Orange Cyber Defense Releases v29 of the Ransomware Ecosystem Map: A Decade of Cyber Extortion Visualized
One of the most comprehensive free threat intelligence resources just got a major update—and if you're not using it, you're missing critical context on how ransomware operations actually work.
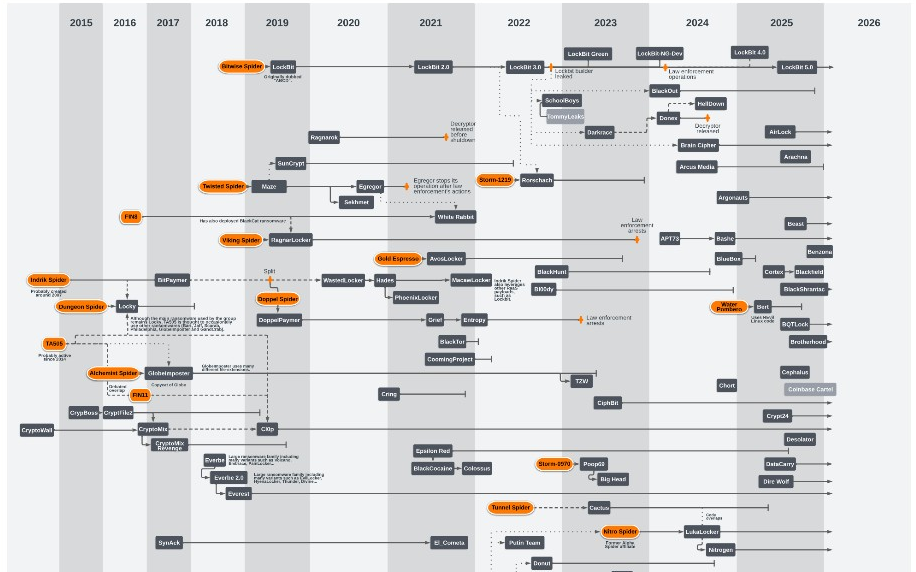
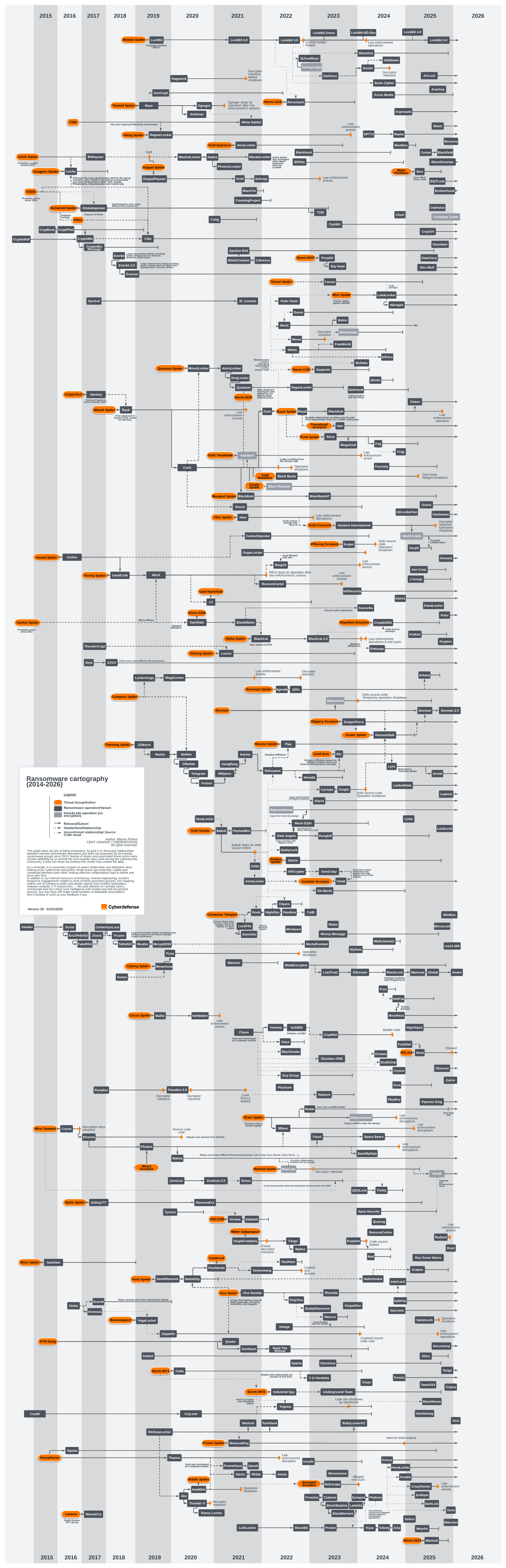
Orange Cyber Defense (OCD) has released version 29 of their Ransomware Ecosystem Map, an extensive visual intelligence resource that charts the relationships, evolutions, and interconnections between ransomware groups from 2014 through 2026. For security teams, threat analysts, and incident responders, this map represents one of the best publicly available tools for understanding how the cyber extortion landscape actually operates.
Why This Map Matters
The ransomware ecosystem doesn't operate in isolation. Groups rebrand. Affiliates jump between operations. Developers sell their code. Former members of disbanded groups resurface under new names. Law enforcement takedowns scatter operators who then reconvene elsewhere.
Understanding these relationships isn't academic—it's operationally critical. When you're responding to an incident attributed to a "new" ransomware group, knowing their lineage can inform your response strategy, help predict their tactics, and identify potential negotiation patterns based on predecessor groups.
The OCD map visualizes these complex relationships in a way that static reports simply cannot. A single glance can reveal that today's emerging threat has direct ties to yesterday's major operation—complete with inherited tooling, tactics, and potentially even the same operators.
What Version 29 Covers
The updated map spans over a decade of ransomware evolution, from the early days of operations like CryptoLocker and TeslaCrypt through the current landscape dominated by sophisticated Ransomware-as-a-Service (RaaS) operations.
Key Elements Tracked
The map documents several types of relationships and attributes:
Threat Actor Groups are displayed chronologically, showing when operations emerged, how long they remained active, and when they went dark—whether due to law enforcement action, voluntary shutdown, or rebranding.
Lineage and Evolution is perhaps the map's most valuable feature. Connection lines trace how groups evolved, split, merged, or directly succeeded one another. You can visually track how code bases, operators, and methodologies transferred between operations.
Collaboration Networks show which groups worked together, shared infrastructure, or maintained affiliate relationships. The ransomware ecosystem is surprisingly interconnected, with developers and operators often maintaining ties across multiple simultaneous operations.
Key Events are annotated throughout the timeline, including major law enforcement actions, significant attacks, and operational changes that affected the broader ecosystem.
Notable Patterns Visible in the Map
Several trends become immediately apparent when examining the visualization:
The Conti Diaspora
The 2022 dissolution of Conti following internal leaks didn't eliminate its operators—it scattered them across the ecosystem. The map traces former Conti affiliates and developers to multiple successor operations, illustrating how a single group's collapse can seed numerous new threats.
LockBit's Dominance and Disruption
LockBit's trajectory through multiple iterations is clearly documented, including the impact of the February 2024 law enforcement action (Operation Cronos) and the group's subsequent attempts to reconstitute. The map shows both LockBit's rise to dominance and the ecosystem effects of its disruption.
The RaaS Model Proliferation
Tracing the timeline from 2015 forward, you can observe the clear shift from individual ransomware operations to the affiliate-based RaaS model. Groups like GandCrab pioneered this approach, and the map shows how this operational model became the dominant paradigm by 2020.
Cyclical Rebranding
Many groups follow predictable patterns: emerge, gain notoriety, attract law enforcement attention, rebrand, repeat. The map makes these cycles visible, helping analysts identify potential rebrand scenarios when a known group suddenly goes quiet while a suspiciously similar new operation emerges.
Intelligence Methodology
OCD is transparent about how this intelligence is compiled and its inherent limitations. The map is built from:
- Direct incident response engagements
- Malware reverse engineering analysis
- Carefully vetted intelligence from trusted sources
- Dark web monitoring and analysis
Importantly, OCD acknowledges the fundamental challenges of attribution in cybercrime. Threat actors are volatile. Relationships are fluid. Collaborations are often deliberately obscured. The map represents their best assessment of key relationships rather than an exhaustive catalog of every ransomware operation since 2014.
This intellectual honesty is refreshing in an industry that often overstates attribution confidence. The map should be treated as a living intelligence product—a framework for understanding relationships rather than definitive proof of specific connections.
Practical Applications
For Incident Responders
When you identify a ransomware variant during an incident, the map can quickly contextualize the threat. Understanding a group's lineage informs decisions about:
- Likely lateral movement techniques based on predecessor TTPs
- Potential decryptor availability from law enforcement actions against related groups
- Negotiation dynamics based on known behaviors of affiliated operations
- Expected data exfiltration and leak site behaviors
For Threat Intelligence Teams
The map serves as a relationship reference when analyzing new threats. When a new group emerges, cross-referencing their technical indicators and operational patterns against the map can reveal likely connections to established operations.
For Security Leadership
Communicating ransomware risk to executives and boards is notoriously difficult. The map provides a visual aid that demonstrates the complexity and interconnected nature of the threat landscape in a way that resonates beyond technical audiences.
For Researchers and Journalists
When reporting on ransomware incidents, the map provides essential context for understanding where a group fits within the broader ecosystem and how they relate to other operations readers may be familiar with.
Accessing the Resource
The Ransomware Ecosystem Map is freely available through Orange Cyber Defense's GitHub repository:
GitHub: https://github.com/cert-orangecyberdefense/ransomware_map
The repository includes high-resolution versions of the map suitable for printing or detailed analysis, along with supporting documentation about the methodology and updates.
Looking Ahead to 2026
The v29 update includes substantial additions heading into 2026, reflecting the continued evolution of the ransomware ecosystem. As law enforcement pressure increases and groups continue to adapt, tools like this map become increasingly valuable for maintaining situational awareness.
The ransomware threat isn't going away—but resources like the OCD Ransomware Ecosystem Map help ensure defenders can keep pace with how that threat evolves and interconnects. If you're not already incorporating this into your threat intelligence workflow, now is the time to start.
V29 Update: 73 New Ransomware Groups Added
The January 2026 update is one of the most substantial releases yet, adding 73 new ransomware operations to the map. This explosion of new entries reflects the continued fragmentation and proliferation of the ransomware ecosystem heading into 2026.
The 2025 Surge
The majority of new additions emerged in 2025, painting a picture of an ecosystem that's become increasingly crowded despite ongoing law enforcement pressure. Notable new entrants include:
Q1 2025 Arrivals:
- CrazyHunter (January)
- World Leaks (January)
- J Group, Kraken, Nightspire, Run Some Wares (February)
- Arkana, Bert, Chaos, Evilbyte, Imn Crew, Mamona, RAlord, Secp0, Skira, VanHelsing, Weyhro (March)
- Cortex, Crypto24, Devman, Satanlock (April)
Q2 2025 Arrivals:
- DataCarry, Dire Wolf, Gunra, TeamXXX (May)
- Ailock, DarkLulz, Global, KawaLocker, Warlock (June)
Q3 2025 Arrivals:
- Beast, BlackNevas, BQTlock, Payouts King, PEAR, Sinobi, Walocker (July)
- Cephalus, Desolator, Obscura, Securotrop (August)
- Arachna, BlackShrantac, Coinbase Cartel, Gentlemen, LockBit 5.0, Lunalock, Radiant, Yurei (September)
Q4 2025 Arrivals:
- BlackField, Brotherhood, Genesis, Kazu, Kryptos, Leaknet, Monolock, Tengu (October)
- Benzona (November)
- Devman 2.0, Minteye, Ms13-089, Osiris, Root, Trident (December)
Already in 2026:
- Aware (January)
- Vect (January)
LockBit 5.0 Emerges
Perhaps the most significant addition is LockBit 5.0, appearing in September 2025. Following the February 2024 Operation Cronos takedown that disrupted LockBit's infrastructure and exposed its administrator, the group has continued attempting to reconstitute. The appearance of a "5.0" version suggests ongoing development despite law enforcement pressure—a testament to the resilience (or stubbornness) of the operation.
Historical Backfill
The update also includes several groups that were active earlier but hadn't been previously mapped:
- Marlock (September 2021)
- Agenda, Mindware, Sparta (2022)
- Werewolves (March 2023)
- SiegedSec (December 2023)
- HelloGookie, HexaLocker, Orca, Prince (2024)
- Anubis (December 2024)
Edits to Existing Entries
Beyond new additions, v29 includes updates to 17 existing group entries: Apos, BlackOut, BlackSuit, Cactus, Cryptnet, Dharma, Embargo, HelloKitty, Hunters International, LukaLocker, Makop, Nitrogen, Phobos, Qilin, Radar, Ransomed, and Thanos. These edits likely reflect new intelligence on relationships, operational changes, or timeline corrections.
What This Proliferation Means
The sheer volume of new groups—over 70 in a single update—reflects several ecosystem dynamics:
Lower barriers to entry. Leaked builders, RaaS affiliate programs, and readily available tooling mean standing up a new ransomware operation requires less technical sophistication than ever.
Fragmentation post-enforcement. Major takedowns scatter operators who then seed new operations. The Conti diaspora demonstrated this pattern, and we're likely seeing similar effects from actions against LockBit, ALPHV/BlackCat, and others.
The rebrand churn. Many "new" groups are likely rebrands of existing operations seeking to shed notoriety or evade tracking. The map helps identify these patterns over time.
Affiliate mobility. The RaaS model means skilled affiliates can easily move between operations or launch their own, contributing to the constant emergence of new names.
For defenders, this proliferation means the threat landscape is more complex than ever—but it also means resources like the OCD map are increasingly essential for maintaining situational awareness.
The Ransomware Ecosystem Map is maintained by the Orange Cyber Defense CERT team. For the latest updates and full-resolution images, visit their GitHub repository.





