Iran's Cyber Warfare Paradox: Under Siege While Threatening Critical Infrastructure

As anti-government protests engulf Iran with death tolls potentially reaching 20,000, the Islamic Republic finds itself fighting a two-front cyber war—defending against unprecedented attacks on its own infrastructure while maintaining offensive operations against Western targets. This escalating cyber conflict, intertwined with the U.S. military operation in Venezuela earlier this month, reveals the evolving nature of modern warfare where kinetic and digital operations merge into a single theater.
The New Year's Day Cyber Assault
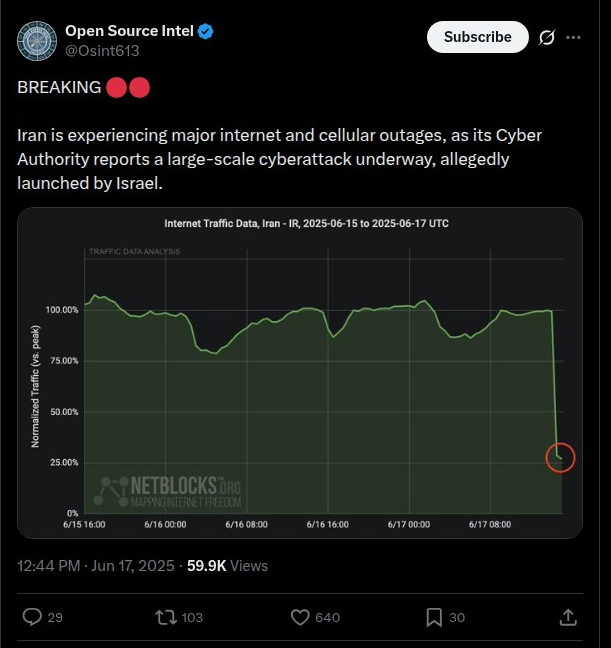
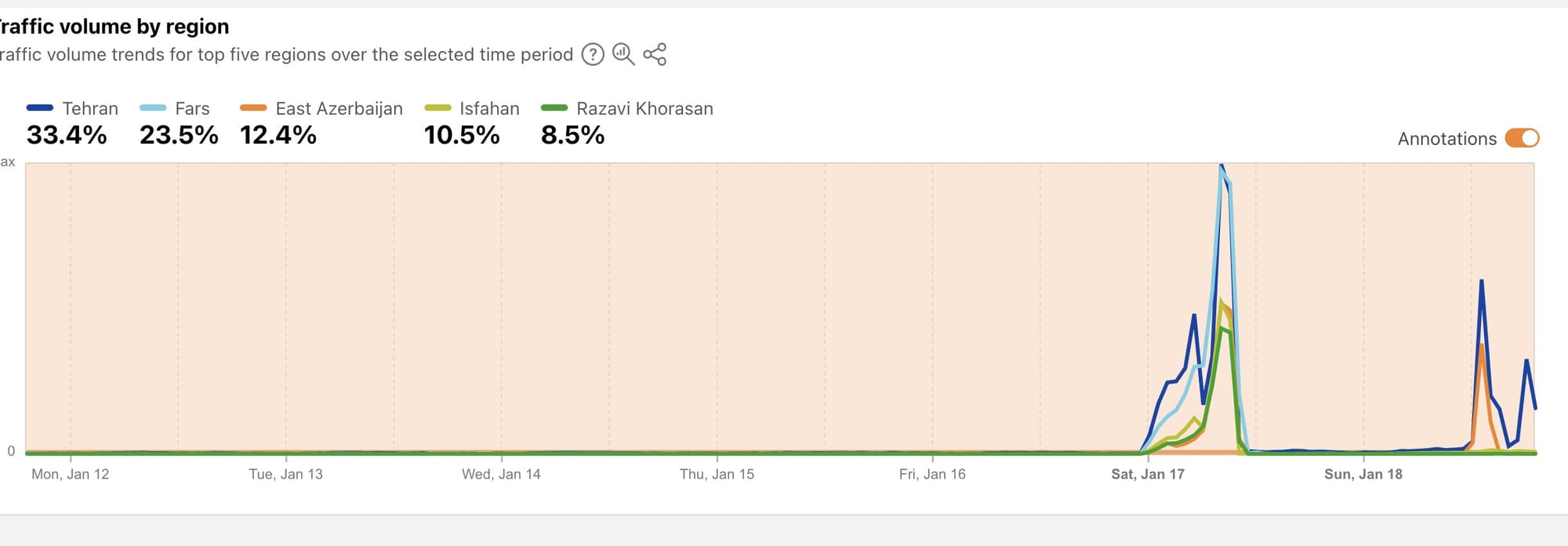
On January 1, 2026, Iran's telecommunications infrastructure faced what authorities describe as one of the largest distributed denial-of-service attacks in recent history. The assault peaked at 720 million packets per second, launched from over 125,000 distributed sources worldwide, according to Iran's Minister of Information and Communications Technology Sattar Hashemi.
The attack specifically targeted Iran's telecommunications service providers using a coordinated global botnet. Iranian officials claim their defenses successfully mitigated 502 million packets per second domestically, with the remainder countered through international partnerships. The timing coincided suspiciously with the beginning of mass protests over economic collapse, as Iran's currency plummeted to 1 million rials per U.S. dollar.
"This attack, in terms of its scope and severity, is among the most significant cyberattacks in recent times and could have created major challenges for the country," Hashemi stated, though he emphasized that preventive measures neutralized the threat.
The sophistication and scale suggest state-level resources, though attribution remains officially unconfirmed. However, the context cannot be ignored: just hours earlier, U.S. Cyber Command executed a devastating cyberattack on Venezuela's infrastructure as part of Operation Absolute Resolve.
The Venezuela Precedent: Cyber-Enabled Regime Change
The January 1 capture of Venezuelan President Nicolás Maduro by U.S. special forces marked a watershed moment in cyber warfare doctrine. U.S. Cyber Command disabled Caracas's power grid, scrambled air defense radars, and disrupted military communications in a coordinated operation that General Dan Caine described as "layering different effects to create a pathway" for kinetic forces.
The operation exposed critical vulnerabilities in Russian, Chinese, and Iranian-supplied defense systems that Venezuela had accumulated over years. Iranian Mohajer-6 combat drones stationed at El Libertador Air Base—assembled in Venezuela using Iranian technology and technical personnel—proved ineffective against the integrated U.S. cyber and kinetic assault. (For a comprehensive analysis of the Venezuela operation, see our detailed examination of Operation Absolute Resolve.)
President Trump's public acknowledgment of cyber operations represents a significant shift from historical covert approaches. "The military is looking at it, and we're looking at some very strong options," Trump told reporters, signaling willingness to deploy cyber weapons openly as instruments of statecraft.
This transparency serves multiple purposes: demonstrating capability to adversaries like Iran, establishing new norms for cyber warfare, and potentially deterring future conflicts. But it also reveals to Tehran exactly what they might face if tensions escalate further.
🚨 Breaking: A cyber attack took over all TV stations in Iran, and they are broadcasting content showing how a free Iran could look like, encourage people to rise and reclaim their country 👇 pic.twitter.com/xT54yzCo4M
— Dr. Eli David (@DrEliDavid) June 18, 2025
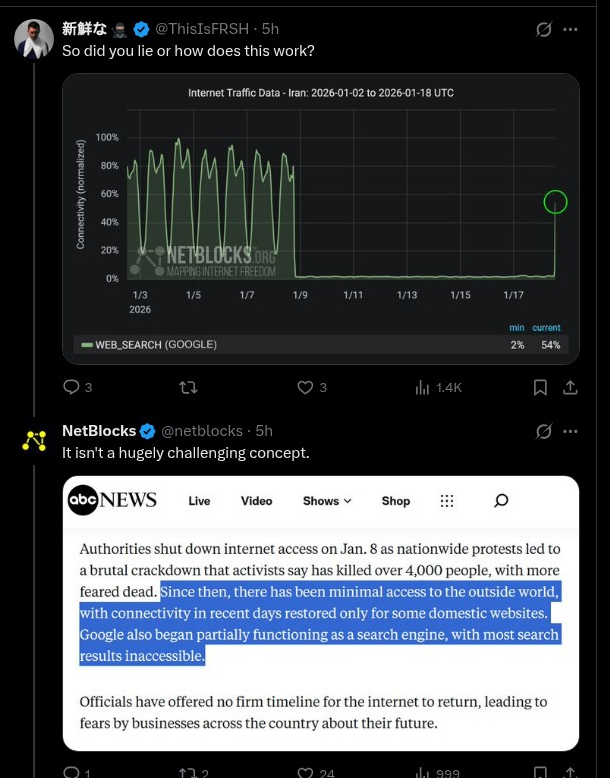
Iran's Defensive Posture: Internet Blackout and Starlink Countermeasures
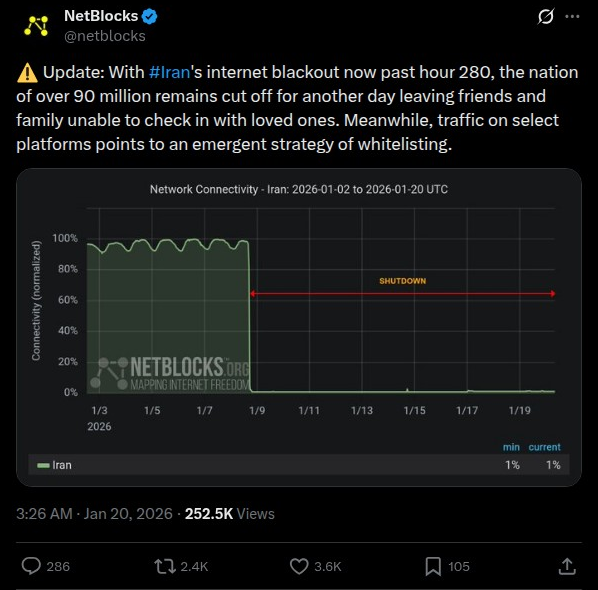
Faced with domestic unrest amplified by social media, Iranian authorities imposed a comprehensive internet shutdown now exceeding nine days—longer than the notorious 2019 blackout. NetBlocks reports that "though news is limited due to the information vacuum, reports indicate thousands have been killed in the subsequent crackdown."
However, this digital siege strategy faces a new challenge: Elon Musk's Starlink. Thousands of terminals smuggled into Iran since 2022 now provide protesters with uncensored satellite connectivity, circumventing traditional infrastructure controls. Iran has responded with GPS spoofing and satellite jamming techniques, but these prove only partially effective against the distributed satellite constellation.
The U.S. has also authorized free Starlink service for Iran through February, mirroring similar support provided to Venezuela after Maduro's capture. Cybersecurity specialists warn that Iranian jamming efforts could enable user tracking, exposing protesters to both cyber crime and state action.
Mahmood Amiry-Moghaddam, director of Iran Human Rights, confirmed that Starlink access has been "pivotal in sharing information about the protests," though the blackout's geographic scope and duration surpass all previous Iranian censorship efforts.
Massive Cyber Attack on Iran: What’s Really Happening?#CyberAttack #Iran #Israel #CyberWarfare #Geopolitics #DataSecurity #NationalSecurity #MiddleEastConflict #TechnologyInWar #DigitalEspionage pic.twitter.com/STlZHKRE0V
— CISO Marketplace (@CisoMarketplace) October 13, 2024
Iran's Offensive Cyber Ecosystem: IRGC Command and Hacktivist Proxies
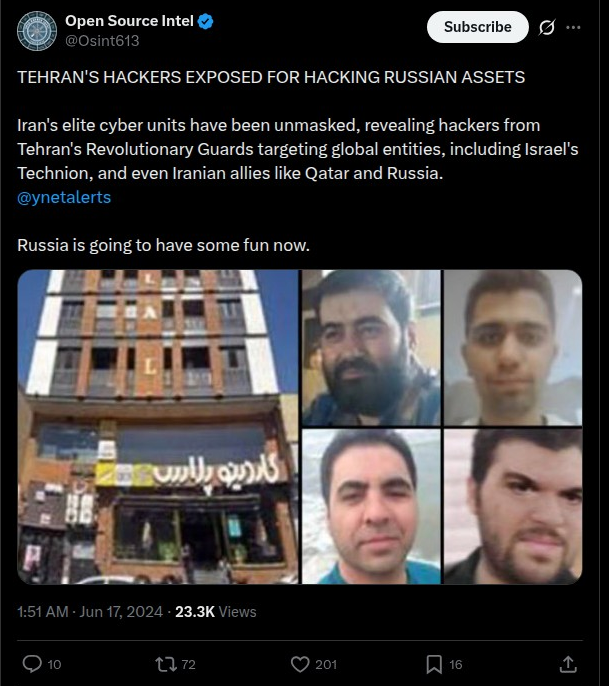
Despite domestic pressures, Iran maintains sophisticated offensive cyber capabilities through a coordinated network of Islamic Revolutionary Guard Corps (IRGC) units and hacktivist proxies. This ecosystem represents a deliberate strategy to conduct state operations while maintaining plausible deniability. (For our analysis of Iran's hacktivist proxy network, see The Cyber Proxy War: How Israel and Iran Are Fighting Through Hacktivist Coalitions.)
Key Iranian APT Groups:
IRGC-Affiliated Actors:
- APT33: Targets energy and aviation sectors, linked to destructive campaigns
- APT34 (OilRig): Focuses on Middle Eastern government and financial institutions
- APT35 (Charming Kitten): Conducts long-term espionage through sophisticated social engineering
- APT42: Specializes in credential harvesting and cloud environment compromise. This group has conducted high-profile operations including compromising John Bolton's email containing classified information, demonstrating sophisticated targeting of senior U.S. officials.
- CyberAv3ngers: Targets critical infrastructure, particularly Israeli-made PLCs in U.S. water systems
These groups share tactics, techniques, and procedures (TTPs), with evidence of operational coordination that blurs the line between state-sponsored APTs and "independent" hacktivists. As our mapping of the global cybercrime empire revealed, Iran—alongside Russia, China, and North Korea—controls 77% of all state-sponsored cyber operations, representing a coordinated threat ecosystem rather than isolated actors.
Recent Attack Patterns:
Critical Infrastructure Targeting: Between November 2023 and January 2024, CyberAv3ngers compromised at least 75 Unitronics PLC devices across multiple U.S. critical infrastructure sectors, including 34 in water and wastewater systems. The attacks exploited devices with default or no passwords, displaying the message: "You have been hacked, down with Israel. Every equipment 'made in Israel' is CyberAv3ngers legal target." Our in-depth analysis of Iranian actors targeting critical infrastructure documented how these groups use brute force attacks and MFA exploitation to maintain persistent access across healthcare, IT, and government sectors.
🚨JUST IN: Iran is a war zone, and the regime is rapidly losing control.
— DK🇺🇸🦅🇺🇸 (@1Nicdar) January 18, 2026
A man inside Iran just spoke to Fox News using Starlink, one of the only ways the truth is getting out. (Thanks to Elon Musk who provided this free service to all Iranian citizens when their communications… pic.twitter.com/Z2JW4yrcEA
Cyber-Enabled Kinetic Targeting: Amazon Web Services researchers identified a concerning evolution in Iranian tactics: using cyberattacks for reconnaissance before and after kinetic strikes. Imperial Kitten, an IRGC-linked group, compromised Automatic Identification Systems on maritime vessels and CCTV cameras in Israel to scope targets and assess damage from missile attacks. Our investigation into Lemon Sandstorm's prolonged Middle East campaign revealed similar patterns of persistent access and pre-positioning for future attacks.
Albania Campaign: In July 2022, IRGC-sponsored APT42 conducted destructive attacks against the Albanian government using ROADSWEEP ransomware, targeting the country for hosting Iranian opposition group MEK. The attacks disrupted government websites and TIMS/MEMEX systems, with hackers periodically publishing stolen database information. Iran's maritime cyber operations have shown similar sophistication, with our reporting on the digital siege against Iran's maritime empire demonstrating how attackers compromised satellite communication systems across Iranian shipping fleets.
BREAKING 🇮🇷 — Iranian state television IRIB was hacked by cybercriminals.
— UK Report (@UK_REPT) January 18, 2026
- The broadcast was interrupted and a message attributed to Reza Pahlavi was aired.
- The message called on the Iranian people to rise up against the regime and take control of their future. pic.twitter.com/8S4pOhsZMJ
Evidence of Diminished Iranian Offensive Capacity
Interestingly, defense analysts have observed a notable decline in certain Iranian cyber operations during the current crisis. Clive Higgins, CEO of Leonardo UK, reported that "online bot activity promoting the independence of Scotland from the UK reduced as Iranian authorities violently suppressed civil protest this month."
This suggests Iran's cyber resources are being redirected toward domestic surveillance and censorship efforts rather than external influence operations. A British parliamentary intelligence committee report from July 2025 had identified the UK as a priority target for Iranian cyber attacks, ranking just behind the U.S. and Saudi Arabia.
"Iran has a high appetite for risk when conducting offensive activity and its intelligence services are ferociously well-resourced," stated committee chairman Kevan Jones, noting Iran's use of "proxy groups—including criminal networks, militant and terrorist organizations, and private cyber actors—to provide it with a deniable means of attacking its adversaries."
The Escalation Calculus: Trump's "Holy Hell" and Iranian Red Lines
Senator Lindsey Graham's recent call for President Trump to unleash "holy hell" on Iran—including "a massive wave of military, cyber and psychological attacks"—reflects growing momentum for U.S. intervention. Graham specifically urged attacks to "destroy the infrastructure that allows the massacre and slaughter of the Iranian people, and take down the leaders responsible for the killing."
Trump has announced a 25% tariff on countries conducting business with Iran and canceled all meetings with Iranian officials "until the senseless killing of protesters STOPS." His January 2 warning that the U.S. would "come to their rescue" if protesters were killed has evolved into concrete considerations of cyber and kinetic operations.
The administration is reportedly evaluating options ranging from:
- Offensive cyber attacks targeting Iranian military and civilian infrastructure
- Psychological operations amplifying anti-regime messaging
- Covert actions supporting protest movements
- Targeted military strikes against nuclear facilities or IRGC assets
Iranian Parliament Speaker Mohammad Baqer Qalibaf responded with threats that "all American military centers, bases and ships in the region will be our legitimate targets" if the U.S. attacks.
BREAKING
— Goldie Ghamari | گلسا قمری 🇮🇷 (@gghamari) January 18, 2026
The Iranian National Revolution managed to hack the state broadcaster of the Islamic Dictatorship occupying Iran.
They broadcast a message from the Leader of the Iranian National Revolution, HRH @PahlaviReza
We are in the end game. https://t.co/CMlPM5w9vL pic.twitter.com/ntaryR6cwQ
The Cyber Warfare Paradigm Shift
The convergence of the Venezuela operation and Iran's domestic crisis illuminates several critical trends:
1. Cyber-Kinetic Integration Has Arrived The Venezuela operation demonstrated seamless integration of cyber effects with special operations forces. This isn't theoretical capability—it's operational doctrine being executed in real-time.
2. Transparency as Deterrence By publicly acknowledging cyber operations, the U.S. is reshaping norms. This transparency aims to deter adversaries but risks escalation as nations feel pressure to demonstrate their own capabilities.
3. Satellite Internet Changes Censorship Calculus Starlink fundamentally alters authoritarian regimes' ability to control information. Iran's inability to fully counter satellite-based connectivity represents a significant shift in the information warfare landscape.
4. Dual-Use Hacktivist Ecosystems Iran's model of maintaining hacktivist proxies for plausible deniability is being exposed through Treasury sanctions and intelligence disclosures. The CyberAv3ngers revelation—initially presented as independent activists but later sanctioned as IRGC officers—demonstrates this strategy's limits.
5. Critical Infrastructure Remains Vulnerable Despite years of warnings, Iranian actors continue successfully exploiting U.S. water systems, power grids, and industrial control systems through basic attacks like default passwords. The sophistication gap between defenders and attackers persists. As we documented in our analysis of Iran's cyber warfare and the Trump campaign hack, APT42's credential harvesting operations against high-profile targets demonstrate both Iran's offensive capabilities and the vulnerabilities in defensive postures—on both sides.

Implications for CISOs and Security Leaders
This evolving situation demands immediate attention to several risk factors:
Assess Iranian APT Exposure: Organizations with ties to Israeli vendors, defense contractors, or Middle Eastern operations face heightened risk. Review network segmentation, OT/IT isolation, and access controls for internet-facing industrial systems.
Prepare for DDoS Campaigns: Iranian-affiliated hacktivist groups conduct coordinated DDoS attacks during geopolitical tensions. Implement cloud-based DDoS protection, traffic filtering, rate limiting, and load balancing capabilities.
The Israeli Air Force successfully struck Iran’s “Cyber Police” headquarters in Tehran, destroying the building.
— OSINTtechnical (@Osinttechnical) June 21, 2025
The organization, known as FATA, is responsible for surveilling Iranian’s online activity and hunting down dissenters. pic.twitter.com/t3RdOxOaZ5
Monitor for Spear-Phishing Escalation: APT35 and APT42 excel at sophisticated social engineering, often impersonating journalists, academics, or event organizers. Enhance user training on recognizing typosquatted domains and suspicious invitations.
Secure Industrial Control Systems: The CyberAv3ngers attacks exploited Unitronics PLCs with default credentials. Audit all internet-connected OT devices, change default passwords, implement network segmentation, and consider removing PLC internet connectivity entirely.
Anticipate False-Flag Operations: Russia previously hijacked Iranian cyber infrastructure to piggyback into already-compromised networks. Attribution during heightened tensions may be unreliable; focus on indicators of compromise rather than threat actor identity.
The regime in #Iran continues to suffer from #cybersecurity breaches, particularly following the exposure of troves of leaked documents belonging to its Presidential Organization's servers. pic.twitter.com/B2sng6tYgE
— NCRI-FAC (@iran_policy) June 7, 2023
Develop Incident Response Plans for Geopolitical Events: The rapid escalation from protest to cyber warfare to potential military intervention illustrates how quickly threat landscapes shift. Tabletop exercises should include scenarios where multiple state actors conduct concurrent campaigns.
The Road Ahead
As this analysis goes to publication on January 20, 2026—the day of Trump's second inauguration—Iran faces an unprecedented cyber siege. Simultaneously defending against potential U.S. offensive operations while maintaining its own cyber campaigns, all during a domestic crisis that has killed thousands, reveals the limits of even sophisticated cyber powers.
The next phase of this conflict will likely determine whether cyber warfare becomes normalized as an instrument of statecraft or whether new international norms emerge to constrain these capabilities. For security professionals, the lesson is clear: the cyber domain is no longer separate from kinetic warfare—it's the opening act, the main event, and the aftermath all in one.
Organizations must prepare not just for Iranian attacks, but for the broader reality that nation-state cyber operations are accelerating, becoming more destructive, and increasingly integrated with traditional military operations. The question is no longer whether cyber war will come—it's whether defenders can keep pace with the new doctrine being written in real-time across Venezuela, Iran, and beyond.
Obama administration reportedly kept an Iranian cyberattack secret while they were trying to close the Iran nuclear deal pic.twitter.com/AqcB9sbRIV
— FOX & Friends (@foxandfriends) June 12, 2017
Related Reading from CISO Marketplace:
Iran Cyber Operations & APT Groups:
- Iranian Cyber Actors Target Critical Infrastructure Networks: A Growing Threat
- The Cyber Proxy War: How Israel and Iran Are Fighting Through Hacktivist Coalitions
- Iranian Cyber Espionage: Lemon Sandstorm's Prolonged Attack on Middle East Critical Infrastructure
- Iran's Cyber Warfare: The Hack on the Trump Campaign and the Blowback on Iran's Infrastructure
Iranian Maritime & Geopolitical Cyber Operations:
- Digital Siege at Sea: The Escalating Cyber War Against Iran's Maritime Empire
- Former Trump National Security Adviser John Bolton Indicted: Iran Hacked Email Account Containing Top Secret Information
U.S. Cyber Operations & Broader Context:
- Operation Absolute Resolve: A Deep Dive into the Cyber, OSINT, and Intelligence Operations Behind Maduro's Capture
- The Global Cybercrime Empire: Mapping the Underground Economy, Partnerships, and Geopolitical Power Structures
- Countries Shore Up Digital Defenses as Global Tensions Raise the Threat of Cyberwarfare
Key Takeaways for Security Teams:
- Iranian APTs remain active despite domestic crisis, focus on U.S. critical infrastructure
- Satellite internet fundamentally changes information warfare dynamics
- Cyber operations now seamlessly integrate with kinetic military actions
- Basic security hygiene (password management, network segmentation) defeats many sophisticated APT attacks
- Attribution during geopolitical tensions may be unreliable; focus on defense-in-depth
- Prepare for coordinated DDoS campaigns and spear-phishing escalation
- Industrial control systems face heightened risk; remove unnecessary internet connectivity
Sources and Further Reading:
- CISA Iran Threat Overview: https://www.cisa.gov/topics/cyber-threats-and-advisories/advanced-persistent-threats/iran
- CSIS Analysis - Beyond Hacktivism: https://www.csis.org/blogs/strategic-technologies-blog/beyond-hacktivism-irans-coordinated-cyber-threat-landscape
- Treasury Sanctions on IRGC-CEC Actors: https://home.treasury.gov/news/press-releases/jy2292
- Unit 42 Iranian Threat Landscape: https://unit42.paloaltonetworks.com/iranian-cyberattacks-2025/