Google Dismantles GRIDTIDE: Inside the Decade-Long Chinese Espionage Campaign Targeting Telcos and Governments Worldwide

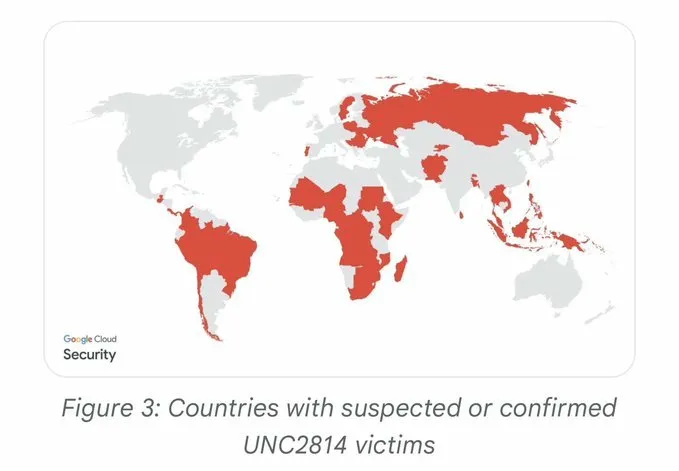
In one of the most significant cybersecurity disruptions of 2026, Google's Threat Intelligence Group (GTIG) and Mandiant have taken down a sprawling global espionage network with confirmed intrusions in 53 organizations across 42 countries — and suspected reach into at least 20 more. The campaign, attributed to a suspected People's Republic of China (PRC)-nexus threat actor designated UNC2814, had been operating quietly since at least 2017, embedding itself inside telecommunications providers and government agencies across Africa, Asia, and the Americas.
This wasn't Salt Typhoon. This was something else entirely — and it had been hiding in plain sight.
Who Is UNC2814?
UNC2814, also publicly tracked under the alias "Gallium," is a sophisticated and persistent cyber espionage actor that GTIG has monitored since 2017. The group maintains a distinct profile from other publicly reported PRC-nexus campaigns, including the high-profile Salt Typhoon telco intrusions that grabbed headlines in 2024 and 2025. According to Google, UNC2814 uses different victims, different TTPs, and has built its own unique toolset — chief among them a C-based backdoor that Google's FLARE team named GRIDTIDE.
The group's primary targets are telecommunications providers and government organizations, and its operational tradecraft reflects years of refinement: patient, stealthy, and deeply embedded in victim environments. When GTIG executed the disruption on February 18, 2026, confirmed intrusions had been established in 42 countries across four continents.
That is not a spray-and-pray operation. That is a decade of deliberate, disciplined intelligence collection.
The GRIDTIDE Backdoor: Google Sheets as a Weapon
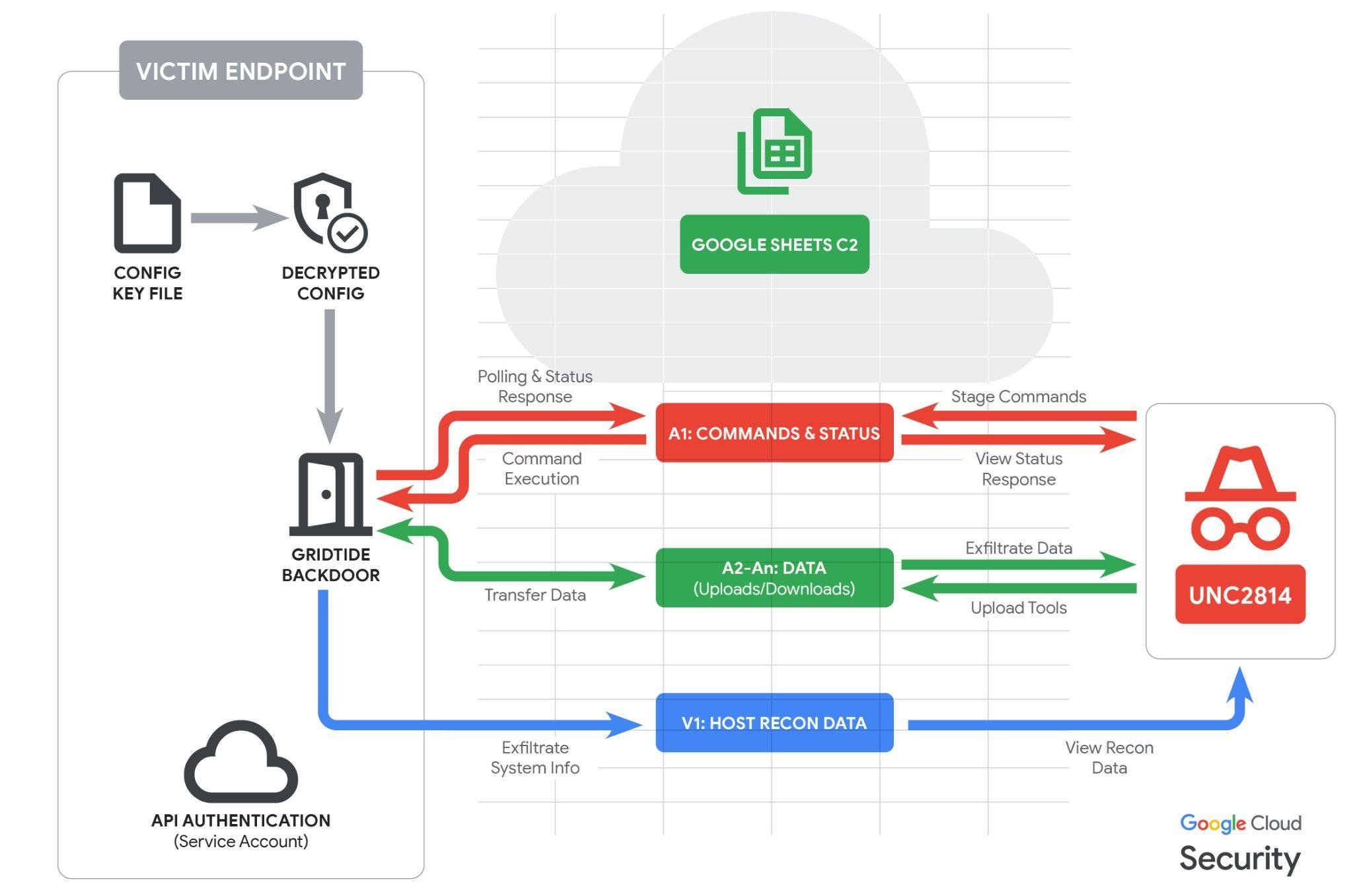
The technical centerpiece of UNC2814's recent campaign is GRIDTIDE — a lean, capable C-based backdoor that executes shell commands, uploads files to victim hosts, and exfiltrates data from compromised systems. What makes GRIDTIDE particularly clever — and particularly difficult to detect — is its choice of command-and-control (C2) infrastructure: Google Sheets.
Rather than communicating with traditional C2 servers that can be blocklisted or sinkholes, GRIDTIDE leverages the legitimate Google Sheets API. The malware treats a Google Spreadsheet not as a document, but as a communication channel. Commands arrive in cell A1. Results get posted back. Victim host metadata gets written to cell V1. File transfers move across the A2:An range in 45-KB fragments. The entire exchange looks, at the network layer, like any other SaaS API call.
This is not a vulnerability in Google Sheets. Google has been explicit about that. The malware simply abuses a platform that works correctly — bending legitimate cloud functionality into a covert channel that blends into normal enterprise traffic.
GRIDTIDE also covers its tracks on initialization, wiping the first 1,000 rows of its spreadsheet across columns A through Z using the batchClear API method. Every session starts clean. All prior command history is gone before a new operator session begins.
How GRIDTIDE Gets Configured
Before GRIDTIDE can communicate with its C2 spreadsheet, it reads a 16-byte cryptographic key from a separate file on the host. It uses that key to decrypt an AES-128 CBC encrypted configuration blob containing:
- A Google Service Account credential associated with UNC2814's Sheets document
- The private key for that service account
- The target Google Spreadsheet ID
From there, GRIDTIDE authenticates via the Google Sheets API, fingerprints the host (username, hostname, OS, local IP, timezone, language), and posts that beacon to cell V1. It then begins polling cell A1 for operator commands on a one-second loop, backing off to a randomized 5–10 minute sleep interval after 120 failed polls — a simple but effective anti-noise measure for when operators aren't actively tasked on a target.
The C2 Command Syntax
Commands follow a four-part format: <type>-<command_id>-<arg1>-<arg2>. The operator sends type C (Client) instructions; the malware responds with type S (Server) acknowledgments. Three core command types are supported:
- C (Command): Execute a Base64-encoded shell command, redirect output back to the spreadsheet
- U (Upload): Reconstruct and write a file to a local path from spreadsheet cell data
- D (Download): Read a local file and exfiltrate it in 45-KB fragments into the spreadsheet range
All data in transit is encoded using URL-safe Base64 (substituting - and _ for the standard + and /), adding another layer of obfuscation against content inspection.
Initial Detection: How Mandiant Found It
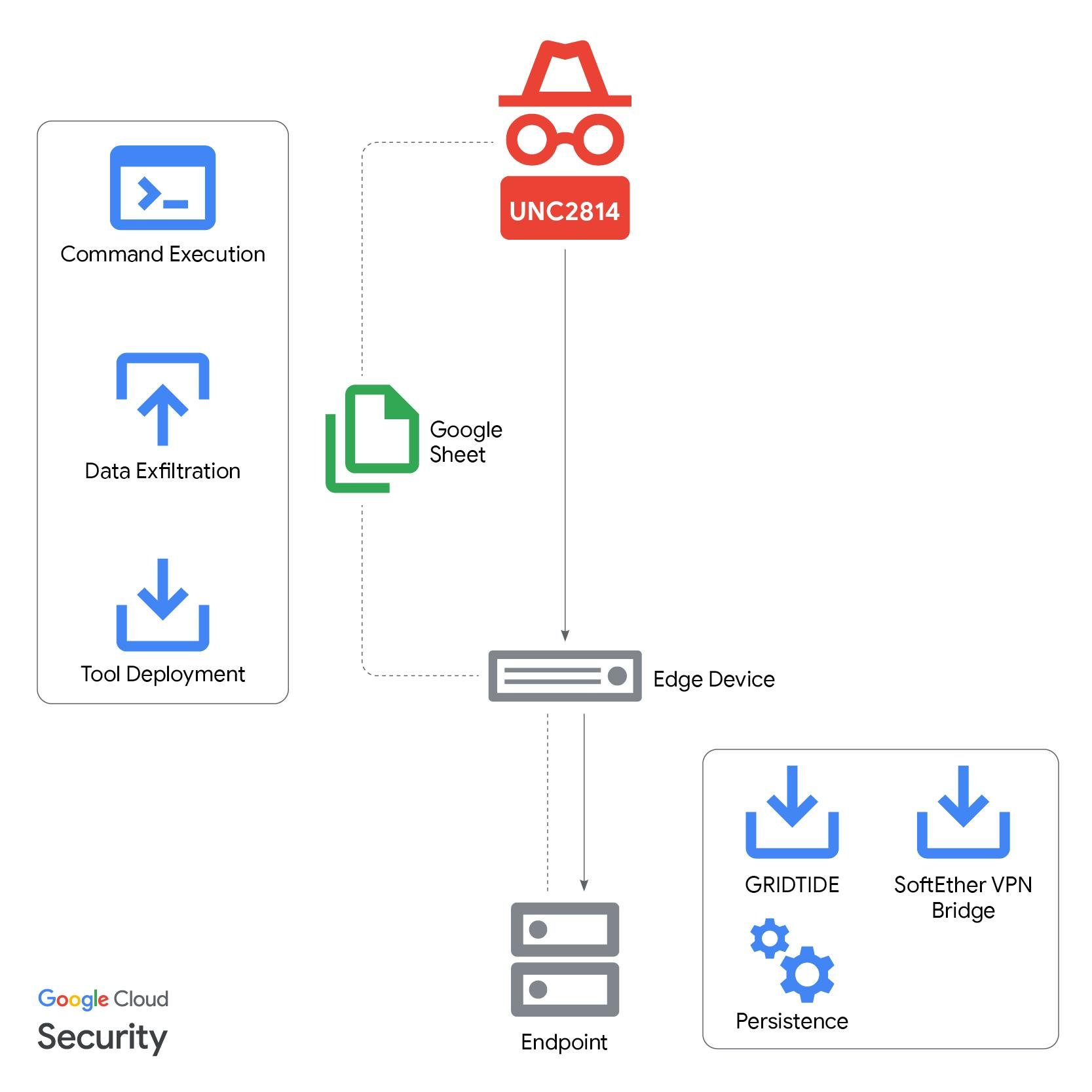
The intrusion that cracked this campaign open was found on a CentOS server during continuous monitoring through Google Security Operations. The alert flagged an unusual process tree: a binary at /var/tmp/xapt spawning a shell and executing sh -c id 2>&1 — a classic post-exploitation move to confirm root privilege escalation. The binary name xapt was almost certainly chosen to impersonate the legacy apt package management tool used in Debian-based Linux distributions.
From there, Mandiant analysts traced the full post-compromise playbook:
- Lateral movement via SSH using a service account
- Persistence established by registering GRIDTIDE as a systemd service at
/etc/systemd/system/xapt.service, launching from/usr/sbin/xapt - Initial execution via
nohup ./xaptto survive session termination - Tunneling established via SoftEther VPN Bridge, an outbound encrypted connection to UNC2814 infrastructure — with configuration metadata suggesting this specific VPN setup had been in active use since July 2018
That last data point is remarkable. This wasn't a fresh implant. This was entrenched infrastructure that had been operational for nearly eight years.
What They Were After: PII and Surveillance at Scale
In at least one confirmed intrusion, GRIDTIDE was deployed onto a system containing:
- Full legal names
- Phone numbers
- Dates and places of birth
- Voter ID numbers
- National ID numbers
Google's assessment aligns this targeting with telecommunications-focused espionage objectives: identify, locate, and surveil persons of interest. Historical PRC-nexus intrusions into telcos have resulted in the theft of call data records, unencrypted SMS messages, and in the worst cases, abuse of lawful intercept systems — the same infrastructure telecommunications providers use to respond to court-ordered law enforcement wiretaps.
GTIG did not directly observe exfiltration during this campaign's disruption window, but the access UNC2814 had achieved would have enabled exactly that kind of surveillance capability. The targets — telcos and government entities in 42 confirmed countries — represent the infrastructure backbone of national communications systems worldwide.
"This was a vast surveillance apparatus used to spy on people and organizations throughout the world," said John Hultquist, Chief Analyst at Google Threat Intelligence Group.
The Disruption: What Google Did
GTIG's response was coordinated and comprehensive. Working with unnamed partners, Google executed the following actions:
Eliminating GRIDTIDE Access: All Google Cloud Projects controlled by UNC2814 were terminated, severing the actor's ability to issue commands through the Google Sheets C2 infrastructure across all compromised environments simultaneously.
Infrastructure Takedown: Known UNC2814 domains and IP infrastructure were identified and disabled. Historical domains were sinkholed to cut off any remaining active connections or dormant implants calling home.
Account Disruption: Attacker Google accounts, service accounts, and associated Google Workspace access were fully disabled. The Google Sheets documents used for C2 are now inaccessible.
Victim Notifications: Formal notifications are being issued to all 53 confirmed victim organizations, with active support being provided.
IOC Release: A comprehensive set of indicators — including SHA256 hashes, IP addresses, C2 domains, User-Agent strings, API endpoint patterns, and a YARA detection rule — has been publicly released to enable the broader defender community to hunt for this activity in their own environments.
GTIG published over 150 C2 domains, 25+ attacker IP addresses, and specific file hashes for GRIDTIDE and its associated SoftEther VPN Bridge components. Detection rules for Google SecOps are also live, including behavioral detections for suspicious Google Sheets API connections from non-browser processes.
Why This Matters for Defenders
The GRIDTIDE campaign is a clear demonstration of where enterprise detection has a structural gap: legitimate cloud API abuse is extremely hard to detect using traditional network monitoring approaches.
If your network security tools are looking for connections to known-bad IP addresses or suspicious domains, they would have seen nothing unusual in GRIDTIDE traffic. All outbound connections went to sheets.googleapis.com:443 — a domain your organization almost certainly has whitelisted across every firewall and proxy in your environment.
Detecting this class of threat requires behavioral analytics: looking for non-browser processes initiating connections to Sheets API endpoints, monitoring for unusual batchClear or batchUpdate patterns, or identifying anomalous configuration file creation in paths like /var/tmp/, /usr/sbin/, or /etc/systemd/system/.
For organizations in telecommunications or government sectors, this campaign should trigger an immediate review of:
- Linux server process telemetry — especially in
/var/tmp/and similar staging directories - Systemd service creation events — unauthorized new services are a high-fidelity persistence indicator
- Outbound HTTPS from server processes to googleapis.com — particularly
batchClear,batchUpdate, andvalueRenderOption=FORMULAendpoints - SoftEther VPN Bridge artifacts — specifically
hamcore.se2andvpn_bridge.configfiles - The GRIDTIDE YARA rule published by GTIG
The IOC list Google has published is long and should be ingested into your threat intelligence platform immediately. The C2 domains span dozens of dynamic DNS providers and represent years of accumulated infrastructure.
The Bigger Picture
UNC2814's GRIDTIDE campaign is the kind of operation that gets built over a decade — quietly expanding, carefully maintaining persistence, and collecting intelligence at a scale that only becomes visible when you zoom out and look at the full map. Confirmed or suspected victims in over 70 countries. Telecommunications infrastructure. Government networks. Personal identification data.
Google's decision to execute a mass simultaneous disruption — rather than quietly notifying individual victims — reflects the scale of the threat and the difficulty of cleaning up one victim at a time when an adversary has this kind of global footprint. The tradeoff is that UNC2814 now knows its infrastructure is burned. Google has acknowledged as much: "We expect that UNC2814 will work hard to re-establish their global footprint."
The clock is already running on the next campaign.
Key IOCs for Immediate Detection
GRIDTIDE SHA256 Hashes:
xapt(GRIDTIDE backdoor):ce36a5fc44cbd7de947130b67be9e732a7b4086fb1df98a5afd724087c973b47xapt.cfg(key file):01fc3bd5a78cd59255a867ffb3dfdd6e0b7713ee90098ea96cc01c640c6495ebxapt.service(persistence):eb08c840f4c95e2fa5eff05e5f922f86c766f5368a63476f046b2b9dbffc2033
Key Attacker IPs:
130.94.6.228— hosted GRIDTIDE download archives38.180.205.14— verified HTTPS access target38.60.194.21— SoftEther VPN server
GRIDTIDE User-Agents:
Google-HTTP-Java-Client/1.42.3 (gzip)Directory API Google-API-Java-Client/2.0.0 Google-HTTP-Java-Client/1.42.3 (gzip)
Suspicious API Patterns (Google SecOps UDM):
target.url = /sheets\.googleapis\.com/
(target.url = /batchClear/ OR target.url = /batchUpdate/ OR target.url = /valueRenderOption=FORMULA/)
principal.process.file.full_path != /chrome|firefox|safari|msedge/
The full IOC collection is available via Google Threat Intelligence for registered users.
Sources: Google Threat Intelligence Group / Mandiant — "Exposing the Undercurrent: Disrupting the GRIDTIDE Global Cyber Espionage Campaign" (February 25, 2026); Reuters reporting by A.J. Vicens (February 25, 2026)





