Predatorgate Verdict: Greek Court Sentences Intellexa Founder and Three Others in Historic Spyware Conviction

In a landmark ruling — the first criminal conviction of commercial spyware executives for how their technology was used against clients — an Athens court sentenced four individuals linked to the Predator spyware ecosystem to a combined 126 years and eight months in prison.
ATHENS — A Greek court handed down a historic judgment on Thursday, convicting four individuals connected to the Predator spyware scandal — including two Israeli nationals — marking the first time executives at a commercial surveillance technology firm have been held criminally accountable for the way clients deployed their product against civilians.
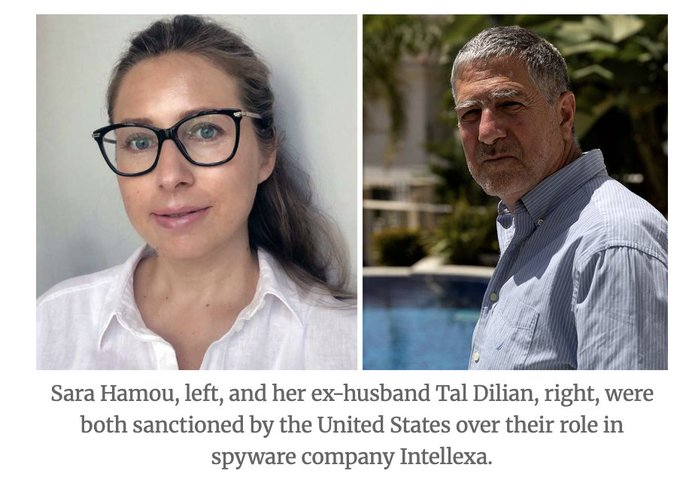
The convicted defendants are Tal Dilian, a former Israeli military intelligence officer and founder of Intellexa; Sara Aleksandra Fayssal Hamou, his business partner; Felix Bitzios, former deputy administrator and shareholder of Intellexa; and Yiannis Lavranos, whose company Krikel allegedly purchased and deployed the Predator spyware. All four denied wrongdoing during the trial. The court rejected all mitigating circumstances, with Presiding Judge Nikos Askianakis citing evidence that the defendants acted with "joint intent" to access the personal data and private communications of their targets.
The sentences total 126 years and eight months combined, with at least eight years required to be served. All four remain free pending appeal, which their lawyers have requested within the statutory 10-day window.
What Is 'Predatorgate'?
The scandal — quickly dubbed "Predatorgate" by the Greek press and "Greek Watergate" internationally — first broke in early 2022 when investigative journalist Thanasis Koukakis discovered that his phone had been simultaneously wiretapped by the Greek National Intelligence Service (EYP) and infected with Predator, a commercial spyware capable of silently infiltrating mobile phones, accessing messages and photos, and remotely activating both the microphone and camera without the user's knowledge.
Months later, Nikos Androulakis — leader of the main opposition PASOK party and then a sitting Member of the European Parliament — discovered his phone had also been targeted. The revelation ignited a political firestorm. Greece's independent telecommunications privacy authority (ADAE) ultimately determined that Predator was deployed against more than 90 individuals, including opposition politicians, government ministers, military officials, journalists, intelligence operatives, prosecutors, and business executives.
A particularly alarming detail emerged during the investigation: many victims were under dual-track surveillance — legally monitored by EYP at the same time they were being hit with illegal Predator spyware. The parallel targeting suggested a level of coordination that the Greek government has consistently denied.
Who Is Intellexa — and What Is Predator?
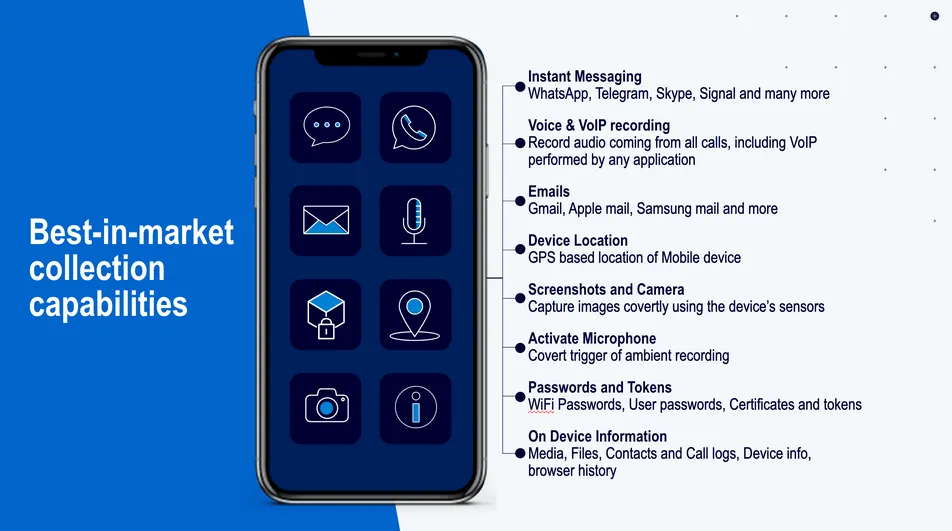
Intellexa is a consortium of surveillance technology companies founded by Tal Dilian following his departure from elite Israeli military intelligence. The company's flagship product, Predator, is a sophisticated commercial spyware tool designed to silently compromise smartphones — both iOS and Android — through zero-click exploits that require no interaction from the target device's owner.
Once installed, Predator grants operators nearly total access: call logs, encrypted messages, emails, photos, GPS location data, and the ability to remotely trigger the device's microphone and camera as a covert listening device. Security researchers from Amnesty International's Security Lab and Citizen Lab have repeatedly documented Predator deployments in multiple countries, including Sudan, Egypt, Madagascar, and Greece.
In 2024, the Biden administration sanctioned Intellexa, several linked entities, Tal Dilian, and Sara Hamou for their role in enabling surveillance of Americans — including government officials and journalists. In December 2024, the Trump administration reversed sanctions against Hamou and two other Intellexa executives, though Dilian remains on the U.S. designation list. Despite this international pressure, Intellexa's infrastructure has proven resilient — security researchers continue to detect active Predator deployments globally.
The Charges and What the Court Found
The Athens court convicted all four defendants on three principal charges:
- Breaching the confidentiality of telephone communications
- Tampering with a personal-data filing system on a repeated basis
- Illegal access to an information system or data
The court additionally ordered authorities to further investigate the case, and stayed execution of the sentence pending appeal — meaning the four walk free for now.
Critically, this is the first criminal conviction anywhere in the world of executives at a commercial spyware company specifically for the manner in which their clients used the technology. Previous legal actions against the surveillance industry have largely focused on civil litigation, sanctions, or export control violations — not criminal accountability for end-use harms.

Political Fallout: Greece's Unresolved Wound
The verdict arrives against a backdrop of years of political turbulence. In 2022, two senior government figures resigned in connection with the affair: Panagiotis Kontoleon, director of the national intelligence service, and Grigoris Dimitriades, the nephew of Prime Minister Kyriakos Mitsotakis, who served as Secretary General of the government. The Mitsotakis administration has consistently denied any involvement in or knowledge of the illegal spyware campaign.
In July 2024, Greece's Supreme Court cleared the state intelligence service and political officials of wrongdoing — a decision that infuriated victims and opposition parties. Androulakis has since appealed that ruling to the European Court of Human Rights, promising that "the fight will continue until all those involved in this murky affair are brought to justice."
The opposition party Syriza issued a statement Thursday declaring that "the government and Kyriakos Mitsotakis himself can no longer hide" and asserting that the conviction reopens the investigation into criminal liability at the highest levels of government. Victims' lawyer Zacharias Kesses told reporters the verdict was "the first conviction for the use of spyware in Greece but is nothing more than a good start" — pointing to serious crimes, including espionage and intelligence service complicity, that he said remain uninvestigated.
Greece Is Not Alone: Europe's Commercial Spyware Crisis
Predatorgate is the most politically explosive iteration of a problem that has metastasized across Europe. Spain's government faced a scandal after the phones of Catalan independence leaders and even Prime Minister Pedro Sánchez were found infected with Pegasus spyware, developed by Israeli firm NSO Group. Hungary deployed Pegasus against journalists, lawyers, and opposition politicians. Poland's government used commercial spyware to target critics and opponents.
In 2022, the European Parliament launched a formal inquiry — the PEGA committee — into the use of commercial surveillance tools across member states. The inquiry documented widespread abuse, recommended significant legislative reforms, and called for an outright ban on spyware use against EU citizens in cases not meeting strict judicial oversight requirements. Implementation, however, has been slow and uneven.
What the Verdict Means for the Surveillance Industry
Amnesty International's Security Lab researcher Rebecca White called Thursday's verdict a potential turning point: "Almost four years since the 'Predatorgate' scandal hit Greece, we are finally seeing consequences for those involved in the abuse of surveillance technology. We hope this landmark ruling signals the end of the era of impunity for the surveillance industry."
That era of impunity has been remarkably durable. The commercial spyware market — estimated to be worth billions of dollars globally — has operated with minimal legal risk despite documented harms to journalists, activists, lawyers, politicians, and ordinary citizens across dozens of countries. The business model has historically insulated vendors from accountability by positioning the government clients as the legal operators and end-users of the technology.
Thursday's verdict directly challenges that model. By finding Intellexa's executives criminally liable for how clients deployed Predator, the Athens court established a precedent — however limited and subject to appeal — that the architects of surveillance-for-hire ecosystems cannot necessarily hide behind their government customers when that technology is used to violate citizens' rights.
Key Takeaways for Security Practitioners and Organizations
For cybersecurity professionals, compliance officers, and organizational leadership, Predatorgate carries several enduring lessons beyond the courtroom drama.
Mobile devices are high-value, high-risk targets. Zero-click exploits like those used by Predator require no user interaction — no phishing link, no malicious attachment. Executives, board members, politicians, and journalists face persistent targeting from nation-state-grade capabilities now available on the commercial market. Mobile device management (MDM), regular OS patching, and tools like Apple's Lockdown Mode represent baseline defenses.
Dual-track surveillance is a real and emerging threat model. The revelation that Predator targets were simultaneously under legal EYP surveillance underscores a sophisticated threat: adversaries using both legal and illegal means in parallel. Organizations should assume that a legally-served wiretap warrant may coexist with unauthorized device compromise.
Third-party and supply chain risk extends to surveillance vendors. Organizations procuring security tools — including network monitoring, endpoint detection, or intelligence services — must scrutinize vendor ethics, export control compliance, and sanction status. The Intellexa/Krikel procurement chain shows how layers of intermediary companies can obscure the true nature and origin of surveillance capabilities.
Legal exposure for technology vendors is growing. Thursday's verdict — combined with NSO Group's ongoing civil litigation in U.S. courts — signals that courts and regulators are increasingly willing to pierce the corporate veil protecting surveillance technology companies. Legal and compliance teams at any organization touching dual-use technology should take note.
The case will now move into an appeals process expected to take months if not years. Whether the conviction ultimately stands — and whether investigations into state-level complicity in Greece are genuinely reopened — will determine whether Predatorgate becomes a true inflection point for accountability in the surveillance industry, or merely a well-publicized footnote.