Inside China's Cyber War Rehearsals: Leaked Documents Reveal Critical Infrastructure Attack Training

Leaked technical documents expose "Expedition Cloud" — a secret training platform where Chinese operatives practice attacks against replicas of foreign power grids, energy systems, and transportation networks. Meanwhile, the Typhoon family of threat actors has pre-positioned inside American critical infrastructure for years, waiting for the order to strike.
Executive Summary
In early 2026, a cache of technical documents leaked from an unsecured FTP server revealed what U.S. intelligence officials have long suspected: China is actively rehearsing cyber operations designed to cripple foreign critical infrastructure. The documents describe a sophisticated training platform called "Expedition Cloud" (远征云), where operatives practice attacks against painstakingly recreated replicas of power grids, energy transmission systems, and transportation networks belonging to China's "main operational opponents."
This revelation arrives as multiple Chinese threat actor groups — collectively known as the "Typhoon" family — have been discovered lurking inside U.S. critical infrastructure for up to five years. Their mission is not espionage. They are pre-positioning for sabotage.
The implications are stark. As Lt. Gen. Thomas Hensley, commander of the 16th Air Force and U.S. Air Force Cyber, warned in September 2025: "If we find ourselves in a conflict with China and they execute destructive cyberattacks against our critical infrastructure in the United States, that is total war in my definition."
This investigation examines the evidence, the threat actors, and what defenders must do now.

Part I: The Expedition Cloud Revelation
How the Documents Emerged
In late 2025, security researchers monitoring underground data repositories discovered a cache of Chinese technical documents on an unsecured FTP server. The server had been collecting material from a personal device belonging to a developer at CyberPeace (Nanjing Saining Network Technologies), a Chinese cybersecurity company. The developer's computer had been infected with infostealer malware — an irony not lost on the researchers who discovered it.
The haul was substantial: source code, training curricula, software assets, engineering specifications, and system architecture blueprints. What emerged from the analysis painted a picture more alarming than any previous intelligence assessment.
At the center of the documents was something called "Expedition Cloud" — a training platform unlike anything Western analysts had seen before.
What Expedition Cloud Actually Is
According to the leaked documentation, Expedition Cloud is not merely a cyber range for training security professionals. It is a purpose-built rehearsal environment where attackers practice compromising replicas of real-world critical infrastructure networks.
The documents describe the system's targets explicitly: "the real network environments" of China's "main operational opponents in the South China Sea and Indochina directions." This geographic focus encompasses Vietnam, the Philippines, Malaysia, Brunei, and — most significantly — Taiwan.
The technical specifications reveal a platform of considerable sophistication:
Scale and Capacity:
- Support for 300 concurrent users
- 10,000 simultaneous network connections
- DNS gateway infrastructure with a URL classification database containing 100 million entries
- 50,000 concurrent connection capacity for simulation environments
Operational Structure:
The platform organizes operations into two distinct team types: reconnaissance groups tasked with mapping target environments, and attack groups that execute the actual compromise operations. This mirrors the organizational structure of real-world nation-state cyber operations.
Target Environments:
The training scenarios include recreations of power sector networks, energy transmission infrastructure, transportation systems, and even smart home systems. The documents specifically mention that scenarios involve equipment from major Western vendors including Cisco, Fortinet, WatchGuard, and Juniper.
Why This Discovery Matters
Dakota Cary, a China-focused researcher at SentinelOne, was among the first to analyze the documents. His assessment was unequivocal: "This was created to meet the needs of a state customer. It's definitely something we've not had insights to before."
The client for Expedition Cloud was identified in the documents as China's Ministry of Public Security.
Eugenio Benincasa, a researcher at ETH Zurich's Center for Security Studies, emphasized the unprecedented nature of the discovery: "This is a first — it's not just developing a cyber range for the state or the security apparatus to train on, this is mimicking critical infrastructure."
But perhaps the most chilling assessment came from Allar Vallaots, the lead coordinator of NATO's Locked Shields cyber defense exercise and a researcher at CR14 in Estonia. After reviewing the documents, Vallaots concluded that what was being documented went beyond training.
"This is basically indicating that they are using something that is classified, or some operational tools," Vallaots said. "They are rehearsing here more than training."
The distinction is crucial. Training develops skills. Rehearsals prepare for specific operations.
The Operational Security Architecture
The Expedition Cloud documentation reveals sophisticated measures designed to prevent attribution and enable operations without detection.
The platform employs physical and logical isolation through "optical gates" — unidirectional data flow devices that separate internal training environments from external networks. More than 200 "worker nodes" are distributed globally, using three different encrypted protocols. The system is designed to deploy "independent, private anti-piracy routes" to prevent tracking.
Every action taken during exercises is recorded: network traffic, system activity, operator decisions. This data collection serves dual purposes — performance evaluation and operational optimization.
"If you can measure all the different parameters within an attack, then you train the attacks," Vallaots explained. The implications extend to artificial intelligence applications. "AI can find paths, bottlenecks, other ideas, much faster than a human... Whoever possesses the better AI wins."
The platform isn't just training operators. It's potentially generating data to train autonomous attack systems.

Part II: The Typhoon Family — Pre-Positioned and Waiting
The Expedition Cloud revelations do not exist in isolation. They confirm what U.S. intelligence agencies have been warning about for over two years: Chinese threat actors have already penetrated American critical infrastructure and are maintaining persistent access.
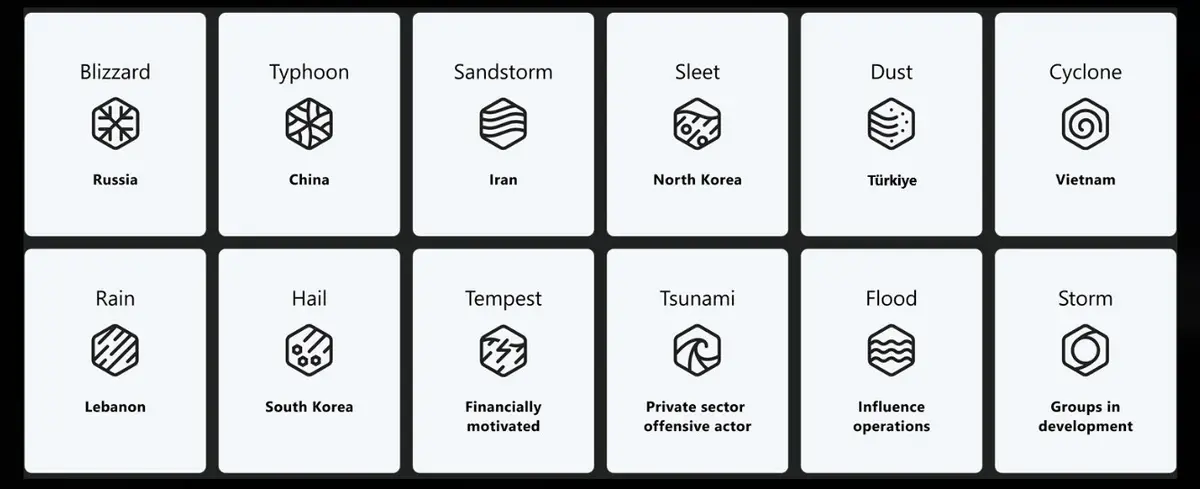
These groups share a naming convention — Typhoon — assigned by Microsoft's threat intelligence team. But they serve distinct missions under different chains of command.
Volt Typhoon: The Sabotage Force
Organizational Attribution: People's Liberation Army Cyberspace Force
Active Since: At least mid-2021, though some compromises may date back over five years
Primary Mission: Pre-positioning within U.S. critical infrastructure for destructive cyberattacks designed to disrupt American military mobilization during a Taiwan contingency
Volt Typhoon is not conducting espionage in the traditional sense. They are not exfiltrating intellectual property or stealing state secrets. They are establishing persistent access that can be activated to cause physical disruption when ordered.
Their targeting priorities reveal the strategic calculus: power grids, water treatment facilities, transportation systems, telecommunications networks, and — critically — U.S. military installations, with particular focus on Guam.
Guam's significance cannot be overstated. As the westernmost U.S. territory, it serves as a critical staging area for any American response to a Chinese invasion of Taiwan. Crippling Guam's infrastructure would severely complicate U.S. force projection.
The Littleton Case Study
In September 2025, Dragos published a detailed analysis of a Volt Typhoon compromise at Littleton Electric Light & Water Department, a municipal utility in Massachusetts. The findings were alarming.
The attackers maintained access for ten months — from February 2023 through November 2023. During that time, they exfiltrated operational technology (OT) operating procedures and spatial layout data related to energy grid operations.
They didn't steal customer data or financial information. They took the technical documentation needed to understand how to disrupt the grid.
This targeting pattern has repeated across more than 100 identified intrusions. Volt Typhoon operators consistently prioritize geographic information system (GIS) data, network diagrams, and operating instructions. They are mapping the systems they intend to attack.
Living Off the Land
Volt Typhoon's technical approach represents a significant evolution in nation-state tradecraft. Rather than deploying custom malware that might trigger endpoint detection, they exploit built-in Windows tools: wmic, ntdsutil, netsh, PowerShell.
This "living off the land" approach makes detection extraordinarily difficult. Every command the attackers execute is something a legitimate administrator might run. There are no malicious binaries to signature-match, no command-and-control beacons to intercept.
Their infrastructure approach is equally sophisticated. Traffic routes through compromised small office/home office (SOHO) routers, firewalls, and VPN hardware — devices often running outdated firmware and rarely monitored. In January 2024, the FBI disrupted a botnet of such devices called "KV Botnet" that Volt Typhoon was using for operational relay.
Initial access typically comes through vulnerabilities in internet-facing VPN appliances and firewalls. They target end-of-life devices that no longer receive security updates. Weak administrator passwords and factory default logins provide easy entry.
Once inside, they maintain persistence through stolen credentials, avoiding the need to redeploy after patches or reboots. Some compromises have persisted for more than five years without the attackers taking any destructive action.
They are waiting.
Salt Typhoon: The Intelligence Operation
Organizational Attribution: Ministry of State Security (MSS)
Active Since: Approximately 2020
Primary Mission: Cyber espionage targeting telecommunications infrastructure and counterintelligence targets
If Volt Typhoon represents China's pre-positioned sabotage capability, Salt Typhoon represents its strategic intelligence operation. The scale of their telecommunications compromise is unprecedented.
As of August 2025, Salt Typhoon had compromised over 200 targets in more than 80 countries. Within the United States alone, at least nine major telecommunications providers have been breached: Verizon, AT&T, T-Mobile, Charter/Spectrum, Lumen, Consolidated Communications, Windstream, and at least one additional unnamed carrier.
The scope of access is staggering: metadata for more than one million users' calls and text messages.
The CALEA Breach
Perhaps most concerning is Salt Typhoon's access to Communications Assistance for Law Enforcement Act (CALEA) systems — the lawful intercept infrastructure used by the FBI for court-authorized wiretaps.
This means Chinese intelligence has visibility into which Americans are under federal surveillance. In counterintelligence terms, this is catastrophic. The Chinese government can now identify not only FBI targets but also the methodologies and sources informing investigations.
The political implications became apparent when it was revealed that phones belonging to Donald Trump, JD Vance, and Harris campaign staff had been compromised.
Technical Approach
Salt Typhoon's methods differ from Volt Typhoon's patient, low-profile approach. They exploit vulnerabilities aggressively, particularly in edge network devices:
- CVE-2023-20198 (Cisco IOS XE) — A maximum-severity vulnerability allowing unauthorized administrative access
- CVE-2024-3400 (Palo Alto PAN-OS) — Command injection in GlobalProtect
- CVE-2024-21887 (Ivanti Connect Secure) — Authentication bypass in VPN appliances
- CVE-2018-0171 (Cisco Smart Install) — Remote code execution in network infrastructure
They deploy a sophisticated Windows kernel-mode rootkit called "Demodex" for persistence, modify access control lists to add attacker IP addresses, and expose additional services like SSH, RDP, and FTP on compromised systems.
Their anti-forensic techniques are highly developed. Operations blend with legitimate network traffic. Analysis is actively hindered.
The Broader Typhoon Ecosystem
Volt and Salt represent the most documented threats, but they are not alone.
Flax Typhoon operates under MSS direction, linked to a Beijing-based cybersecurity company called Integrity Technology Group. Their primary focus is Taiwan — government systems, technology sectors — but they've built a botnet comprising hundreds of thousands of hijacked internet-connected devices globally. In September 2024, the U.S. government took control of this botnet. In January 2025, Treasury sanctioned Integrity Technology Group.
Silk Typhoon (previously known as Hafnium) gained notoriety with the 2021 Microsoft Exchange Server mass exploitation. In December 2024, they compromised the U.S. Treasury Department, including the Office of Foreign Assets Control (OFAC) — the agency responsible for administering economic sanctions against China.
Additional groups including Linen Typhoon and Violet Typhoon have been identified but remain less documented. In Singapore, UNC3886 was publicly named in July 2025 for targeting telecommunications infrastructure.
Part III: The Taiwan Connection
Understanding why China is preparing to attack American critical infrastructure requires understanding Taiwan.
The 2027 Timeline
Since 2021, U.S. military and intelligence officials have repeatedly cited 2027 as a pivotal year. That year marks the 100th anniversary of the People's Liberation Army and represents a frequently cited potential window for a Chinese invasion of Taiwan.
Xi Jinping has made "reunification" with Taiwan a personal priority and a core objective of his leadership. The question for American strategists is not whether China will eventually move on Taiwan, but when — and what can be done to deter or complicate such action.
This is where cyber operations become critical.
The Mobilization Problem
In any Taiwan scenario, the United States would face a fundamental logistics challenge. Taiwan is approximately 8,000 miles from the continental United States. American forces would need to mobilize, deploy, and sustain operations across the Pacific.
This mobilization would depend on critical infrastructure: the power grids that supply military installations, the telecommunications networks that enable command and control, the transportation systems that move equipment and personnel, the water systems that sustain bases and communities.
Volt Typhoon's targeting makes strategic sense through this lens. Their compromises in Guam target the power authority, the largest cellular provider, and federal defense networks. Massachusetts might seem like an odd target for Pacific contingency planning — until you consider that supply chains and logistics hubs span the continental United States.
Disrupting even a portion of American critical infrastructure during the opening hours of a Taiwan conflict could slow mobilization by days or weeks. In a rapid amphibious assault, those delays could prove decisive.
The Tacit Admission
In 2024, Chinese officials met with their American counterparts in a diplomatic exchange that U.S. officials have since characterized as remarkable.
During these discussions, Chinese officials made remarks that American participants interpreted as "a tacit admission and a warning to the U.S. about Taiwan."
The implication was clear: China's cyber capabilities exist. They are deployed. And they will be activated if America intervenes.
The Taiwan Surge
Taiwan's own intelligence reveals the pressure they face daily.
According to the Taiwan National Security Bureau's January 2026 report, cyberattacks from China rose 6% in 2025, reaching an average of 2.63 million intrusion attempts per day. The energy sector and hospitals saw the largest increases.
Crucially, attack patterns correlate with PLA "joint combat readiness patrols" and major Taiwanese political events. When military pressure increases in the Taiwan Strait, cyber pressure increases in parallel.
This coordination suggests centralized command and control. The cyber operations are not freelance activities by patriotic hackers. They are integrated into military planning.

Part IV: "Total War in My Definition"
In September 2025, Lt. Gen. Thomas Hensley addressed the Air Force Association conference with unusual directness.
As commander of the 16th Air Force and U.S. Air Force Cyber, Hensley leads American airborne and cyber warfare capabilities. His remarks represented a stark escalation in official rhetoric.
"If we find ourselves in a conflict with China and they execute destructive cyberattacks against our critical infrastructure in the United States, that is total war in my definition," Hensley said.
The phrase "total war" carries specific historical weight. It evokes conflicts where the distinction between military and civilian targets dissolves — where the entire society becomes a target.
"Using the cyber domain to execute a counter-value attack against the U.S. population," Hensley continued, making explicit what the targeting means: not just military infrastructure, but civilian systems upon which the American population depends.
The Precedent Problem
This isn't theoretical. Russia demonstrated the concept in Ukraine.
In December 2015, Russian hackers knocked out power to approximately 230,000 Ukrainian customers in what was later attributed to the Sandworm group. The outage lasted several hours. In December 2016, a more sophisticated attack hit the Ukrenergo transmission company, causing power outages in Kyiv.
These attacks served as proof of concept. Power grids can be disrupted remotely. The attacks also served as warnings — indicators of what Russia could do in a more serious conflict.
When Russia invaded Ukraine in February 2022, cyber operations accompanied kinetic strikes. The ViaSat satellite hack disrupted Ukrainian military communications in the opening hours. Wiper malware proliferated across Ukrainian networks.
China has watched these operations carefully. They have learned.
The Response Question
American policymakers face a dilemma. Robust response risks escalation. Inadequate response invites aggression.
Previous administrations were described by officials as "hesitant" to respond offensively to Chinese cyber operations. This hesitancy was driven by concerns about escalation, legal constraints, and the difficulty of proportional response.
At RSA Conference 2025, senior officials signaled a potential policy shift. "If you come and do this to us, we'll punch back," they warned, articulating a "defend forward" posture that could include preemptive actions.
But the Cyber Safety Review Board — the entity responsible for investigating major cyber incidents and providing strategic recommendations — was disbanded by the second Trump administration. The institutional capacity for coordinated response has been undermined precisely as the threat escalates.
Chinese Denials
Beijing's official position remains consistent denial.
The Chinese Foreign Ministry maintains that China "stands against hacking and fights such activities in accordance with the law." State media has characterized Volt Typhoon as a "misinformation campaign by U.S. intelligence agencies." The Chinese Embassy in Washington dismisses allegations as "unfounded and irresponsible smears and slanders."
These denials continue even as evidence accumulates. The Expedition Cloud leak represents perhaps the most damning documentary evidence yet — technical specifications for a state-sponsored training platform designed explicitly for rehearsing attacks on foreign critical infrastructure.
The client was identified. The targets were described. The capabilities were documented.

Part V: The Supply Chain Time Bomb
Beyond active intrusions, another threat vector demands attention: the hardware itself.
What's Inside the Inverters
The 2025 U.S.-China Economic and Security Review Commission report documented findings that should alarm every critical infrastructure operator.
Multiple independent analyses identified "undocumented communication modules" in Chinese-manufactured solar inverters and battery systems. Some devices contained what researchers described as "secret radios" — components with no documented purpose in device specifications.
These devices are deployed throughout American energy infrastructure. They're on rooftops and in solar farms. They're connected to grid management systems.
The implications are serious. A device that can communicate without the operator's knowledge can potentially be commanded without the operator's knowledge. Whether for surveillance, disruption, or both, the capability exists.
The Firmware Problem
Modern operational technology runs on firmware — low-level software that controls device behavior. Much of this firmware is opaque to the organizations that deploy the devices. Updates come from vendors, often automatically. The ability to inspect what's actually running is limited.
Chinese manufacturers control update pipelines for equipment deployed in critical American infrastructure. This is not hypothetical supply chain risk. This is realized supply chain dependence.
What the Commission Recommends
The USCC report offered specific recommendations:
- Stronger procurement safeguards and national testing of foreign-origin OT devices before critical infrastructure deployment
- Open-source firmware initiatives for field-deployed energy assets — enabling inspection and verification
- Software Bills of Materials (SBOM), Firmware Bills of Materials (FBOM), and Hardware Bills of Materials (HBOM) with validated provenance for all critical infrastructure components
- Regional incident response exercises and technical playbooks for coordinated response
- Support for utility asset owners with segmentation, monitoring, and rapid response capabilities
These recommendations acknowledge an uncomfortable truth: the supply chain has already been compromised. The question is how to manage the risk going forward.
Part VI: What Defenders Must Do Now
For CISOs and critical infrastructure security leaders, the intelligence is clear. The threat is present. Action is required.
Immediate Priorities
1. Assume Compromise
If your organization operates critical infrastructure, you should assume you have been or are currently compromised. This isn't pessimism — it's operational reality based on the scope of documented intrusions.
Your security posture should begin from the assumption that an adversary has access and work backward. What can you detect? What can you contain? What can you reconstitute?
2. Focus on Behavioral Detection
Signature-based detection will not catch Volt Typhoon. They're using your tools against you — wmic, PowerShell, netsh, ntdsutil. Every command they execute appears legitimate in isolation.
Detection must be behavioral. You need to identify anomalous patterns: lateral movement that doesn't match expected traffic, privileged command execution from unexpected sources, data collection targeting operational documentation.
Dragos specifically recommends:
- Monitoring behaviors rather than signatures
- Comparing unusual lateral movement with expected traffic patterns
- Validating suspicious user activity, even from regular employee accounts
- Implementing integrity monitoring for critical systems
3. Prioritize Edge Device Security
Both Volt Typhoon and Salt Typhoon gain initial access through internet-facing devices — VPN appliances, firewalls, routers. These devices are often the least monitored components of enterprise networks.
Immediate actions:
- Inventory all internet-facing devices completely
- Identify and replace end-of-life equipment that no longer receives security updates
- Audit configurations for weak passwords, default credentials, and unnecessary services
- Prioritize patching for edge devices above workstations
Key vulnerabilities to verify remediation:
- CVE-2023-20198 (Cisco IOS XE)
- CVE-2024-3400 (Palo Alto PAN-OS)
- CVE-2024-21887 (Ivanti Connect Secure)
- CVE-2018-0171 (Cisco Smart Install)
4. Segment OT Networks
If your organization operates operational technology — industrial control systems, SCADA, building management systems — network segmentation is not optional.
OT networks should be isolated from IT networks with enforced firewall rulesets. Connections between segments should be logged and monitored. High-risk components should receive additional isolation.
The goal is containment. If attackers achieve IT access, OT compromise should not be automatic.
5. Monitor OT Protocols
Standard enterprise security tools often don't understand OT protocols like Modbus and DNP3. Deploy monitoring capabilities specifically designed for industrial environments.
Anomalies in OT traffic may indicate reconnaissance or manipulation. Normal baseline behavior must be established so deviations can be detected.
6. Audit Chinese-Origin Components
Conduct a comprehensive audit of operational technology components manufactured in China or using Chinese-origin hardware. Solar inverters, battery systems, and power management equipment deserve particular scrutiny.
Where possible, conduct forensic evaluation. Where re-flashing firmware is feasible and doesn't void safety certifications, consider rebuilding devices with known-good images.
For devices where inspection is impractical, compensating controls become essential: network isolation, traffic monitoring, out-of-band verification of commands.
Incident Response Preparation
1. Develop Pre-Planned Procedures
When (not if) a compromise is discovered, response must be rapid. Develop response procedures before they're needed.
- Document escalation paths
- Identify key personnel and their backup contacts
- Establish communication channels that don't depend on potentially compromised infrastructure
- Pre-coordinate with FBI, CISA, and relevant sector ISACs
2. Practice
Tabletop exercises should simulate realistic Typhoon scenarios. What happens if VPN access is compromised? What if OT systems begin behaving anomalously? What if a regional power outage occurs during a Pacific crisis?
The goal isn't to create perfect plans — it's to build muscle memory and identify gaps before they matter.
3. Coordinate Regionally
Critical infrastructure systems are interdependent. A power outage affects water treatment. Telecommunications failures impact emergency response.
Regional coordination with peer organizations, state authorities, and federal partners must be established before crisis hits. Know who to call. Know what they can provide. Know what you can provide them.
Long-Term Posture
1. Demand Supply Chain Transparency
Push vendors for Software Bills of Materials, Firmware Bills of Materials, and Hardware Bills of Materials. Understand what's in your infrastructure.
Where vendors refuse transparency, evaluate alternatives. Where alternatives don't exist, document the risk and implement compensating controls.
2. Participate in Information Sharing
Sector ISACs, FBI field offices, and CISA regional coordinators represent force multipliers for organizations that engage with them.
Share indicators of compromise. Report anomalous activity. Participate in classified briefings when eligibility permits.
The adversary benefits from defenders operating in isolation. Break isolation.
3. Plan for Degraded Operations
Critical infrastructure organizations should develop continuity plans that assume cyber-induced outages.
- How do you operate if SCADA is unavailable?
- How do you communicate if telecommunications are degraded?
- How do you coordinate if regional systems fail?
Manual procedures, out-of-band communications, and degraded-operations training may prove essential.

Part VII: The Stakes
The evidence assembled here leads to an uncomfortable conclusion.
China is not merely developing theoretical capabilities for some hypothetical future conflict. They are:
- Training operatives on realistic simulations of target infrastructure
- Pre-positioning access inside American critical infrastructure systems
- Waiting for orders that may come during a Taiwan crisis
- Preparing to execute what an American general describes as "total war"
The timeline is uncertain. 2027 looms as a frequently cited inflection point, but crises can accelerate or delay based on factors beyond any single analyst's ability to predict.
What is certain: the capability exists. The access exists. The intent, as documented in leaked training materials and as acknowledged in diplomatic discussions, exists.
Lt. Gen. Hensley's warning deserves repetition: "Using the cyber domain to execute a counter-value attack against the U.S. population."
This is not about intellectual property theft. This is not about espionage for commercial advantage. This is preparation for attacks designed to harm the American population — to turn off lights, contaminate water, disrupt transportation, impede emergency response.
For critical infrastructure defenders, the responsibility is clear. You are not protecting a network. You are protecting the systems upon which communities depend.
The adversary has prepared. You must prepare as well.
Appendix: Key Statistics
| Metric | Value | Source |
|---|---|---|
| Volt Typhoon compromises identified | 100+ | CISA/FBI advisory |
| Salt Typhoon victims | 200+ across 80 countries | August 2025 advisory |
| U.S. telecom users' metadata accessed | 1 million+ | Congressional testimony |
| Volt Typhoon persistence duration | Up to 5+ years | Dragos analysis |
| Taiwan daily intrusion attempts | 2.63 million | Taiwan NSB (Jan 2026) |
| Taiwan year-over-year attack increase | 6% | Taiwan NSB (Jan 2026) |
| Expedition Cloud capacity | 300 users, 10,000 connections | Leaked documents |
| FBI bounty for Salt Typhoon information | $10 million | FBI (April 2025) |
Appendix: Key Vulnerabilities
Critical infrastructure defenders should prioritize patching and verification for these vulnerabilities actively exploited by Typhoon actors:
| CVE | Product | CVSS | Description |
|---|---|---|---|
| CVE-2023-20198 | Cisco IOS XE | 10.0 | Web UI privilege escalation |
| CVE-2024-3400 | Palo Alto PAN-OS | 10.0 | GlobalProtect command injection |
| CVE-2024-21887 | Ivanti Connect Secure | 9.1 | Authentication bypass |
| CVE-2018-0171 | Cisco Smart Install | 9.8 | Remote code execution |
Appendix: U.S. Government Sanctions and Actions
| Date | Target | Basis |
|---|---|---|
| January 2024 | KV Botnet | FBI disruption (Volt Typhoon infrastructure) |
| September 2024 | Flax Typhoon botnet | U.S. government takeover |
| December 10, 2024 | Sichuan Silence Information Technology | Treasury sanctions |
| January 3, 2025 | Integrity Technology Group | Treasury sanctions (Flax Typhoon) |
| January 17, 2025 | Yin Kecheng, Sichuan Juxinhe Network Technology | Treasury sanctions (Salt Typhoon) |
| March 5, 2025 | Zhou Shuai, Shanghai Heiying Information Technology | Treasury sanctions |
| April 2025 | Salt Typhoon-associated individuals | $10 million FBI bounty |
Appendix: Resources for Defenders
Government Resources:
- CISA Joint Advisory on Volt Typhoon (February 2024)
- CISA/NSA/FBI Joint Advisory on Salt Typhoon (August 2025)
- CISA's Known Exploited Vulnerabilities Catalog
- Your sector's Information Sharing and Analysis Center (ISAC)
- FBI Cyber Division field offices
Industry Resources:
- Dragos WorldView threat intelligence
- McCrary Institute "Code Red" report
- Mandiant threat actor profiles
- Microsoft Threat Intelligence
Reporting:
- FBI IC3: ic3.gov
- CISA: us-cert.cisa.gov
- Sector-specific ISACs
About This Investigation
This investigation synthesizes information from:
- Recorded Future News reporting on the Expedition Cloud leak
- NetAskari technical analysis of leaked documents
- McCrary Institute's "Code Red" threat assessment
- U.S.-China Economic and Security Review Commission 2025 Annual Report
- Taiwan National Security Bureau intelligence assessments
- Dragos operational technology threat intelligence
- U.S. Treasury Department sanctions announcements
- Public remarks by Lt. Gen. Thomas Hensley and other officials
- Congressional testimony and government advisories
The evidence presented represents the most comprehensive publicly available assessment of China's critical infrastructure targeting capabilities and intentions.
Published by Breached.Company — Investigative breach journalism for CISOs and security leaders.