Health-ISAC 2026 Report: Healthcare Sector Faces Existential Cybersecurity Crisis as Ransomware, Supply Chain Attacks, and AI-Powered Threats Surge
Health-ISAC's newly released 2026 Global Health Sector Threat Landscape Report paints a dire picture of an industry under siege. With 455 ransomware incidents tracked globally throughout 2025 and sophisticated supply chain compromises enabling access at unprecedented scale, healthcare organizations face a perfect storm of escalating threats, inadequate defenses, and potentially life-threatening operational disruptions. The report identifies ransomware groups Qilin, INC Ransom, and SAFEPAY as the most active in targeting health entities, while warning that AI-enabled tactics are poised to dramatically escalate the threat landscape in 2026.
Executive Summary
The Health-ISAC report arrives at a critical juncture for global healthcare cybersecurity. Unlike breaches in retail or hospitality sectors where the primary harm is financial and reputational, healthcare cyberattacks directly threaten patient safety, clinical operations, and in extreme cases, human life. The report's findings make clear that healthcare has become the sector of choice for profit-driven ransomware operators precisely because the consequences of disruption are so severe—creating maximum pressure to pay ransoms.

Key findings include:
- 455 ransomware incidents targeting health organizations globally in 2025
- Escalating supply chain compromise, with attackers increasingly targeting vendors to gain access at scale
- Sophisticated social engineering evolution, including QR code phishing (quishing), ClickFix, and FileFix techniques that bypass traditional security awareness training
- AI-enabled attack tactics emerging as a major concern for 2026
- Survey of 250 health executives revealing ransomware, phishing, third-party compromise, and newly discovered software flaws as top concerns
Health-ISAC Chief Security Officer Errol Weiss captured the existential nature of the threat:
"The Health sector has become one of the most targeted sectors in the world, not because it's the easiest, but because the consequences of disruption are so severe. This report is a clear warning: cyber threats are no longer isolated events. They represent life-saving business continuity crises that can impact patient care, staff safety, and public trust."
The Ransomware Epidemic: 455 Incidents and Counting
By the Numbers
455 ransomware incidents globally in 2025 represents not just the volume of attacks but the relentless, sustained pressure facing healthcare organizations of all sizes and types:
- Hospitals and health systems
- Outpatient clinics and medical practices
- Pharmaceutical companies
- Medical device manufacturers
- Health insurance companies and TPAs
- Clinical laboratories and diagnostic centers
- Telehealth platforms
- Medical research institutions
This figure likely represents significant underreporting, as:
- Many organizations don't detect breaches promptly
- Some incidents are resolved without public disclosure
- Private practices and smaller clinics often lack reporting obligations
- International incidents may not reach Health-ISAC's tracking systems
The Most Active Threat Actors
The report identifies three ransomware groups as particularly prolific in healthcare targeting:
Qilin Ransomware
Profile:
Russian-speaking ransomware-as-a-service (RaaS) operation active since mid-2022, known for:
- Sophisticated double extortion tactics
- Targeting of large healthcare systems with capacity to pay substantial ransoms
- Rapid encryption using modern cryptographic techniques
- Professional negotiation tactics and leak site management
Notable Healthcare Attacks:
- Synnovis (UK pathology services provider, June 2024): Disrupted blood testing across multiple London hospitals, forcing postponement of thousands of procedures
- Octapharma Plasma (2024): Compromised blood plasma provider, affecting supply chain
Why Healthcare?
Qilin specifically targets organizations where operational disruption creates maximum pressure. Healthcare's inability to tolerate downtime makes it an ideal target.
INC Ransom
Profile:
Relatively newer operation (emerged 2024) that has rapidly built a substantial healthcare portfolio through:
- Aggressive targeting of mid-sized healthcare organizations
- Exploitation of known vulnerabilities in medical devices and healthcare IT systems
- Focus on regional hospital systems and specialty practices
Tactics:
- Initial access through phishing and compromised credentials
- Rapid lateral movement to identify and prioritize clinical systems
- Exfiltration of both patient data (for extortion) and operational data (to demonstrate impact)
SAFEPAY Ransomware
Profile:
Lesser-known group with specific focus on financial disruption:
- Targets healthcare billing and revenue cycle systems
- Demands ransoms tied to organizational revenue
- Threatens exposure of billing records and patient financial data

Impact:
Beyond operational disruption, SAFEPAY attacks can cripple healthcare organization finances by:
- Preventing claim submission to insurers
- Exposing patient payment information
- Disrupting accounts receivable collections
Why Healthcare Is Target #1
The report emphasizes that healthcare targeting is no accident:
1. Maximum Pressure to Pay
When ICU monitors stop working, operating rooms go offline, or EHRs become inaccessible, patient lives are at immediate risk. This creates enormous pressure to pay ransoms quickly rather than endure lengthy recovery processes.
2. High-Value Data
Healthcare records are worth 10-50x more than credit card numbers on dark web markets because they enable:
- Medical identity theft (obtaining prescriptions, procedures, insurance benefits)
- Insurance fraud
- Blackmail (sensitive diagnoses, treatments, conditions)
- Targeted phishing based on medical conditions
3. Limited Security Maturity
Healthcare organizations face unique security challenges:
- Legacy medical devices that cannot be patched
- Complex interconnected systems (EHR, billing, imaging, pharmacy, etc.)
- 24/7 operations preventing maintenance windows
- Limited IT security budgets compared to financial services or technology sectors
- Shortage of healthcare-specific security expertise
4. Regulatory Pressure
HIPAA and international equivalents create compliance obligations that make data breaches particularly painful, forcing organizations to:
- Notify affected patients
- Offer credit monitoring
- Face potential regulatory fines
- Manage reputational damage
5. Supply Chain Complexity
Modern healthcare depends on:
- Electronic health record vendors (Epic, Cerner/Oracle, Meditech)
- Medical device manufacturers (GE Healthcare, Philips, Siemens)
- Revenue cycle management companies
- Clinical laboratories
- Imaging centers
- Pharmacy benefit managers
- Telehealth platforms
Each vendor represents a potential entry point to multiple downstream healthcare organizations.

Supply Chain Compromise: The Multiplier Effect
The Health-ISAC report emphasizes growing exploitation of third-party suppliers as a force multiplier for attackers:
"The findings reinforce a critical reality: even organizations with strong internal security may remain vulnerable through a partner, platform, managed service provider, or widely used software solution."
Why Supply Chain Attacks Work
Access at Scale
Instead of attacking 100 hospitals individually, attackers compromise one EHR vendor or MSP with access to all 100, gaining:
- Simultaneous access to multiple targets
- Trusted relationships that bypass security controls
- Deep knowledge of target systems from vendor access
- Ability to deploy malware disguised as legitimate updates
Reduced Detection Risk
Vendor access appears legitimate:
- Security tools expect vendor connections
- Vendor actions don't trigger anomaly alerts
- Lateral movement looks like normal vendor activity
- Data exfiltration can be disguised as vendor data synchronization
Shared Vulnerabilities
Vendors often deploy similar configurations across customers:
- Same software versions with same vulnerabilities
- Standard access methods (VPN, remote desktop, API keys)
- Common security control gaps
- Predictable network architectures
Recent Healthcare Supply Chain Incidents
Change Healthcare / UnitedHealth Group (2024)
Perhaps the most devastating healthcare cyberattack in history:
- BlackCat/ALPHV ransomware group compromised Change Healthcare, a subsidiary of UnitedHealth Group
- Change Healthcare processes ~15 billion healthcare transactions annually
- Attack disrupted prescription processing, claims submissions, and payment processing across thousands of healthcare organizations
- Estimated impact: $872 million in costs for UnitedHealth, far greater for affected provider organizations
- Demonstrated catastrophic risk of concentration in healthcare infrastructure
Synnovis (June 2024)
- Qilin ransomware compromised UK pathology services provider
- Disrupted blood testing services across multiple London hospitals
- Forced postponement of thousands of surgical procedures and cancer treatments
- Took months to fully restore services
Octapharma Plasma
- Qilin compromise affected blood plasma provider
- Supply chain implications for hospitals dependent on plasma products
Philips Respironics (ongoing)
While not a ransomware attack, the massive recall and security vulnerabilities in Philips sleep apnea devices demonstrate healthcare supply chain fragility
These incidents underscore a terrifying reality: a single vendor compromise can cascade across the entire healthcare ecosystem.
The Evolution of Social Engineering: Beyond Traditional Phishing
The Health-ISAC report highlights sophisticated deception tactics that render traditional security awareness training increasingly obsolete:
QR Code Phishing (Quishing)
How It Works:
- Attackers send emails or physical mail containing malicious QR codes
- Victims scan codes with personal smartphones
- Codes redirect to credential harvesting sites, malware downloads, or payment scams
- Bypasses email security controls that scan links but not images
Why Healthcare Is Vulnerable:
- COVID-19 normalized QR code usage for patient check-in, vaccine verification, etc.
- Healthcare workers frequently use personal devices for convenience
- Medical environments often require quick scanning of patient wristbands, medication, etc.—creating "scan fatigue"
Example Attack:
Employee receives email claiming to be from HR regarding benefits enrollment. QR code appears to link to benefits portal. Employee scans code with personal phone. Site harvests hospital network credentials. Attacker uses credentials to access EHR from outside network.

ClickFix Attacks
How It Works:
- Malicious websites or emails present fake error messages (e.g., "Your browser needs an update" or "Plugin required to view document")
- User clicks "Fix" button or downloads "required" plugin
- Click installs malware, ransomware, or info-stealer
Why It Bypasses Traditional Training:
- Doesn't follow typical phishing patterns (spelling errors, urgency, suspicious links)
- Appears to be legitimate technical requirement
- Exploits users' desire to complete tasks quickly
Healthcare Example:
Physician receives email with lab results attachment. Clicking attachment displays message: "PDF viewer plugin required. Click to install." Doctor, focused on patient care, clicks install. Ransomware deploys across hospital network.
FileFix Attacks
How It Works:
- Similar to ClickFix but focuses on document "corruption"
- Users receive documents that appear to be corrupted or unreadable
- Error message offers to "repair" or "recover" file
- Repair process installs malware
Healthcare Context:
Medical imaging files (DICOM), lab results (HL7), or EHR exports often have compatibility issues. Healthcare workers are accustomed to file format problems and may readily click "fix" buttons to access patient data.
Why These Tactics Work Against Healthcare
1. Time Pressure
Healthcare environments operate under constant time pressure. Staff need to access patient information immediately, creating urgency that undermines security caution.
2. Complexity of Healthcare IT
With dozens of different systems, frequent compatibility issues, and regular updates, healthcare workers expect technical problems and "fix" prompts.
3. Patient Care Prioritization
When security creates friction for patient care, healthcare workers find workarounds—often including clicking through security warnings.
4. BYOD and Personal Device Use
Healthcare workers frequently use personal smartphones for convenience, bypassing enterprise security controls.
5. Traditional Training Ineffectiveness
Standard "don't click suspicious links" training doesn't address:
- QR codes that bypass link scanning
- Fake technical error messages
- Attacks delivered via legitimate platforms (SharePoint, DocuSign, etc.)

The AI Threat: 2026's Emerging Crisis
Health-ISAC's survey of 250 health executives and cybersecurity professionals revealed growing concern around AI-enabled tactics, with 66% anticipating significant AI impact on cybersecurity in 2026—yet only 37% report having processes to assess AI tool security before deployment.
This gap between recognition and preparation could prove catastrophic.
AI-Powered Threat Capabilities
1. Automated Vulnerability Discovery
AI can:
- Scan healthcare organizations' external attack surfaces at scale
- Identify vulnerable medical devices, VPN concentrators, web applications
- Prioritize targets based on likely value and exploitability
- Generate custom exploits for identified vulnerabilities
2. Adaptive Malware
Machine learning enables malware that:
- Modifies behavior based on environment (evading sandboxes, signature detection)
- Learns from failed attempts and adjusts tactics
- Identifies high-value systems and prioritizes them
- Mimics legitimate traffic patterns to avoid detection
3. Deepfake Social Engineering
Generative AI enables:
- Voice cloning of hospital executives for phone-based attacks (e.g., CFO calling to authorize wire transfers)
- Video deepfakes for virtual meetings (e.g., "CEO" on Zoom call requesting privileged access)
- Personalized phishing at scale using data scraped from social media, hospital websites, etc.
4. AI-Powered Reconnaissance
Large language models can:
- Process massive amounts of open-source intelligence (OSINT)
- Identify employees, their roles, relationships, and communication patterns
- Generate organizational charts and decision-making structures
- Craft perfectly tailored spear-phishing based on individual targets
5. Automated Attack Orchestration
AI can manage complex multi-stage attacks:
- Coordinate simultaneous exploitation of multiple systems
- Adapt in real-time to defender responses
- Optimize timing and sequencing of attack phases
- Manage dozens or hundreds of concurrent campaigns
Healthcare-Specific AI Threat Scenarios
Scenario 1: The AI-Powered Physician Impersonation
- Attackers use publicly available physician information (credentials, specialties, publications)
- AI generates deepfake video call appearing to be attending physician
- "Physician" calls pharmacy requesting urgent medication change for critical patient
- Pharmacy, trusting voice and visual identification, makes change
- Patient receives incorrect medication

Scenario 2: EHR Data Poisoning
- Attackers compromise AI-powered clinical decision support system
- Inject malicious training data causing system to:
- Recommend dangerous drug combinations
- Miss critical diagnoses in medical imaging
- Suggest incorrect treatment protocols
- Errors appear to be AI mistakes rather than malicious attacks
Scenario 3: Automated Mass Exploitation
- AI scans entire health system's medical device inventory
- Identifies vulnerable insulin pumps across multiple hospitals
- Generates custom exploits for each device type
- Deploys ransomware simultaneously to all vulnerable devices
- Demands ransom with threat to manipulate insulin dosages
Scenario 4: The AI Social Engineer
- LLM scrapes LinkedIn, hospital websites, medical journals to build detailed employee profiles
- Generates personalized phishing campaigns for 1,000+ employees
- AI engages in conversational email exchanges, adapting to responses
- Human attackers only become involved after AI secures credentials or access
Why Healthcare Is Particularly Vulnerable to AI Threats
1. Medical Device Legacy
Many medical devices run outdated operating systems and cannot be easily patched:
- Windows XP and Windows 7 still common
- Proprietary systems with no available updates
- Vendor support ended years ago
- "If it works, don't touch it" mentality in clinical engineering
AI-powered vulnerability scanning can rapidly identify these devices and exploit known vulnerabilities at scale.
2. Complex Trust Relationships
Healthcare requires rapid trust decisions:
- Emergency situations demand fast credentialing
- Multiple healthcare organizations share patient data
- Physicians work across multiple hospitals
- Telehealth involves remote consultations with providers patient has never met
AI-powered impersonation exploits this necessary trust.
3. High-Consequence Errors
In financial services, fraud controls can catch and reverse unauthorized transactions. In healthcare, a medication error or missed diagnosis can kill a patient before the mistake is discovered.
4. Adoption Without Security
The survey finding that only 37% of health organizations have processes to assess AI tool security before deployment is alarming. Healthcare is rushing to adopt:
- AI-powered diagnostics
- Clinical decision support systems
- Administrative automation
- Chatbots for patient interaction
Without adequate security assessment, these tools become attack vectors.
What Healthcare Organizations Must Do
Immediate Priorities
1. Ransomware-Specific Preparedness
- Offline, immutable backups that cannot be encrypted by attackers
- Regular backup testing to verify restoration capability
- Incident response playbooks specifically for ransomware
- Tabletop exercises simulating ransomware scenarios
2. Supply Chain Risk Management
- Inventory all third-party connections to your environment
- Assess security posture of critical vendors
- Contractual security requirements with teeth (e.g., liability for breaches)
- Network segmentation to limit vendor access to only necessary systems
- Continuous monitoring of vendor access and activity

3. Enhanced Detection
- Deploy AI-powered SIEM to detect anomalous behavior
- User and Entity Behavior Analytics (UEBA) to identify compromised accounts
- Network traffic analysis to spot lateral movement
- Endpoint detection and response (EDR) on all systems, including medical devices where feasible
4. Medical Device Security
- Asset inventory of all connected medical devices
- Vulnerability assessment identifying devices with known exploits
- Network isolation for high-risk devices (e.g., separate VLAN for infusion pumps)
- Vendor accountability demanding security patches and support
5. Advanced Security Awareness
- Quishing education on QR code risks
- ClickFix and FileFix awareness training on fake error messages
- Deepfake awareness for executives and high-value targets
- Simulated attacks using these new techniques to test effectiveness
Strategic Transformation
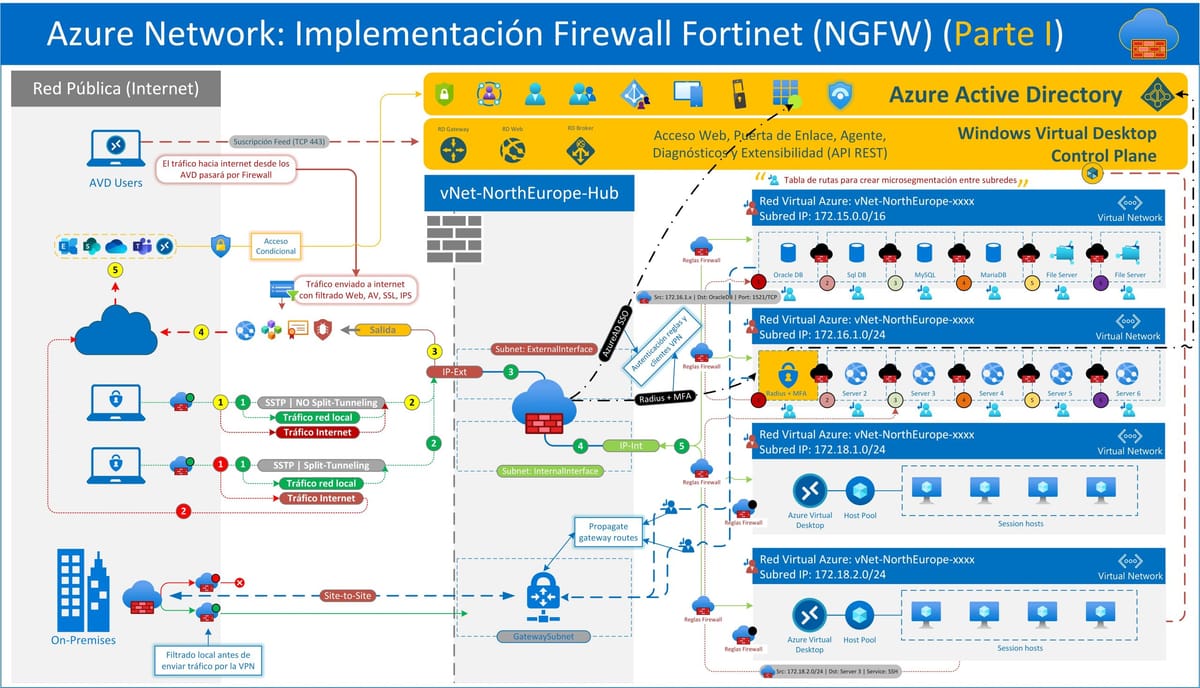
1. Zero Trust Architecture
Healthcare must move from perimeter-based security to zero trust:
- Continuous verification of all access requests
- Least privilege access controls
- Micro-segmentation to limit lateral movement
- Assume breach and design for containment
2. AI Security Governance
Before deploying AI tools:
- Security assessment by qualified professionals
- Vendor security documentation review
- Data handling evaluation (where does AI send data?)
- Adversarial testing (can the AI be manipulated?)
- Ongoing monitoring for anomalous AI behavior
3. Insider Threat Program
Given Everest and other groups' insider recruitment:
- Behavioral monitoring for unusual data access
- Privileged access management with extensive logging
- Anonymous reporting mechanisms for suspicious activity
- Regular background re-checks for high-risk positions
4. Business Continuity Beyond IT
Healthcare's digital dependence requires:
- Downtime procedures for all clinical systems
- Paper-based backup protocols (yes, really)
- Alternative care coordination methods
- Communication systems that don't rely on compromised infrastructure
5. Cyber Insurance with Healthcare Expertise
Standard cyber insurance often doesn't address healthcare-specific risks:
- Business interruption calculations that account for patient diversions
- Malpractice exposure from cyber incidents affecting care
- Regulatory defense for HIPAA and state law violations
- Crisis management for patient communication and media relations
Regulatory and Policy Priorities
1. Mandatory Minimum Security Standards
Healthcare needs sector-specific security requirements:
- Baseline controls all organizations must implement
- Medical device security standards
- Supply chain security requirements
- Regular security assessments and audits
2. Information Sharing Incentives
Organizations need safe harbor to share threat intelligence:
- HIPAA-compliant information sharing
- Protection from liability for good-faith sharing
- Government-facilitated ISACs and ISAOs
- Real-time threat feeds
3. Vendor Accountability
Legislation should:
- Require security by design for medical devices
- Mandate long-term security support (10+ years)
- Create liability for vendors who ship insecure products
- Establish certification programs for healthcare IT vendors
4. Workforce Development
Healthcare cybersecurity shortage is critical:
- Scholarships and training programs
- Career pathways from clinical to security roles
- Competitive compensation for healthcare security professionals
- Public-private partnerships for training
Survey Findings: What Healthcare Leaders Worry About
Health-ISAC's survey of nearly 250 health executives and cybersecurity professionals revealed:

Top Concerns for 2026
1. Ransomware (Ranked #1)
No surprise given 455 incidents in 2025. Healthcare leaders recognize this is an existential threat.
2. Phishing (Ranked #2)
Despite years of awareness training, phishing remains the primary initial access vector.
3. Third-Party Compromise (Ranked #3)
Supply chain risk awareness has dramatically increased post-Change Healthcare.
4. Exploitation of Newly Discovered Software Flaws (Ranked #4)
Zero-day and newly disclosed vulnerabilities create patch windows attackers exploit.
5. AI-Enabled Tactics (Growing Concern)
66% anticipate significant AI impact on cybersecurity, but only 37% have AI security assessment processes.
The Preparation Gap
The disconnect between concern and preparation is alarming:
66% expect AI will significantly impact cybersecurity
37% have processes to assess AI security before deployment
29% gap between awareness and action
This 29-point preparation deficit suggests many healthcare organizations will deploy AI tools without adequate security assessment, creating vulnerabilities that attackers will inevitably exploit.
Conclusion: An Existential Moment for Healthcare Cybersecurity
The Health-ISAC 2026 Report arrives at a pivotal moment. Healthcare organizations face a perfect storm:
- Escalating threats: 455 ransomware attacks, sophisticated supply chain compromises, AI-powered tactics
- Inadequate defenses: Legacy medical devices, limited security budgets, workforce shortages
- Life-or-death consequences: Cyberattacks that kill patients, disrupt clinical care, and undermine public trust in healthcare systems
Errol Weiss's statement bears repeating:
"Cyber threats are no longer isolated events. They represent life-saving business continuity crises that can impact patient care, staff safety, and public trust."
This is the reality: cyberattacks on healthcare kill people. The Change Healthcare attack disrupted cancer treatments. The Synnovis attack forced postponement of surgeries. Future attacks will cause deaths directly attributable to cyber incidents.
Healthcare cybersecurity is no longer an IT problem or a compliance checkbox—it's a patient safety imperative that demands board-level attention, executive commitment, and substantial investment.
The question facing every healthcare CEO, CFO, and board member is stark: Will you make cybersecurity a strategic priority now, before patients die from a preventable cyberattack? Or will you be explaining to grieving families, regulators, and prosecutors why you didn't act when the warnings were clear?
The Health-ISAC report has provided the warning. What happens next is up to healthcare leadership.

About This Analysis
This report is published by CISO Marketplace, providing healthcare security leaders with actionable intelligence and strategic guidance for protecting patient care in an era of escalating cyber threats.
Sources:
- Health-ISAC 2026 Global Health Sector Threat Landscape Report
- Health-ISAC (Health Information Sharing and Analysis Center)
- Survey of 250 healthcare executives and cybersecurity professionals
- Errol Weiss, Chief Security Officer, Health-ISAC
For More Information:
Health-ISAC: https://h-isac.org
Report Access: Contact Health-ISAC for full report details