Operation Roaring Lion: The Cyberattack That Rewrote the Rules of Modern Warfare

On February 28, 2026, the world witnessed something it had never seen before — not just a military strike, but the seamless fusion of kinetic and cyber warfare executed at a scale that no conflict in history has matched. As Israeli F-35s and American cruise missiles carved through Iranian airspace targeting IRGC command centers, a parallel assault was already underway in the digital realm. Within hours, Iran's internet connectivity had collapsed to just 4% of normal traffic levels. The Islamic Republic had gone dark.
This is the deep-dive breakdown of what happened, how it was done, what Iran is likely to do in retaliation, and what every organization operating critical infrastructure needs to do right now.
The Digital Kill Chain: What Went Dark and Why
Internet monitoring firm NetBlocks confirmed the near-total shutdown in real time. This was not a rolling outage or a DDoS blip — it was a sustained, multi-vector collapse of Iran's entire digital ecosystem. The attack reportedly operated across four simultaneous vectors:

Electronic Warfare disrupted GPS, navigation, and radio communications across key military and government networks. IRGC units attempting to coordinate drone and ballistic missile launches found their command-and-control links severed or jammed at the exact moment they needed them most.
DDoS at Scale overwhelmed Iran's public-facing government services. The Islamic Republic News Agency (IRNA) — the regime's primary propaganda arm — was taken completely offline for extended periods. Tasnim News, IRGC-affiliated, experienced severe disruptions and was reportedly hacked to display anti-Khamenei messages directly on government platforms.
Deep Network Intrusions penetrated classified and isolated systems. Even Iran's vaunted "national internet" — a domestically isolated intranet the regime had been building for years precisely to survive this kind of attack — reportedly failed under the combined pressure. Local government apps in Tehran, Isfahan, and Shiraz crashed. Aviation systems were disrupted. Energy infrastructure was reportedly penetrated.
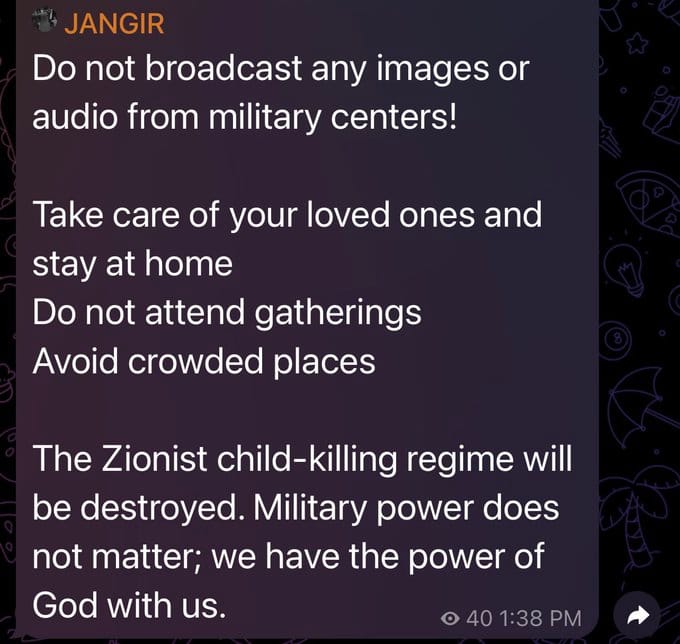
Psychological Operations ran in parallel with the technical assault. Subversive messages appeared on hacked government platforms calling on Iranians to rise up against the regime. Satellite broadcasts — compromised as early as January 2026 — had already been used to air footage calling for the regime's overthrow directly into millions of Iranian households.
The strategic logic was precise: blind Iran's defensive capabilities during kinetic strikes, prevent coordinated counterattacks, isolate leadership from both internal communications and the outside world, and amplify the psychological pressure on a population already deeply dissatisfied with the regime.
This Is Not Stuxnet. This Is the New Doctrine.
To understand how significant this moment is, you have to place it in historical context.
Stuxnet — the joint US-Israeli cyberweapon that destroyed Iranian centrifuges at Natanz around 2010 — operated entirely in the shadows. Attribution took years. The operational goal was deniability and surgical precision against one target set.
NotPetya, the 2017 Russian wiper malware disguised as ransomware that caused over $10 billion in global damage, was plausibly deniable and operated as economic warfare with mass collateral damage.
Operation Roaring Lion is categorically different. This attack was executed in full public view, synchronized with 200 fighter jets and hundreds of cruise missiles, attributed immediately, and apparently designed to be seen. It was not a covert operation — it was a strategic statement about what integrated cyber-kinetic warfare looks like in 2026.
According to threat intelligence produced by Anomali and shared with Defense One, the operation "has destroyed Iran's conventional military options, making cyber operations the regime's sole remaining instrument of asymmetric retaliation." That assessment carries an ominous implication: what the US and Israel did to Iran, Iran will now attempt to do to us.
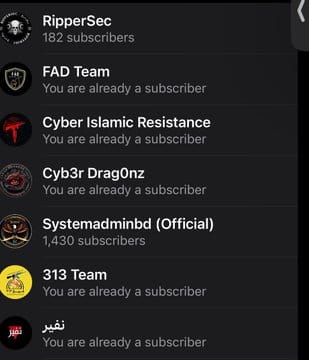
This escalation didn't emerge in a vacuum. We've been tracking the long arc of this conflict on the cyber front for years — from Lemon Sandstorm's prolonged infiltration of Middle East critical infrastructure to the cyber proxy war Iran has been running through hacktivist coalitions. February 28 is the culmination of that escalation arc — not the beginning of it.

Iran's Cyber Arsenal: What SentinelOne's Intelligence Brief Reveals
SentinelOne published an emergency intelligence brief on the same day as the strikes, sent directly to all partners and customers. Their assessment is worth examining in detail because it represents real-time threat intelligence from a team that has tracked Iranian APT groups for years.
Their core finding: Iran presents a mature, well-resourced cyberthreat based on more than fifteen years of experience. This is not a reactive program being stood up in a crisis. These operators were ready before the first missile was fired.
The full toolkit SentinelOne identified includes espionage and credential theft via APT34, APT39, APT42, and MuddyWater against military, civilian, telecom, and academic targets; disruptive and destructive campaigns including wiper malware (Shamoon, MeteorExpress); targeted spearphishing and social engineering at scale; fake hacktivist personas like DarkBit and Cyber Av3ngers for plausible deniability; coordinated disinformation across Telegram, X, and compromised news outlets; internal internet blackouts to control domestic narrative; and proxy ransomware operations that blur the line between state and criminal actors.
That last item is particularly significant. The Iranian cyber actors targeting critical infrastructure networks piece we published documented exactly how Pioneer Kitten and related groups have been collaborating with ransomware affiliates — AlphV, Ransomhouse, NoEscape — receiving cuts of ransom payments in exchange for initial access. This isn't just espionage. It's a self-funding offensive cyber operation.
The Retaliatory Threat Is Real and Imminent
Here is where the story gets directly relevant to every security professional, IT director, and infrastructure operator reading this.
Iran's cyber program is one of the most capable state-sponsored offensive operations on the planet, built over a decade of persistent investment in APT groups operating under both the IRGC and the Ministry of Intelligence and Security (MOIS). Based on the SentinelOne brief and corroborating threat intelligence, here are the primary actors and what they do:
APT34 / OilRig (MOIS-affiliated): Long-dwell espionage operations against government, financial, and critical infrastructure. Known for lateral movement and credential harvesting that gives them persistent access across entire enterprise networks.
APT39 (MOIS-affiliated): Telecom and travel sector targeting for surveillance and tracking of individuals of interest to the regime.
APT42 / TA453 (IRGC-affiliated): The group that compromised John Bolton's email and accessed top-secret classified materials — a case that demonstrated Iran's willingness to go after the highest-value human intelligence targets in the US national security apparatus.
MuddyWater (MOIS-affiliated): Active as recently as February 2026 — days before the kinetic strikes — running attacks on Israeli companies. SentinelOne's detection rules specifically call out MuddyWater DLL sideloading as a priority monitoring item right now.
Peach Sandstorm / HOLMIUM: Deployed a custom multistage backdoor called Tickler against federal/state governments, oil and gas, satellite, and communications sectors. Microsoft researchers documented this campaign targeting US and UAE entities.
Handala: Iran-linked hacktivist group that on February 28 — the same day as the strikes — announced it had breached Clalit Health Services, Israel's largest healthcare network, leaking data on 10,000+ patients and promising "massive cyber attacks in the coming hours." Their message was direct: "We have no red lines for the traitors of the region. Prepare for the destruction of your infrastructure."
CyberAv3ngers: IRGC-linked, previously compromised 75+ Unitronics ICS devices in US water and wastewater facilities. The digital siege against Iran's regional adversaries we covered demonstrates how these actors shift targeting fluidly based on geopolitical direction from Tehran.
SentinelOne's assessment with high confidence: organizations in Israel, the United States, and allied nations are likely to face direct or indirect targeting — particularly within government, critical infrastructure, defense, financial services, academic, and media sectors.
Former CISA official Brian Harrell put it plainly: threat hunters should be working overtime right now. By combining disruptive attacks with psychological operations, Iran will seek to erode public trust in government institutions and project domestic strength during this conflict.
Iran's cyber units were already "activated and retooling before the kinetic trigger," according to Anomali's threat intelligence report. They weren't waiting to see what happened — they were pre-positioned.
The CISA Problem Nobody Is Talking About
There is a critically dangerous institutional gap that compounds every concern above.
CISA — the Cybersecurity and Infrastructure Security Agency, the primary federal body responsible for warning and protecting US critical infrastructure from exactly this kind of threat — is currently operating with sharply reduced staffing due to a funding lapse at the Department of Homeland Security. Its website is reportedly not being actively managed.
As Annie Fixler, director of the Center on Cyber and Technology Innovation at the Foundation for Defense of Democracies, noted: this is a bad time for Washington's cyber agency to be operating with limited staff.
This is not a partisan observation — it is a material operational risk. When Iran-affiliated actors penetrate an ICS in a water treatment facility or a hospital network, the speed of the federal response and the quality of the IOC sharing that CISA facilitates is the difference between contained damage and cascading failure. Right now, that capacity is degraded at the worst possible moment.
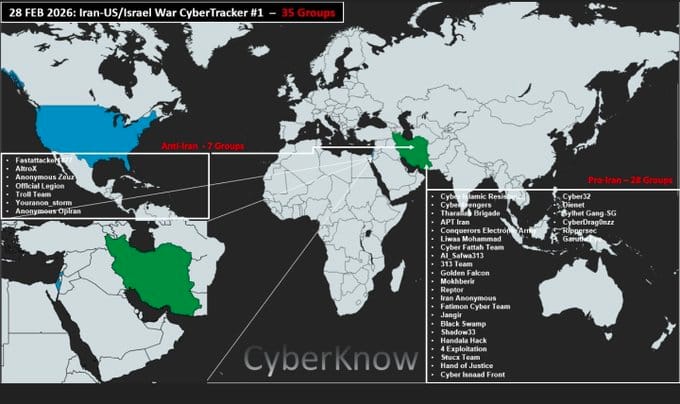
What the Attack Reveals About Modern Cyber Warfare Doctrine
The February 28 operation crystallizes several doctrinal shifts that security professionals need to internalize:
Cyber is no longer a separate domain. It is woven into every phase of kinetic operations. The timeline coordination between the electronic warfare component and the first Israeli airstrikes was not accidental. The goal was to eliminate Iran's ability to respond in the first critical hours. Every future major conflict will include this integration.
Isolated networks are not safe. Iran spent years and significant resources building a domestic intranet precisely to survive Western cyberattacks. It failed. Air-gapped and semi-isolated networks can be compromised through supply chain access, pre-positioned implants, and the kind of deep intrusion campaigns that Iran's own APT groups have been conducting against US networks for years. The same vulnerability exists in reverse.
Psychological operations and cyber attacks are the same operation. Hacking IRNA and displaying anti-regime messaging is not a separate "influence operation" — it is the kinetic component's information warfare support. Organizations need to plan for scenarios where a technical breach is combined with public-facing manipulation of their own communications channels. Iran ran this exact playbook — coordinating influence operations targeting the 2024 US election and the Trump campaign hack alongside overt information operations. The infrastructure and the doctrine are already in place.
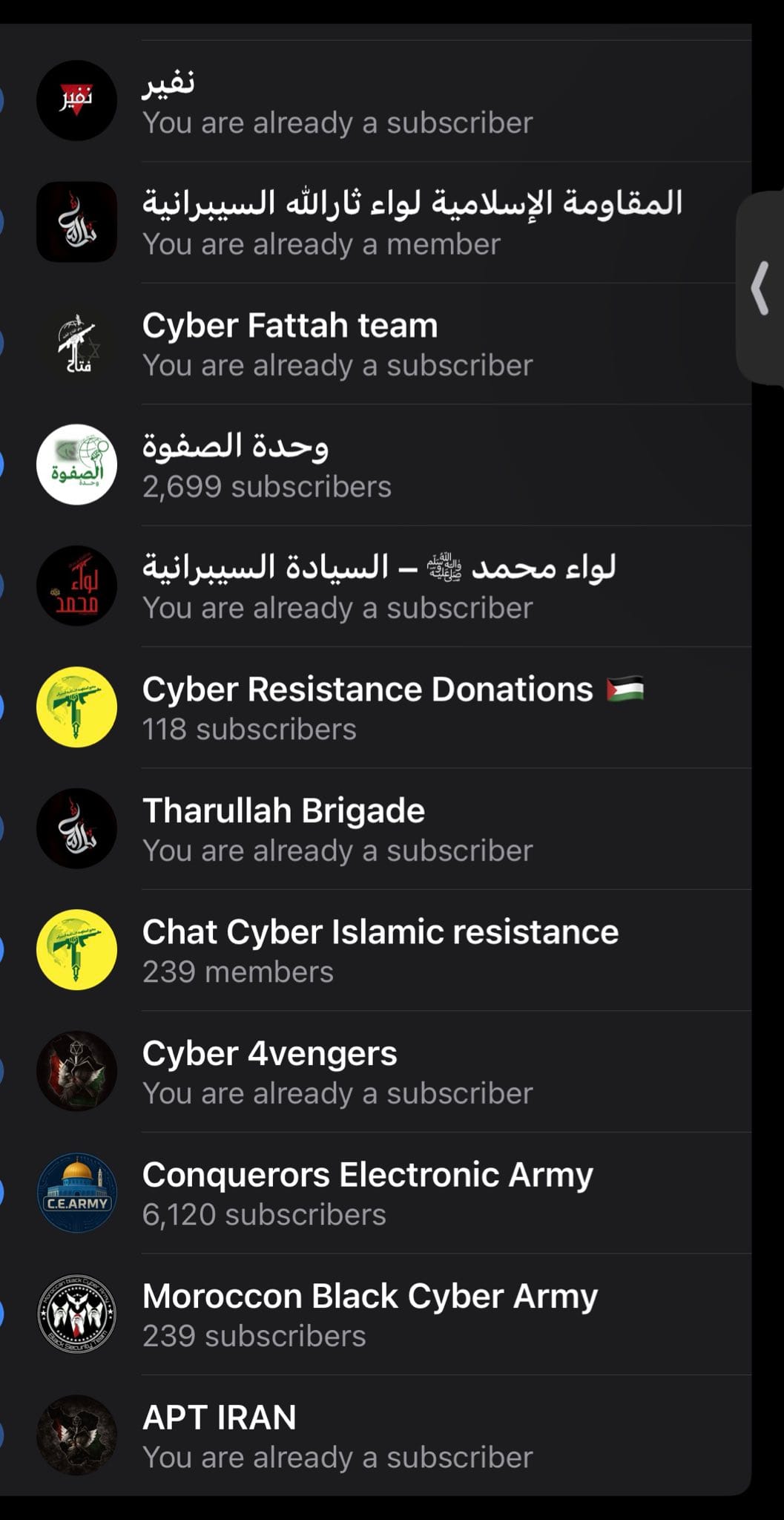
Hacktivist proxies provide deniability at scale. Iran uses groups like Handala, CyberAv3ngers, DarkBit, and others to conduct operations that can be attributed to "independent activists" while achieving state strategic objectives. SentinelOne explicitly flags that the TTPs employed by Iranian hacktivists "increasingly mirror those used by state-sponsored APTs, raising critical questions about capability sharing and formal command-and-control relationships." This model scales. Defending against it requires understanding which "hacktivist" activity is actually state-directed — a distinction we've covered in depth.
The Iranian Retaliation Playbook: Four Vectors to Watch
SentinelOne's intelligence brief outlines four distinct categories of expected Iranian cyber response. This is the most operationally useful framework for defenders right now:
1 — Precision Espionage Operations. Expect escalated targeting of Israeli defense, government, and intelligence networks using spearphishing, credential harvesting, and custom malware deployment. APT34 and APT42 are the primary actors. US military and government organizations are likely secondary targets. Defense contractors and supply chain partners are at elevated risk.
2 — Disruptive and Destructive Tactics. Iran has a well-documented history of wiper malware deployment (Shamoon destroyed 35,000 Saudi Aramco workstations in a single operation in 2012). SentinelOne assesses a high likelihood of similar tactics against US and Israeli utilities and public-facing systems. Key techniques include wiper deployment via fake hacktivist personas, exploitation of unpatched public-facing web services, and scheduled task abuse using LOLBins to execute malware with stealth and persistence. Priority targets: transportation, communications, energy and water utilities, telecom, financial platforms.
3 — Coordinated Influence and Disinformation Campaigns. Iranian-aligned actors will amplify disinformation around civilian impact, military failure, and geopolitical instability. SentinelOne specifically flags anticipated themes including fabricated claims of successful Iranian cyber retaliation, leaked or manipulated documents misattributed to Israeli insiders, and disinformation about US-Israel political division. This is not background noise — it is a coordinated operation designed to degrade public trust and create institutional pressure.
4 — Probing Attacks on US and Israeli Infrastructure. Recent examples include the exploitation of Unitronics PLCs at US water treatment plants — an attack we covered in detail when CyberAv3ngers first emerged — and a shift toward ICS/OT targets that serve retaliatory and signaling purposes. These are often designed to be low-impact yet high-visibility to maximize psychological effect. The Strait of Hormuz and Iran's maritime cyber capabilities represent an additional pressure vector on global energy supply chains.
Immediate Action Items for Security Teams
SentinelOne's brief and corroborating intelligence from CISA, FBI, and NSA point to a consistent set of defensive priorities. These are not optional right now:
Turn on Live Updates and Emerging Threat Platform Rules in your EDR platform. SentinelOne specifically recommends activating Platform Detection Library rules for MuddyWater DLL sideloading, credential dumping (LSASS, shadow copy, NTDS harvesting), tunneling tools (ngrok, Cloudflared), and PowerShell/script abuse — all documented Iranian TTPs.
Audit your external attack surface immediately. Iranian APT groups conduct aggressive reconnaissance before striking. Know what you're exposing before they enumerate it for you.
Patch edge devices without delay. Citrix NetScaler (CVE-2023-3519), F5 Big-IP (CVE-2022-1388), Palo Alto Networks firewalls, Check Point gateways — these are the documented entry points. If you haven't patched, you may already be compromised.
Review MFA configurations end to end. MFA push bombing is a documented Iranian technique. Move to phishing-resistant MFA (FIDO2/passkeys) wherever possible. Audit recent MFA registration changes for signs of tampering — Iranian actors have been documented modifying MFA registrations to establish persistent access.
Assume pre-positioned access. Iran's APT groups are known for long-dwell operations — they get in, stay quiet, and wait for the right moment. Now is the time to run threat hunting exercises against your environment assuming an adversary is already present. SentinelOne's Wayfinder Threat Hunting teams are actively hunting IOCs and TTPs associated with Iranian state-aligned actors across their customer base.
Segment and monitor OT/ICS environments. If you operate industrial controls of any kind, treat this week as a maximum-alert period. Patch and segment exposed ICS components, especially common HMI/PLC vendors. Consider removing or restricting network access to non-critical internet-facing services.
Establish out-of-band communications now. One of the most effective components of the Israeli attack was eliminating Iran's ability to communicate during the crisis. Do you have communications resilience if your primary channels are compromised?
Watch for disinformation targeting your brand. Iran pairs technical attacks with influence operations. Establish rapid communication response protocols. Simulate corporate social media hijacking scenarios. Prepare for account pausing and access reset procedures.
Ensure clear internal escalation paths. SentinelOne specifically recommends establishing direct points of contact for security incidents and communicating posture expectations and escalation paths internally before an incident — not during one.

The Historical Inflection Point
What happened on February 28, 2026, will be studied in military academies and cybersecurity programs for decades. For the first time in history, a nation-state deployed offensive cyber capability simultaneously across electronic warfare, communications infrastructure, critical systems, media, and psychological operations — synchronized to the minute with the largest airborne combat operation in Israeli military history.
The cyber component was not support for the kinetic operation. It was an equal pillar of the assault.
The rules of engagement in nation-state conflict have been permanently rewritten. Cyber is now a first-strike weapon, a force multiplier, and a strategic deterrent all at once. And the adversary that just had this doctrine deployed against it has a mature, patient, and dangerous cyber program of its own — now with nothing left to lose.
Threat hunters should be working overtime right now. That was not hyperbole.
Related Coverage on Breached Company
Iranian Cyber Operations & Threat Actor Deep Dives:
- Iranian Cyber Espionage: Lemon Sandstorm's Prolonged Attack on Middle East Critical Infrastructure
- The Cyber Proxy War: How Israel and Iran Are Fighting Through Hacktivist Coalitions
- Iranian Cyber Actors Target Critical Infrastructure Networks: A Growing Threat
- Digital Siege at Sea: The Escalating Cyber War Against Iran's Maritime Empire
Iran's Offensive Operations Against the US:
- Iran's Cyber Warfare: The Hack on the Trump Campaign and the Blowback on Iran's Infrastructure
- Iranian Interference in the 2024 US Election: A Comprehensive Overview
- Former Trump National Security Adviser John Bolton Indicted: Iran Hacked Email Account Containing Top Secret Information
Broader Nation-State Cyber Warfare Context:
This is a developing situation. Breached Company will continue tracking Iranian retaliatory cyber activity, CISA advisories, and infrastructure threat indicators as this conflict evolves.
Sources: Jerusalem Post, NetBlocks, Wikipedia (2026 Israeli-United States strikes on Iran), Defense One/Nextgov/FCW, Fortune, Inc., CSIS, ITIF, Anomali Threat Intelligence, SentinelOne Intelligence Brief (February 28, 2026)