South Carolina Critical Infrastructure Cybersecurity: 2025 Year in Review
Executive Summary
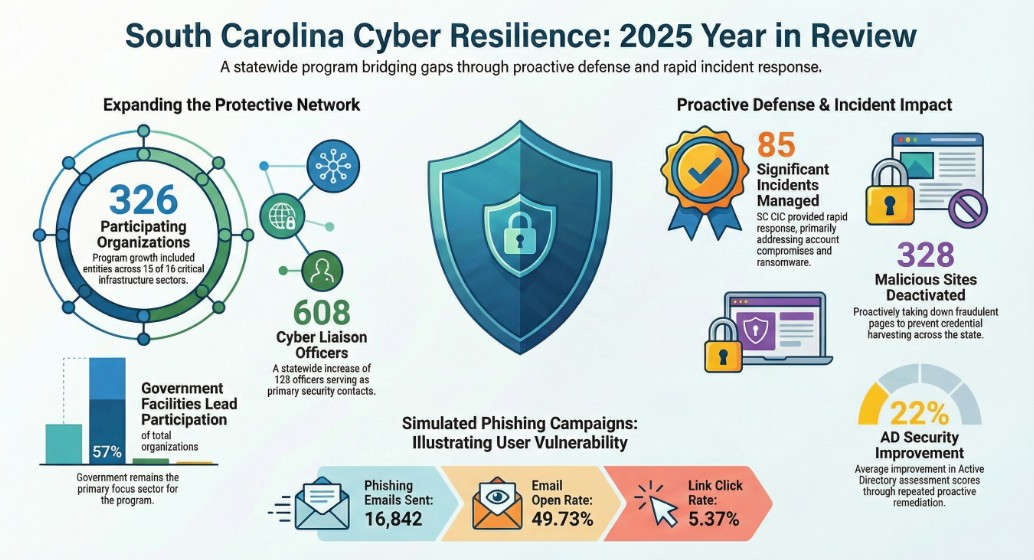
The South Carolina Critical Infrastructure Cybersecurity (SC CIC) program experienced significant expansion and operational impact in 2025. Established in 2017 to bridge cybersecurity gaps for sub-state level infrastructure, the SC CIC now serves as a central hub for intelligence sharing and proactive defense for 326 participating organizations.
Critical Takeaways from 2025:
- Rapid Growth: The program added 47 new organizations and 123 new Cyber Liaison Officers (CLOs), bringing the total statewide network to 608 CLOs.
- Incident Response: The SC CIC responded to 85 significant cyber incidents. The Government Facilities sector remains the most targeted, accounting for 78% of all incidents.
- Dominant Threat Vectors: Account compromise (66%) and ransomware (19%) were the primary incident types. Lack of Multi-Factor Authentication (MFA) on VPNs was identified as a recurring vulnerability in major breaches.
- Proactive Mitigation: Through more than 2,500 malware analyses and dozens of security assessments (Active Directory and Microsoft 365), the program achieved a 22% average improvement in Active Directory security scores among assessed entities.
- Resource Expansion: With a team of 13 specialists, the program is utilizing increased state funding to expand services and address the growing demand for statewide cybersecurity readiness.
AI Defense in Action – Feb 21
40% discount code: CISOMP40

--------------------------------------------------------------------------------
Program Overview and Strategic Growth
South Carolina Critical Infrastructure Cybersecurity (SC CIC) was established by Executive Order in April 2017. Its mission is to facilitate intelligence sharing and improve the cybersecurity posture of critical infrastructure below the state level, providing services at no cost to public and private organizations.
Organizational Reach by Sector
As of 2025, the SC CIC represents 15 of the 16 critical infrastructure sectors identified by Presidential Policy Directive 21 (PPD-21).
Sector | Number of Organizations |
Government Facilities | 185 |
Emergency Services | 29 |
Energy | 22 |
Healthcare & Public Health | 22 |
Water and Wastewater | 21 |
Financial Services | 17 |
Critical Manufacturing | 11 |
Transportation Systems | 8 |
Information Technology | 4 |
Communications | 3 |
Chemical | 2 |
Defense Industrial Base | 1 |
Food and Agriculture | 1 |
Total Organizations | 326 |
Note: The Commercial Facilities sector is currently evaluated on an individual basis as attacks there often result in financial loss rather than the disruption of essential services.
The Government Facilities Sector Breakdown
Because the SC CIC's primary mission focuses on entities below the state level, the Government Facilities sector is the most represented (57% of total organizations).
- Education (K-12): 57 organizations
- City/Town: 40 organizations
- County: 39 organizations
- State Agency: 25 organizations
- Education (Higher): 16 organizations
- County Support: 6 organizations
--------------------------------------------------------------------------------
Collaborative Ecosystem: CLOs and External Partners
Cyber Liaison Officer (CLO) Program
CLOs are the foundation of the SC CIC, acting as primary points of contact within their organizations.
- Total CLOs: 608 (an increase of 123 from 2024).
- Role: CLOs coordinate onboarding, select services, and participate in monthly calls to receive updates on ransomware trends, phishing (such as the "ClickFix" trend), and incident walkthroughs.
External Partner Initiative
Launched in 2025, the "External Partners" program aims to increase information sharing with state associations and federal agencies. Currently, 12 external partners are actively engaged.
--------------------------------------------------------------------------------
2025 Service and Operational Highlights
The SC CIC utilizes a proactive model to prevent incidents before they occur, offering a suite of technical assessments and training.
Security Assessment and Protection Metrics
- Active Directory (AD) Security Assessments: 52 conducted, resulting in a 22% average score improvement.
- Microsoft 365 (M365) Assessments: 63 performed in partnership with Soteria.
- Vulnerability Scanning: 173 engagements.
- Phishing Simulations: ~30 facilitated sessions.
- Endpoint Protection: +22,000 endpoints protected via SLCGP-funded CheckPoint EDR/MDR solutions.
- Malware Analysis: Analyzed +2,500 malware files and malicious artifacts.
Key Engagements and Events
- SC CIC Annual Conference: Hosted 120 CLOs in Columbia, SC. Key topics included Industrial Control Systems (ICS) security, supply chain attacks, and cyber insurance.
- Cyber Security Awareness Month (October): Included a virtual Capture The Flag (CTF) event ("Battle of the Cyber Apocalypse") with 22 participants and a virtual training session on building security awareness programs.
- External Presentations: Staff participated in 40+ events, including the SC Cyber Symposium and the National Governor’s Association.
--------------------------------------------------------------------------------
Incident Analysis and Trends
In 2025, the SC CIC responded to 85 significant incidents. The concentration of incidents in the Government Facilities sector (78%) is attributed to the high volume of sector participation.
2025 Incident Distribution by Type
Incident Type | Percentage |
Account Compromise | 66% |
Ransomware | 19% |
Network Attacks | 7% |
Other | 7% |
Business Email Compromise | 1% |
Threat Intelligence Successes
The SC CIC takes a proactive notification approach to ransomware. By monitoring the deep and dark web for leaked credentials or stolen data, the team often notifies victims before encryption or exfiltration occurs.
- Threat Intel Participation: 229 organizations.
- Identified Leaks: +1,700 leaked credentials identified.
- Takedowns: 328 malicious sites removed.
--------------------------------------------------------------------------------
Significant Case Studies: 2025
1. School District Ransomware (June 2025)
- Vector: A teacher visited a compromised site; a "ClickFix" payload installed a Remote Access Trojan (RAT).
- Activity: Threat actors tampered with EDR agents and exploited insecure AD configurations to gain domain administrator access.
- Impact: Disrupted payroll, SAT/ACT testing, and summer school operations.
2. Utilities Ransomware (June 2025)
- Vector: An IT employee used a domain administrator account to install a malicious package from a typosquatted domain (impersonating PuTTY).
- Activity: Actors moved laterally into the Operational Technology (OT) network, impacting Industrial Control Systems (ICS).
- Impact: Data exfiltration via open-source backup tools followed by environment-wide encryption.
3. Hospital Ransomware (July 2025)
- Vector: Brute-force attack on a VPN lacking Multi-Factor Authentication (MFA).
- Activity: Lateral movement via Remote Desktop Protocol (RDP) leading to domain administrator control.
- Impact: Complete halt in medical operations and full patient diversion to other facilities.
--------------------------------------------------------------------------------
AI Defense in Action – Feb 21
40% discount code: CISOMP40

Looking Ahead to 2026
The SC CIC has identified three primary initiatives for the upcoming year:
- In-Person Engagement: Coordinating more physical events for technical training and networking for professionals and students.
- Personnel Growth: Hiring new positions and providing proactive training for the current 13-member team to meet rising demand.
- Expansion: Pursuing growth in both participating organizations and strategic partnerships at the state and national levels.







