Operation Anonymous Fénix: Spain's Guardia Civil Dismantles Hacktivist Group That Exploited DANA Disaster
Spain's Guardia Civil has completed the takedown of "Anonymous Fénix," a domestic hacktivist group that launched a sustained campaign of cyberattacks against government ministries, political parties, and public institutions — capping a two-year investigation with the arrest of all four key members.
The operation, announced on February 22, 2026 via the Guardia Civil's official channels, marks a significant win for Spanish law enforcement and the country's cybersecurity apparatus at a time when hacktivist-driven DDoS attacks have become an increasingly disruptive tool for politically motivated actors across Europe.
Who Was Anonymous Fénix?
Anonymous Fénix emerged in April 2023 with a deliberately low profile, slowly building a presence on X (formerly Twitter) and Telegram before escalating into a coordinated campaign against Spanish government infrastructure. The group styled itself as a branch of the globally recognized Anonymous movement — leveraging the brand recognition and mystique of that decentralized collective — while operating as an independent, domestically organized unit with its own command structure, administrator, and moderator.
Their primary weapon was the Distributed Denial of Service (DDoS) attack. Rather than infiltrating systems or stealing data, the group's tactic was volume: flooding government web servers with massive, simultaneous request traffic until targeted sites became completely unavailable to the public. It's a blunt instrument — but an effective one for generating headlines, disrupting citizen-facing services, and amplifying a political message.
Their targets included:
- Websites of Spanish government ministries
- Political party online infrastructure
- Multiple public administration portals at both national and regional levels
- Institutions across several Latin American countries




The DANA Connection: Exploiting a National Tragedy
Anonymous Fénix's activity accelerated sharply beginning in September 2024. The catalyst? Spain's catastrophic DANA (Depresión Aislada en Niveles Altos) weather event that struck Valencia in autumn 2024, causing widespread flooding, deaths, and massive property destruction.
In the emotionally charged weeks that followed, the group dramatically ramped up both its operations and its public posture — attacking websites of public administration entities and justifying those attacks by publicly claiming that government institutions were "responsible for the tragedy." The framing was calculated: a complex, multifaceted disaster involving failures at multiple levels of government was reduced to a single, shareable accusation that fit neatly in a Telegram post.
The DANA period represented Anonymous Fénix's peak activity and highest public visibility. It was also the moment that accelerated the Guardia Civil's investigation timeline.
This pattern — hacktivist groups exploiting high-emotion national events to recruit, amplify, and justify attacks — is one security professionals have watched emerge across Europe, most notably with pro-Russian hacktivist collective NoName057(16) following the Ukraine invasion. Anonymous Fénix applied the same playbook to a domestic political context.
The Arrests: A Two-Phase Operation
Phase One — May 2025: Guardia Civil investigators first identified the group's leadership structure. The administrator and moderator — the two individuals at the top of the organizational hierarchy — were arrested in:
- Alcalá de Henares, Madrid
- Oviedo, Asturias
Devices and digital materials seized during those arrests proved critical. Analysis of the intercepted equipment led investigators to the group's most operationally active members.
Phase Two — February 2026: The two most active hackers in the group were arrested just days before this article's publication in:
- Ibiza
- Móstoles, Madrid
All four suspects now face charges in proceedings coordinated by Spain's Fiscalía de Sala de Criminalidad Informática (Cybercrime Division), the Fiscalía de Madrid, and the Tribunal de Instancia de Madrid.
Digital Infrastructure Dismantled
Beyond the physical arrests, the operation also resulted in the judicial intervention or closure of the group's entire online presence:
- X (Twitter) profile — judicially intervened
- YouTube channel — judicially intervened
- Telegram channel — closed
Removing these channels is arguably as significant as the arrests themselves. For hacktivist groups, social media presence is the oxygen supply — it's how they recruit new "volunteers," amplify attack impacts, and maintain narrative control. Cutting those channels severs the group's ability to reconstitute under new leadership.
Who Supported the Investigation?
The Guardia Civil did not act alone. Key partners included:
- Centro Criptológico Nacional (CCN) — Spain's National Cryptologic Centre, operating under the National Intelligence Centre (CNI), provided technical cybersecurity support critical to identifying the suspects through their digital tradecraft.
- Fiscalía de Sala de Criminalidad Informática — the specialized cybercrime prosecution unit that has been central to Spain's increasingly aggressive posture toward hacktivist and cybercriminal groups.
The Broader Context: Spain Under Siege from Hacktivist Groups
This case does not exist in isolation. Spain has faced a mounting wave of hacktivist activity over the past two years:
- In July 2024, the Guardia Civil arrested three members of the pro-Russian hacktivist group NoName057(16) in Mallorca, Huelva, and Seville for DDoS attacks against NATO-aligned countries — attacks characterized as committed "for terrorist purposes."
- In February 2025, Spanish National Police arrested a lone hacker in Calpe accused of over 40 attacks against NATO, the U.S. Army, Spain's own Guardia Civil and Ministry of Defense, and international organizations including ICAO — with data sold on BreachForums under aliases including "Natohub."
- Meanwhile, cyberattacks against critical Spanish infrastructure operators rose 43% in 2024, according to national security figures.
The pattern reflects a global acceleration of hacktivist and state-adjacent cyber operations targeting democratic governments, with Spain — as a NATO member with visible political tensions around regional autonomy — representing an attractive target environment.
What This Means for Security Professionals
For those in the cybersecurity space, the Anonymous Fénix case offers several instructive takeaways:
DDoS remains a high-impact, low-barrier threat. These attacks require no advanced persistent threat (APT) sophistication. Open-source tools and volunteer "botnets" recruited via Telegram can cripple government web infrastructure. Public sector clients need robust DDoS mitigation as a baseline, not an afterthought.
Social media is part of the threat surface. The group's Telegram and X presence wasn't decorative — it was operational infrastructure for recruitment and amplification. Monitoring for hacktivist mobilization on these platforms can provide early warning before attacks materialize.
Emotion-driven events are recruitment opportunities for threat actors. The DANA exploitation is a textbook example of how national tragedies become recruitment funnels. Security teams supporting public sector clients should anticipate elevated hacktivist activity following major disasters, political controversies, or social unrest.
Operational security failures enable attribution. Despite using a recognized brand (Anonymous) to obscure individual identities, the group's sustained, coordinated activity across stable channels gave investigators a consistent digital trail to follow. Persistence and coordination are enemy of anonymity.
Conclusion
The dismantling of Anonymous Fénix represents a mature, methodical law enforcement response to domestic hacktivism — patient investigation, technical support from national cryptologic assets, and a two-phase arrest strategy that worked from leadership downward. The judicial intervention of the group's social media infrastructure ensures the operation goes beyond arrests to structurally degrade the group's capacity.
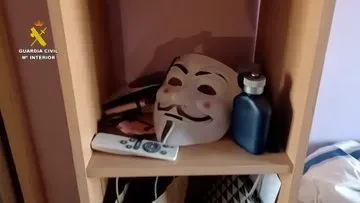
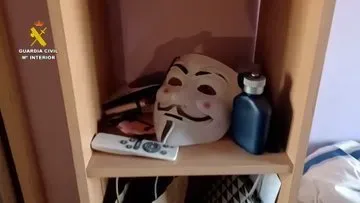
For Spain's growing hacktivist threat environment, it sends a clear signal: digital masks — whether Guy Fawkes or brand Anonymous — don't guarantee anonymity when you operate persistent, coordinated infrastructure over months and years.
#OperacionesGC | Detenidos los cuatro principales integrantes del grupo hacktivista ‘Anonymous Fénix’ por ciberataques contra organismos públicos.
— Guardia Civil (@guardiacivil) February 22, 2026
▶️ Atacaban webs de Ministerios, partidos políticos e instituciones públicas. Se autodenominaban parte del grupo hacker… pic.twitter.com/567JmFvHFH
Sources: Guardia Civil official announcement, Euronews, Infobae España, Prensa Mercosur. Additional context from prior reporting on Spanish cybersecurity operations by BleepingComputer and The Record.
QSai LLC provides cybersecurity consulting, vCISO services, and incident response. Learn more at the CISO Marketplace.





