Nike Confirms Investigation Into Massive 1.4TB Data Breach

WorldLeaks Ransomware Group Claims Theft of Jordan Brand Designs, Supply Chain Data, and Six Years of Internal Documents
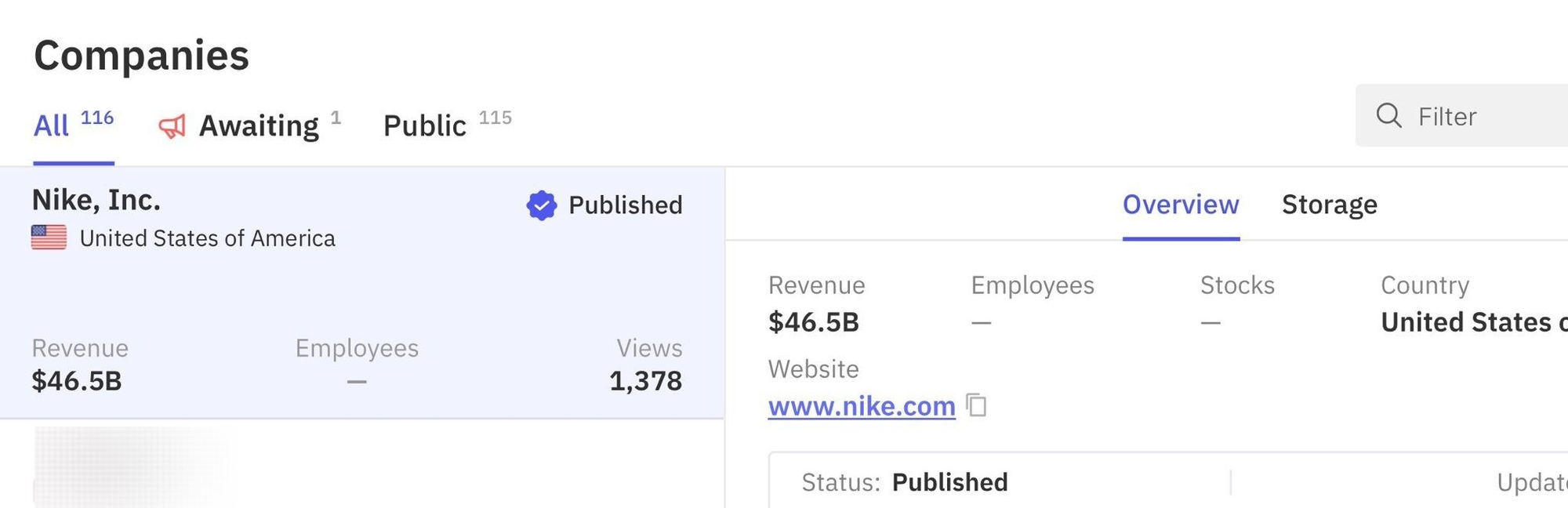
Nike, Inc. has confirmed it is actively investigating a potential cybersecurity incident after the WorldLeaks ransomware group claimed to have exfiltrated 1.4 terabytes of sensitive internal data from the sportswear giant. The alleged breach, first posted to the group's darknet leak site on January 22, 2026, represents one of the largest intellectual property exposures in the athletic apparel industry's history.
"We always take consumer privacy and data security very seriously," a Nike spokesperson told reporters. "We are investigating a potential cybersecurity incident and are actively assessing the situation."
The Scope of the Alleged Breach
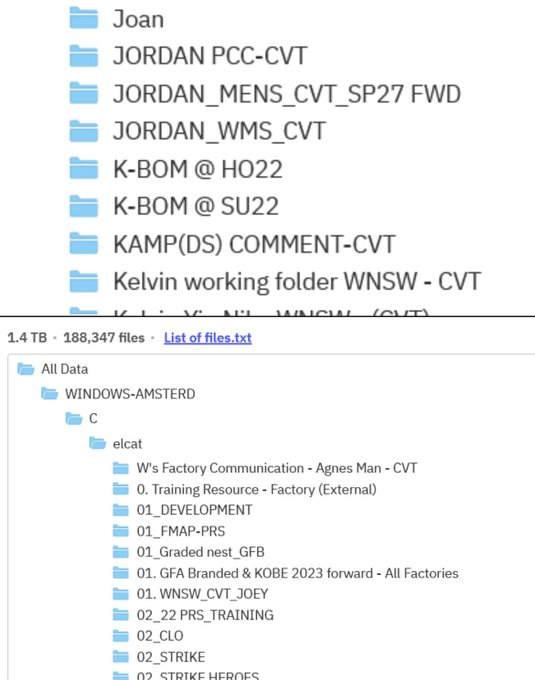
According to listings reviewed by multiple security researchers, WorldLeaks claims to have stolen 188,347 files from Nike's systems. Unlike typical ransomware attacks that target customer databases, this breach appears focused on Nike's core intellectual property and operational infrastructure.
The exposed data reportedly includes:
- Design schematics and tech packs for the upcoming Jordan Brand SP27 collection
- Bills of materials (BOMs) and prototypes
- Complete R&D documentation spanning product creation workflows
- Factory audits and manufacturing partner details
- Garment making process documentation labeled "Training Resource – Factory"
- Internal strategic presentations and employee training materials from 2020 to 2026
Directory names visible in the leaked samples include "Women's Sportswear," "Men's Sportswear," and various product development categories—suggesting the attackers gained deep access to Nike's product creation systems rather than customer-facing infrastructure.
WorldLeaks: A New Breed of Extortion Group
WorldLeaks emerged in January 2025 as a strategic rebrand of Hunters International, a ransomware operation active since late 2023. The group has abandoned traditional file encryption in favor of pure data theft and extortion, reflecting a broader shift in the cybercriminal ecosystem as law enforcement pressure increases and fewer organizations pay for decryption keys.
"From the administrator's perspective, ransomware is no longer profitable and risky," according to threat intelligence findings from Group-IB. The shift to what security researchers call "Extortion-as-a-Service" (EaaS) allows these groups to operate more quietly while still generating significant revenue through data leak threats.
WorldLeaks operates a sophisticated four-platform infrastructure:
- Main data leak site
- Victim negotiation portal with live chat
- Affiliate management panel
- "Insider" journalist portal providing media 24-hour advance access to stolen data
The group has claimed hundreds of victims since its launch, with manufacturing and industrial firms appearing repeatedly among its targets. Previous high-profile claims include Dell, though that company stated WorldLeaks didn't obtain important data.
Implications for Nike and the Industry
The nature of this breach poses unique challenges for Nike. While customer data exposures trigger regulatory notification requirements, the theft of design files, manufacturing processes, and supply chain documentation creates different but potentially more damaging long-term consequences.
Key risks include:
- Counterfeit exposure: Design files and tech packs for unreleased products could enable counterfeiters to bring knockoff merchandise to market before Nike's official launches
- Supply chain intelligence: Factory audit documentation could expose manufacturing partners to targeted attacks or reveal competitive intelligence about production costs and supplier relationships
- Jordan Brand vulnerability: The brand generates billions in annual revenue and maintains cultural significance far beyond its market share—the reported theft of SP27 collection materials is particularly damaging
This incident comes at a challenging time for Nike. The company has been working to re-establish dominance in the athletic apparel market amid market share losses to smaller rivals. Shares were trading flat following the breach disclosure.
Sportswear Industry Under Siege
The Nike breach follows closely on the heels of another major sportswear incident. Under Armour disclosed a breach last week after the Everest ransomware gang leaked data affecting 72.7 million customer accounts. That breach, which occurred in November 2025, exposed:
- Names and email addresses
- Dates of birth and genders
- Geographic locations
- Purchase histories
Under Armour now faces multiple class action lawsuits over the incident.
The pattern suggests sportswear and fashion companies have become attractive targets for cybercriminals. These organizations maintain complex global supply chains with numerous manufacturing partners, creating extensive attack surfaces. The steady flow of new designs moving between headquarters and production facilities means valuable intellectual property constantly traverses networks that may lack enterprise-grade security controls.
Defensive Recommendations
Organizations in similar positions should evaluate their exposure to pure exfiltration attacks, which don't trigger the same detection mechanisms as traditional ransomware.
Key defensive measures include:
- Data Loss Prevention (DLP): Implement solutions capable of detecting unauthorized bulk data transfers
- Network segmentation: Limit lateral movement and restrict access to design and R&D systems
- Behavioral analytics: Deploy tools to identify anomalous access patterns to sensitive file repositories
- Supply chain audits: Conduct regular security assessments of manufacturing partners and facilities
- Zero-trust architecture: Assume breach and verify every access request regardless of source
The shift toward extortion-only attacks means organizations can no longer rely on backup and recovery strategies alone. Prevention, detection, and rapid response capabilities must evolve to address threats that focus on stealing data rather than encrypting it.
Unconfirmed Details
Several key questions remain unanswered:
- Nike has not confirmed the authenticity of the leaked samples or the scope of the breach
- The initial access vector remains unknown
- It's unclear whether Nike's major wholesale partners (Dick's Sporting Goods, Macy's, JD Sports) may have been affected
- Nike declined to comment on whether any ransom demand has been made or payment discussions have occurred
WorldLeaks initially listed Nike on January 22 with a threat to release all stolen files by January 24. The full dataset has reportedly been published, though researchers have noted difficulty downloading and verifying the complete archive.
Looking Forward
This incident underscores a fundamental shift in the threat landscape. Cybercriminal groups increasingly recognize that intellectual property, trade secrets, and operational data can be just as valuable as customer databases—while attracting less regulatory scrutiny.
For organizations whose competitive advantage depends on proprietary designs and manufacturing processes, the threat model must expand beyond traditional data breach scenarios.
We will continue monitoring this situation and provide updates as Nike's investigation progresses and more details emerge about the scope and impact of this breach.
This article was researched and written for the CISO Marketplace ecosystem. For more cybersecurity news and analysis, visit breached.company.





