The Cyber Arms Trade: How Commercial Spyware Is Reshaping Global Security

From Pegasus to Pall Mall: Understanding the Growing Market for Offensive Cyber Capabilities
You don't need to manufacture fighter jets to field an air force—you just need the budget to buy them. The same principle now applies to offensive cyber capabilities. Over 80 countries have purchased vulnerabilities, exploits, spyware, and command-and-control infrastructure from private vendors, democratizing access to tools once reserved for the world's most sophisticated intelligence agencies.
While these capabilities can serve legitimate security purposes—from counterterrorism investigations to tracking criminal networks—their misuse introduces systemic risks into the broader cyber ecosystem. The proliferation of critical vulnerabilities, weak governance frameworks, and documented human rights abuses have transformed commercial spyware from a niche defense product into a global security challenge.
https://assets.recordedfuture.com/Executive-Insights/eir-2025-0918.pdf
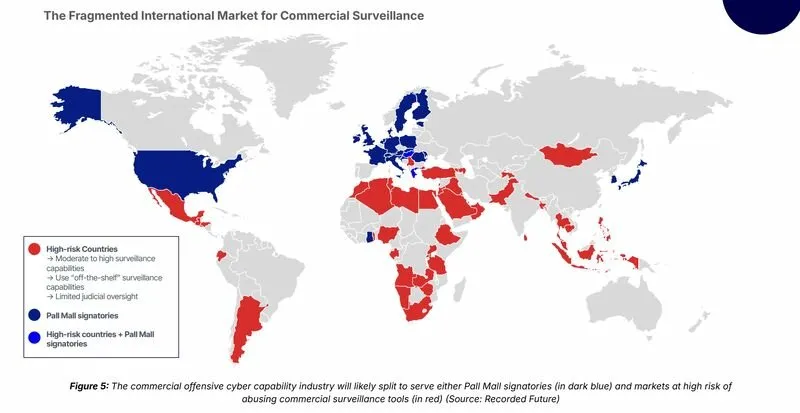
The Pall Mall Code of Practice, signed by 25 countries in April 2025, represents the most significant international attempt to encourage responsible use. But with uneven adoption and fundamentally different governance models emerging across the globe, the commercial surveillance market appears headed toward fragmentation rather than harmonization.
The Anatomy of an Industry
The commercial spyware industry operates through a complex ecosystem that extends far beyond the headline-grabbing vendors. According to research from the Atlantic Council's Cyber Statecraft Initiative, at least 435 entities across 42 countries participate in this market—and that figure likely represents only a fraction of the total ecosystem when accounting for holding companies, subcontractors, individual researchers, and investors.
Commercial offensive cyber capabilities typically comprise three interconnected components. First, vulnerabilities and exploits: many cyber intrusion tools rely on undiscovered (zero-day) vulnerabilities in widely-used software like iOS or Android. When exploited, these vulnerabilities allow operators to deliver malware payloads without detection. Second, surveillance capabilities: the spyware itself, designed to access device cameras and microphones, track keystrokes, exfiltrate data, and monitor location. Third, infrastructure: command-and-control systems including domain registrations, IP addresses, VPNs, and delivery mechanisms that enable operators to communicate with deployed malware.

The industry concentrates heavily in three jurisdictions: Israel, India, and Italy. The Israeli cluster alone—including NSO Group, Candiru, Paragon Solutions, Cognyte, and others—accounts for nearly 44% of entities tracked in the Atlantic Council dataset. The Indian cluster includes firms like Appin Security Group and BellTroX Infotech, while Italian companies such as Memento Labs (formerly Hacking Team) and RCS ETM Sicurezza round out the major hubs.
Notably, of these three primary industry centers, only Italy has signed the Pall Mall Code of Practice or joined the US-led Freedom Online Coalition—highlighting the fundamental challenge facing regulatory efforts.
The Human Cost: From Khashoggi to Kathmandu
The risks associated with commercial spyware fall into two primary categories: proliferation of cyber vulnerabilities and human rights violations. Both have proven difficult to contain.
The proliferation risk materializes when exploits developed for targeted surveillance leak or spread. The most notorious example remains EternalBlue, an exploit allegedly developed by the US National Security Agency that was subsequently used in the WannaCry ransomware attack affecting hundreds of thousands of systems worldwide. More recently, exploits previously deployed by spyware vendors Intellexa and NSO Group were repurposed by Russian state-sponsored threat actors in attacks targeting Mongolian government websites.
The human rights dimension is equally troubling. According to Recorded Future's country risk data, 63% of countries observed using commercial off-the-shelf surveillance tools have limited oversight capabilities—meaning they lack an independent judiciary or oversight body capable of monitoring and restraining surveillance activities.
The case of journalist Jamal Khashoggi stands as the most chilling example. Pegasus spyware, developed by NSO Group, was found on devices belonging to Khashoggi's family and associates in the months surrounding his 2018 murder at the Saudi consulate in Turkey. But the pattern extends far beyond a single high-profile case. Dozens of countries have deployed commercial surveillance tools against political dissidents, journalists, lawyers, and civil society activists. This has occurred not only in authoritarian states but in democracies including Mexico, Greece, Spain, and Poland—the latter seeing the January 2025 arrest of former justice minister Zbigniew Ziobro over allegations of Pegasus misuse.
As recently as February 2025, Amnesty International documented ongoing Pegasus targeting of journalists at the Serbia-based Balkan Investigative Reporting Network, demonstrating that despite years of exposure and litigation, abusive deployments continue.
NSO Group: A Case Study in Industry Dynamics
No company better illustrates the commercial spyware industry's trajectory than NSO Group, developer of the Pegasus platform. The company's journey from celebrated security innovator to sanctioned entity to recent acquisition by US investors encapsulates the contradictions and complexities of this market.
NSO Group developed its first iteration of Pegasus in 2011, marketing it as a tool to help governments combat terrorism and serious crime. The company has consistently maintained that it sells only to vetted government clients and conducts due diligence before licensing its products. According to NSO, it rejected approximately $300 million in potential sales between 2020 and 2021—roughly 15% of new revenue—based on human rights risk assessments.
Yet documented abuses have accumulated steadily. Citizen Lab researchers have tracked Pegasus operations across 45 countries, with at least six—Bahrain, Kazakhstan, Mexico, Morocco, Saudi Arabia, and the United Arab Emirates—previously linked to abusive targeting of civil society. In May 2025, a US jury ordered NSO Group to pay Meta $167.3 million in damages for exploiting WhatsApp vulnerabilities to target 1,400 users across 51 countries. By October 2025, a US court mandated that NSO cease using its spyware on WhatsApp entirely.
The regulatory pressure appeared to have achieved its intended effect—until October 2025, when NSO Group confirmed that a group of US-based investors led by film producer Robert Simonds had acquired a controlling interest in the company. While headquarters will remain in Israel under Defense Ministry supervision, the ownership change raises questions about whether US government agencies might eventually become Pegasus customers rather than adversaries.
The Pall Mall Process: Building Guardrails
Recognizing the escalating risks, the United Kingdom and France launched the Pall Mall Process in February 2024, bringing together governments, companies, and civil society organizations to develop practical frameworks for responsible commercial cyber intrusion capability (CCIC) use.
The April 2025 Code of Practice for States, now signed by 25 countries including the United States, establishes voluntary commitments across four pillars: accountability, precision, oversight, and transparency. Signatories pledge to establish national laws governing CCIC development, purchase, and export; implement know-your-customer requirements to prevent sales to rights-abusing entities; and create processes barring irresponsible vendors from government contracts.
The Code represents genuine progress. It explicitly calls for holding accountable individuals and entities that misuse CCICs through financial restrictions, travel bans, or criminal charges—measures the US has already pioneered through Treasury Department sanctions against Intellexa-affiliated individuals and State Department visa restrictions targeting those involved in spyware misuse.
But significant limitations remain. The Code is voluntary and non-binding, raising questions about enforcement. Less than half of Pall Mall signatories actually use commercial surveillance tools, while even fewer host major offensive cyber firms. And critically, the agreement allows exceptions for domestic law—a loophole that authoritarian-leaning signatories could exploit to legitimize surveillance of political opponents.
Perhaps most fundamentally, the Pall Mall framework addresses only one segment of the global surveillance market. It will have limited influence on countries pursuing alternative approaches—most notably Russia and China.
The Parallel Markets: SORM and Safe City
While Western attention focuses on commercial spyware vendors, two state-backed surveillance ecosystems operate largely outside Pall Mall's reach.
Russia exports its System for Operative Investigative Activities (SORM) to neighboring states and, increasingly, to partners in Central Asia and Latin America. Unlike commercial spyware that compromises individual devices, SORM embeds surveillance capabilities at the internet service provider level, enabling mass monitoring of telecommunications traffic without targeting specific endpoints. This architectural approach makes it fundamentally different from—and in some ways more dangerous than—commercial device-based spyware.
China has pursued a parallel track through Huawei-based "Safe City" systems deployed in several African capitals and beyond. These integrated platforms combine surveillance cameras, facial recognition, and communications monitoring into comprehensive urban surveillance networks. China also maintains a robust vulnerability research ecosystem, accounting for approximately 30% of all detected zero-days in 2024—capabilities that, while not directly commercial, contribute to the global proliferation of offensive cyber tools.
These parallel markets ensure that even aggressive Western regulation cannot eliminate surveillance capabilities for states willing to operate outside US-allied frameworks. The likely result is not the elimination of abusive surveillance but its geographical redistribution.
Salt Typhoon and the "Hack Back" Debate
The commercial spyware discussion has gained new urgency following revelations about Salt Typhoon, a Chinese state-sponsored hacking campaign that Senator Mark Warner has called "the worst telecommunications hack in our nation's history."
First publicly identified in September 2024, Salt Typhoon compromised at least nine major US telecommunications companies—including AT&T, Verizon, and T-Mobile—accessing systems used for court-authorized law enforcement surveillance. The hackers obtained access to communications of senior government officials and political figures, including President Trump and Vice President Vance. By August 2025, the FBI confirmed the campaign had expanded to target over 80 countries and 600 organizations across telecommunications, government, transportation, and military sectors.
The intrusions exploited vulnerabilities that had remained unpatched for years—in one case, a Cisco router flaw documented since 2018. US officials have expressed concern that Chinese operatives may maintain active access to American telecommunications systems even as remediation efforts continue.
Salt Typhoon has renewed discussions around "hacking back"—authorizing private companies to conduct offensive operations against attackers. If permitted, this would dramatically expand the market for offensive cyber tools beyond government purchasers, significantly increasing proliferation risks. Any regulatory framework for commercial offensive capabilities must now account for the possibility of private-sector offensive operations—a scenario that would require entirely new transparency and accountability mechanisms.
The Fragmentation Scenario
Looking forward, the commercial surveillance market appears headed toward fragmentation rather than harmonization. The Pall Mall Code of Practice will likely accelerate this division by creating a regulated tier of vendors willing to operate within signatory frameworks and an unregulated tier deliberately avoiding them.
For vendors, this creates a fundamental business choice: adapt to CoP-compliant markets with their transparency requirements and oversight mechanisms, or pivot toward less-regulated customers willing to pay premium prices for capabilities without restrictions. Some companies will likely attempt to maintain dual tracks, using complex corporate structures to separate compliant and non-compliant operations.
For countries, the fragmentation creates new strategic considerations. States prioritizing human rights alignment will find themselves limited to a smaller pool of vendors subject to export controls and due diligence requirements. States willing to operate outside Western frameworks will have access to Russian, Chinese, and potentially new commercial suppliers emerging in jurisdictions that position themselves as alternatives to the Pall Mall system.
The geography of the industry itself may shift. New spyware hubs could emerge in countries that offer regulatory arbitrage—permissive legal environments combined with technical talent and investor capital. The current concentration in Israel, India, and Italy reflects historical development patterns that new regulatory pressures may disrupt.

Implications for Defenders
Organizations and individuals at elevated risk of surveillance targeting—journalists, lawyers, human rights defenders, political opposition figures, and executives handling sensitive information—should assume that sophisticated commercial spyware represents a realistic threat.
Practical defensive measures include maintaining strict separation between personal and corporate devices; keeping all devices and applications updated to minimize vulnerability windows; enabling security features like Apple's Lockdown Mode designed specifically to reduce spyware attack surfaces; and performing periodic device reboots, which can disrupt some spyware persistence mechanisms.
Organizations should implement mobile device management solutions to enforce security controls across employee devices and invest in security awareness training emphasizing minimal data exposure and spearphishing recognition. For highest-risk individuals, forensic analysis services from organizations like Citizen Lab and Amnesty International's Security Lab can detect spyware infections.
At the enterprise level, security teams should monitor indicators of compromise associated with known commercial spyware infrastructure. Threat intelligence providers including Recorded Future track infrastructure used by vendors like Candiru, enabling detection of potential targeting.

The Road Ahead
The commercial spyware industry stands at an inflection point. Legal accountability is increasing—NSO Group's $168 million judgment demonstrates that vendors can face meaningful financial consequences for enabling abuse. Regulatory frameworks are emerging—the Pall Mall Code of Practice, while imperfect, establishes baseline expectations that did not exist three years ago. Technical countermeasures are improving—Apple's notifications to potential spyware targets have prompted numerous investigations that exposed abusive deployments.
Yet fundamental challenges remain unresolved. The voluntary nature of current frameworks limits enforcement against determined bad actors. The concentration of offensive cyber vendors in non-signatory jurisdictions ensures continued supply to rights-abusing customers. State-backed surveillance systems from Russia and China operate entirely outside Western regulatory reach. And the possibility of private-sector "hack back" operations could dramatically expand the offensive tools market in ways current frameworks cannot address.
For security professionals, the commercial spyware landscape demands ongoing attention not merely as an abstract policy concern but as an operational reality affecting clients, organizations, and potentially their own communications. The cyber arms trade has matured from an emerging threat to an established feature of the global security environment—one that will continue evolving regardless of which regulatory frameworks ultimately prevail.
Key Takeaways
Scale of the Market: Over 80 countries have purchased commercial offensive cyber capabilities from an ecosystem of at least 435 identified entities across 42 countries.
Governance Gap: 63% of countries using commercial surveillance tools lack adequate oversight mechanisms, enabling documented human rights abuses.
Geographic Concentration: The industry concentrates in Israel, India, and Italy—only one of which (Italy) has signed the Pall Mall Code of Practice.
Regulatory Progress: The Pall Mall Code of Practice, signed by 25 countries including the US, represents the most significant international framework to date, though it remains voluntary and non-binding.
Parallel Markets: Russian SORM and Chinese Safe City systems operate outside Western regulatory frameworks, ensuring continued surveillance capability access for states willing to operate outside US-allied systems.
Emerging Pressures: The Salt Typhoon telecommunications breach has renewed discussions around private-sector offensive operations, which would significantly expand the market for commercial cyber tools.
Fragmentation Likely: The commercial surveillance market will likely split between regulated vendors serving Pall Mall-compliant customers and unregulated vendors serving less-restricted markets.

Sources: Recorded Future Insikt Group, Atlantic Council Cyber Statecraft Initiative, Citizen Lab, Amnesty International Security Lab, Lawfare, Freedom House, UK Foreign Commonwealth & Development Office, US Congressional Research Service