Over 1,000 Clawdbot AI Agents Exposed on the Public Internet: A Security Wake-Up Call for Autonomous AI Infrastructure
Executive Summary
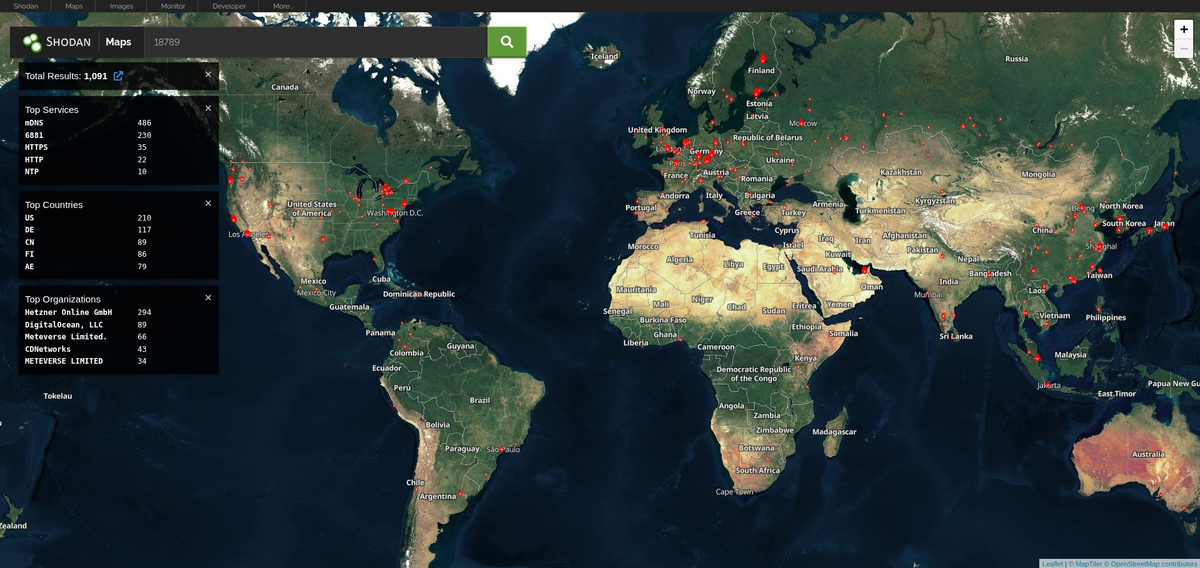
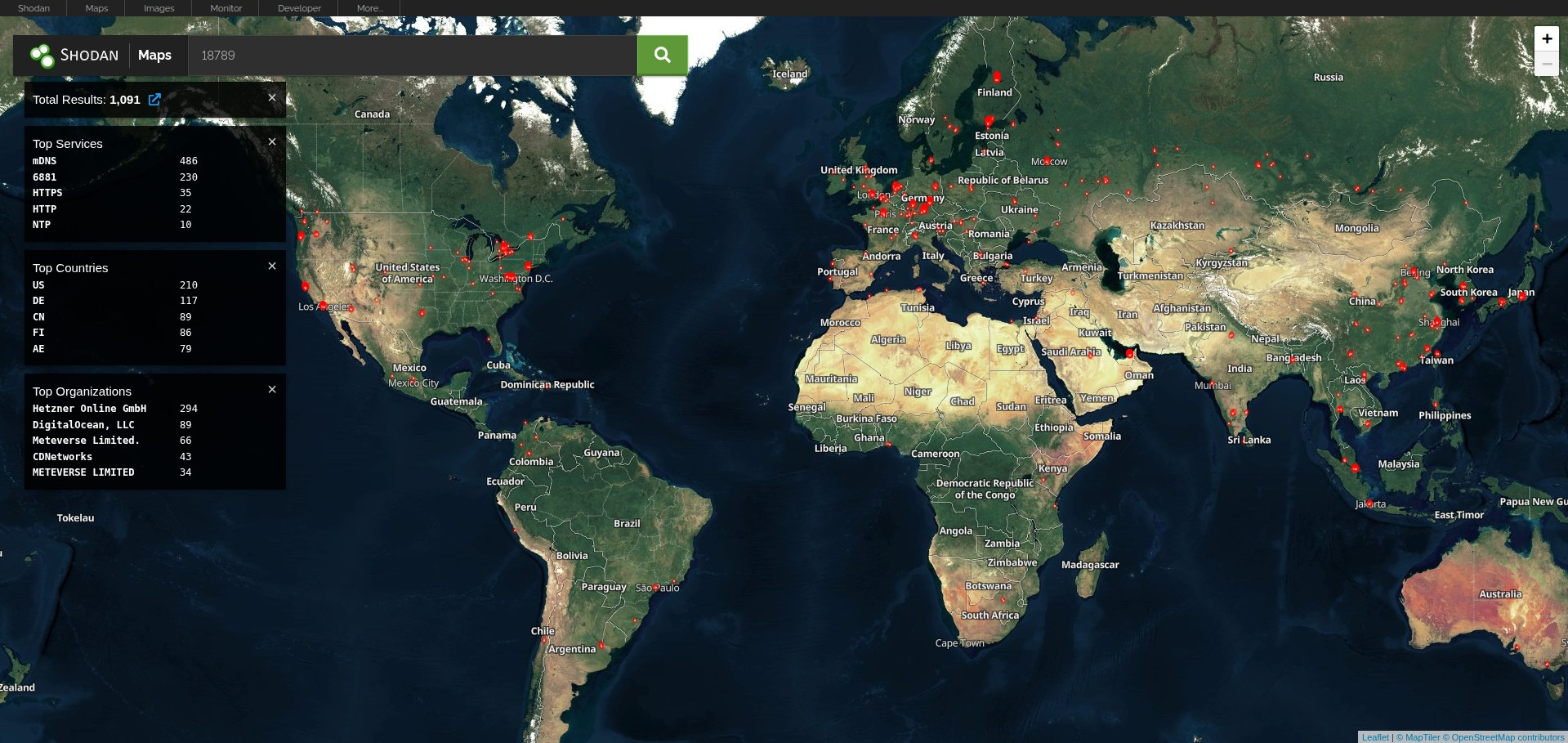
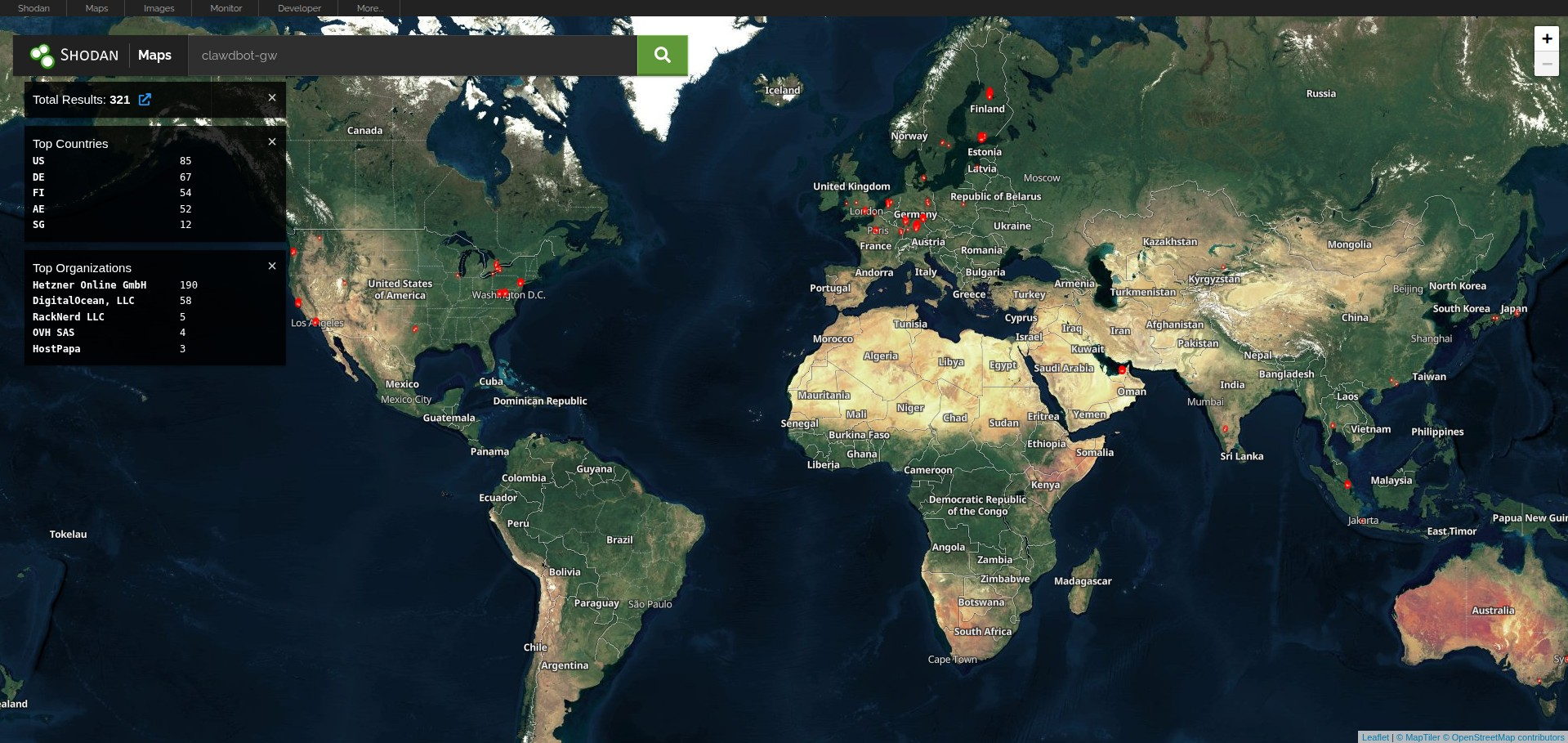
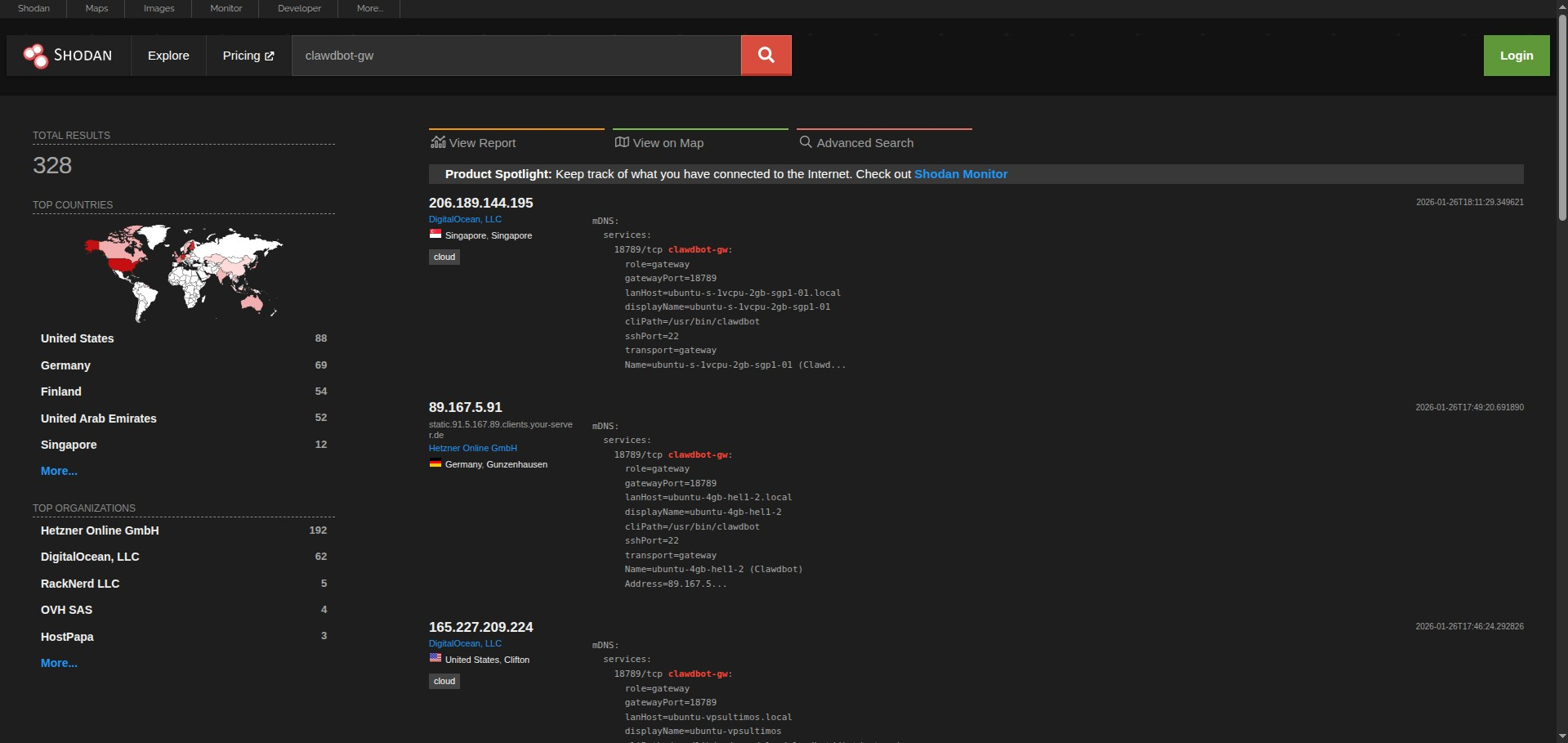
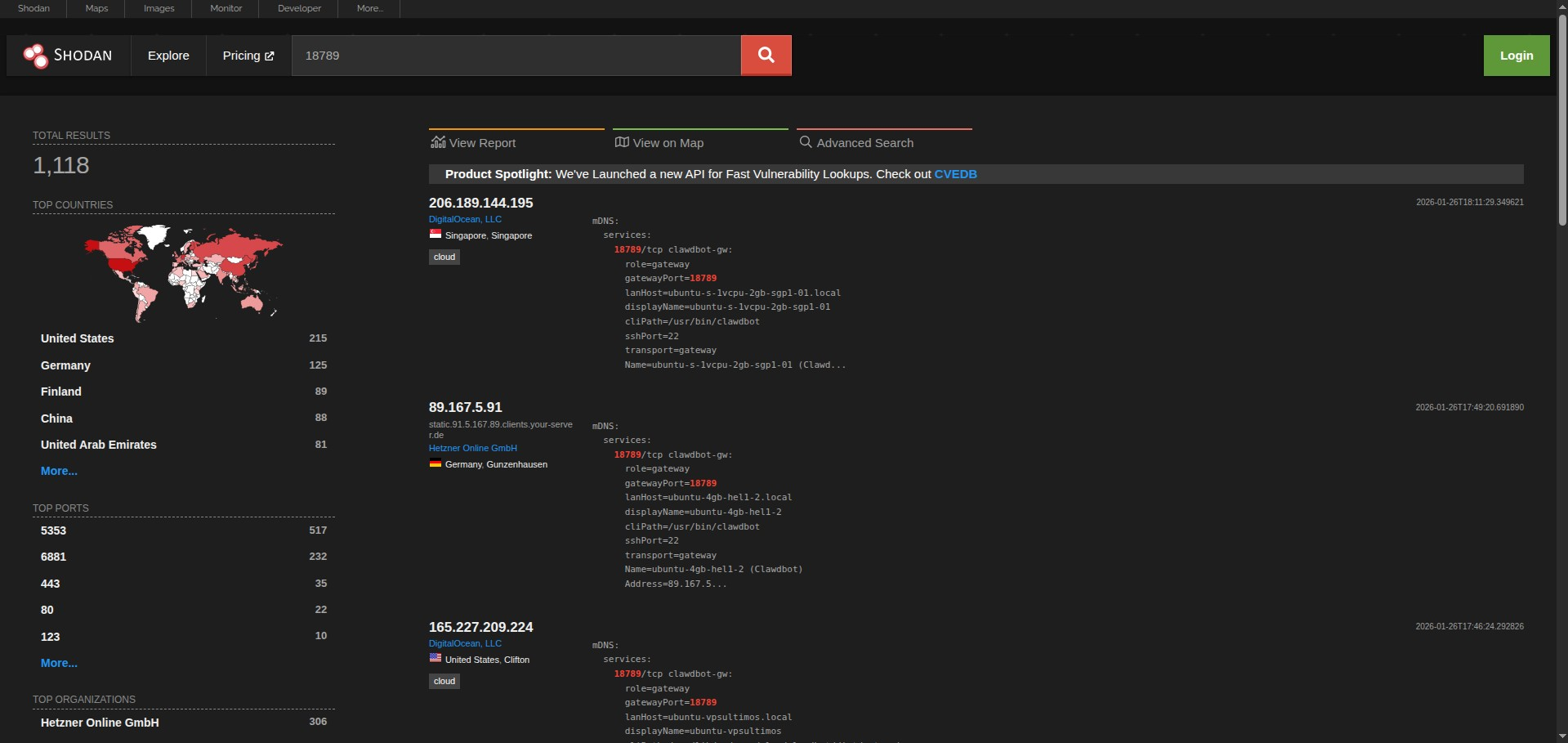
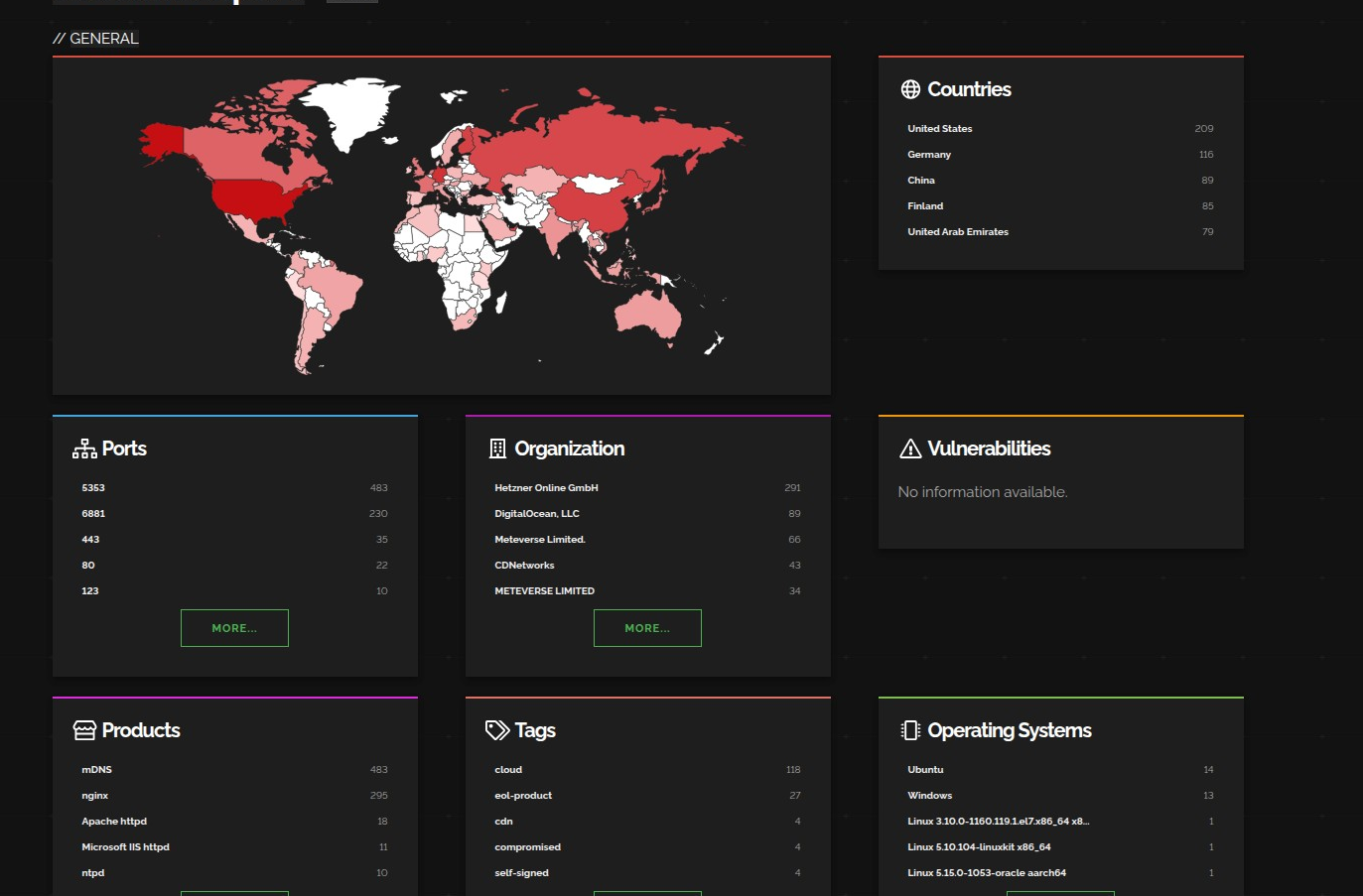
Clawdbot, the rapidly-adopted open-source AI agent gateway, has a significant exposure problem. Our research using Shodan and Censys identified over 1,100 publicly accessible Clawdbot gateway and control instances on the internet. While many deployments have authentication enabled, we discovered numerous instances requiring no authentication whatsoever—leaving API keys, conversation histories, and in some cases, root shell access available to anyone who stumbles across them.
This isn't a vulnerability in Clawdbot itself. It's a predictable pattern that emerges when powerful autonomous systems are deployed without careful security hardening. And given what Clawdbot can access—your messages, your credentials, your filesystem, your browser sessions—the stakes are extraordinarily high.
If you're running Clawdbot, stop reading and run clawdbot security audit immediately. Then come back.
📚 This article is part of our ongoing series on AI Agent Security Risks. As autonomous AI systems proliferate, we're documenting the emerging attack surfaces that security teams need to understand. See the complete series at the end of this article.
What is Clawdbot and Why Should You Care?
Clawdbot has exploded onto the scene as an open-source personal AI assistant that runs locally on your own hardware. Created by Peter Steinberger, it connects frontier AI models like Claude to your messaging platforms—WhatsApp, Telegram, Slack, Discord, Signal, iMessage, Microsoft Teams—and gives the AI the ability to actually do things on your behalf.

The appeal is obvious: instead of copy-pasting between apps, you text your AI assistant and it handles everything. It reads your emails, manages your calendar, searches the web, runs shell commands, controls your browser, and maintains long-term memory across sessions. The lobster mascot (🦞) is cute. The capabilities are genuinely impressive.
But here's what the hype cycle misses: Clawdbot is not a productivity app. It's infrastructure.
This is part of a broader pattern we've been tracking. As we covered in our analysis of agentic desktop agents and local file access security, AI systems that operate on your local machine introduce fundamentally different risk profiles than cloud-based assistants.
Specifically, it's an agent gateway that bridges large language models with real execution environments. Once deployed, it becomes part of your attack surface. The Gateway listens on port 18789 by default, handles message routing, manages credentials, and executes tools. The Control UI provides a web-based admin interface for configuration, conversation inspection, and key management.
When that infrastructure is exposed without proper protection, you're not just leaking data—you're handing over the keys to your digital life.
https://www.youtube.com/results?search_query=clawdbot
The Numbers: What We Found
Using internet scanning platforms, we identified Clawdbot instances across the public internet with concerning results:





