Chinese intelligence to target thousands of German citizens by posing as academics or consultants.
- Telegram: Russian intelligence utilizes automated bots (e.g., "Privet Bot") to recruit young Europeans for sabotage or monitoring tasks in exchange for cryptocurrency.
- Social Media Bubbles: The isolation of the COVID-19 pandemic fostered "information bubbles," making individuals more susceptible to digital manipulation.
Operational Tradecraft
- Collection: Photography of computer screens, military buildings, and equipment remains the most common method. USB drives and scanners are used to copy sensitive files.
- Communication: Shifted toward encrypted platforms like Signal or Telegram, though traditional "dead mailboxes" (draft emails accessed by two parties) and radio/satellite transmissions are still in use.
- Physical Exchange: "Dead drops" (e.g., hiding envelopes in library ceiling tiles or rubbish bins) continue to be used to transfer physical items and cash.
--------------------------------------------------------------------------------
5. Targets of Espionage
While military objectives are the most frequent targets, the appetite of antagonistic states is described as "omnivorous."
- Military: Information on NATO shipments to Ukraine, troop movements, and weapon specifications (artillery, munitions).
- Critical Infrastructure: Energy and electricity supply, oil and gas infrastructure, and transport nodes.
- Technical/Dual-Use: Automotive software, semiconductors, and microchips that have both civilian and military applications.
- Political: EU deliberations on sanctions, Arctic disputes, and the mapping of political opposition figures.
- Counterintelligence: Infiltration of security services to determine what they know about foreign intelligence operations.
--------------------------------------------------------------------------------
6. Demographics and Statistical Overview
Data derived from the 70 convicted cases provides a profile of the "typical" convicted spy in Europe:
- Gender: Overwhelmingly male (only 4 women identified).
- Age: Mean age at conviction is 48; however, recruitment begins as early as 17.
- Education: Varies from basic schooling to advanced doctoral research and specialized military training.
- Employment: 72.6% were in civilian service, while 16.1% were in military service.
- Cooperation: Approximately one in three spies worked with at least one other person (e.g., spouse or colleague).
Conviction Count by Country (Top 5)
Country | Convictions |
Estonia | 19 |
Germany | 8 |
North Macedonia | 8 |
Lithuania | 7 |
Latvia | 6 |
--------------------------------------------------------------------------------
7. Strategic Implications for Counterintelligence
The shift toward "disposable" agents and "single-use" missions poses a significant challenge for detection, as these individuals often lack national ties to the operational area and may enter/exit a country quickly.
Key Conclusions:
- Legislative Gaps: Many European legal frameworks are struggling to keep pace with modern digital espionage. Prosecution is often avoided to prevent the disclosure of further secrets.
- The Importance of Transparency: Publicizing convictions serves as a deterrent and builds domestic resilience against foreign influence.
- Whole-of-Society Threat: Adversaries now target "ordinary" citizens and non-experts in civilian sectors (healthcare, green tech, academia) who have access to sensitive but not necessarily classified data.
- Deterrence through Resilience: Internal organizational cultures that support employees and protect whistleblowers are critical to preventing recruitment based on personal crisis or discontentment.





