The Cyber War in the Shadows: How the 2026 Iran–Israel–U.S. Conflict Is Reshaping the Middle East’s Digital Battlefield

As missile tracks and drone footage dominate the headlines from Tehran to Tel Aviv, an equally consequential battle is unfolding in the shadows of the internet. The 2026 U.S.–Israel kinetic campaign against Iran has triggered a hybrid war that blends missile barrages with large‑scale cyber operations, turning the Middle East into one of the most contested digital frontiers in modern history.
For global enterprises, governments, and critical‑infrastructure operators, the implications are clear: the cyber front is no longer a side effect of conflict—it is a core component of warfare, with spillover risk stretching far beyond the region.
From missiles to megabytes: The birth of a hybrid conflict
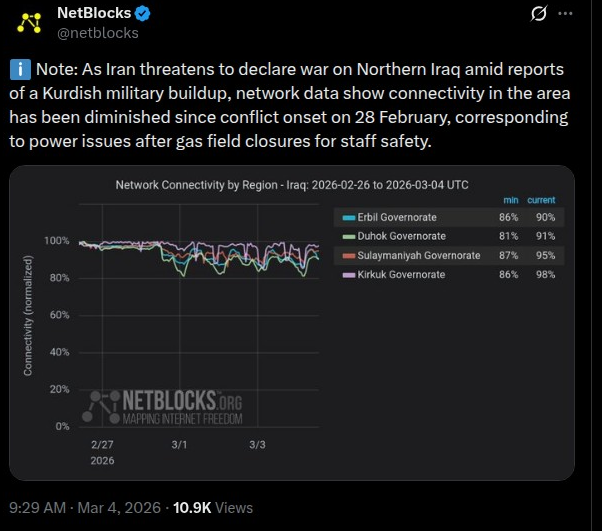
On February 28, 2026, the United States and Israel launched Operation Epic Fury and Operation Roaring Lion, a coordinated strike campaign targeting Iranian leadership, IRGC facilities, and strategic nuclear‑related infrastructure. Almost immediately, Iran responded with ballistic missiles and drones aimed at Israel, U.S. bases, and Gulf‑state targets, while the broader Middle East entered a high‑alert phase.
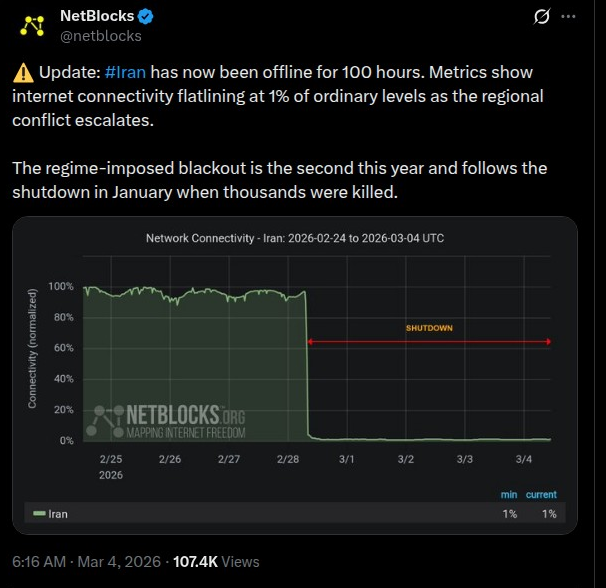
In parallel, reports describe a massive Israeli cyber offensive against Iran, characterized by some as the largest cyber operation in regional history. This campaign reportedly contributed to a near‑total internet blackout in Iran, with nationwide connectivity dropping to roughly 1% of normal levels at its peak.
The result is a dual‑front war: kinetic strikes in the physical world, paired with a cyber‑enabled campaign to disrupt command, control, and communications—and to sow fear and confusion in the information domain.

🟧 #HackTuesday 🟧
— Hackmanac (@H4ckmanac) March 3, 2026
Hack Tuesday: Week 25 Feb - 03 Mar 2026
⚠️556 cyber attacks across 57 countries ⚠️
➡️The most active threat actor last week was NoName057(16) claiming responsibility for 49 cyber attacks.
➡️The USA is the most affected country, accounting for 18.9% of… pic.twitter.com/Knlu0B6EXN
Who is fighting in cyberspace?
The cyber dimension of the 2026 conflict is not limited to state actors. Instead, it is being driven by a triad of threat actors:
- Iranian state and IRGC‑linked APTs
- Iranian cyber programs—historically focused on espionage, disruption, and sabotage—have been active for over a decade, with campaigns targeting Israel, Gulf states, and Western entities.
- In the wake of the 2026 strikes, security firms have observed renewed reconnaissance, phishing, and credential‑theft campaigns linked to long‑established Iranian APT groups, often operating through fronted or proxy infrastructure.
- Pro‑Iran and pro‑Palestine hacktivist collectives
- Between February 28 and March 1, more than 150 hacktivist incidents were recorded, dominated by DDoS attacks, website defacements, and so‑called “data‑leak” operations.
- Groups such as Handala Hack Team, Cyber Islamic Resistance Axis, and others have publicly claimed intrusions into Israeli energy firms, industrial‑control systems, and Jordanian critical‑infrastructure assets.
- Pro‑Russian and other aligned actors
- Some pro‑Russian cyber personas have joined the fray in support of Iran, leveraging existing tools and infrastructure to amplify DDoS and defacement campaigns against regional targets.
This multi‑actor ecosystem means that even if formal state‑level cyber operations are constrained, proxy and hacktivist fronts can continue disruptive activity—often with little attribution and minimal direct exposure.
🟧 #HackTuesday 🟧
— Hackmanac (@H4ckmanac) March 3, 2026
Hack Tuesday: Week 25 Feb - 03 Mar 2026
⚠️556 cyber attacks across 57 countries ⚠️
➡️The most active threat actor last week was NoName057(16) claiming responsibility for 49 cyber attacks.
➡️The USA is the most affected country, accounting for 18.9% of… pic.twitter.com/Knlu0B6EXN
Tactics, techniques, and targets
The cyber‑attack patterns observed so far reveal a mix of disruption, espionage, and psychological warfare:
- DDoS and website defacements
- Hacktivist groups have flooded government portals, financial institutions, and telecom providers with denial‑of‑service traffic, temporarily degrading availability and undermining public confidence.
- Defacements often carry political messaging, linking the cyber operations directly to the kinetic war narrative.
- Targeted intrusions and ransomware‑style attacks
- Some Iran‑linked groups claim to have infiltrated industrial‑control systems at Israeli ICS providers, raising the specter of sabotage against critical infrastructure.
- Others assert ransomware‑style deployments against energy firms, warning of “massive cyber attacks” pending wider escalation.
- Exploitation of exposed edge devices and VPNs
- Analysts note a rise in exploitation of VPN appliances, firewalls, and web‑facing applications—a pattern consistent with prior Iranian APT tradecraft.
- Persistent web shells and credential‑theft campaigns suggest long‑term persistence is being prioritized alongside short‑term disruption.
- Information operations and cyber‑enabled propaganda
- Cyber operations are being paired with disinformation campaigns, where leaked or re‑hashed data is repackaged to amplify fear and confusion.
- This fusion of cyber and information operations makes attribution harder and public‑sector trust more fragile.

A pro-Iran aligned cyber group claims it infiltrated Israeli government & military communications infrastructure, alleging breaches of 160+ data centers and disruption of internal networks. Claims include impact on defense systems, but remain unverified. https://t.co/KtwCqKBsYO pic.twitter.com/RScVeu4Hdk
— FalconFeeds.io (@FalconFeedsio) March 3, 2026
Spillover risk: When the region’s cyber war becomes your problem
Perhaps the most important takeaway for global organizations is this: you do not need to be in the Middle East to be targeted.
- Supply‑chain and regional dependencies
- The UK’s National Cyber Security Centre (NCSC) has already warned that organizations with regional supply chains, cloud dependencies, or OT‑linked partners should urgently review their postures.
- Similar advisories have come from CISA, the NSA, and the FBI, urging operators of critical infrastructure to disconnect exposed operational technology from the internet, adopt deny‑by‑default zoning, and harden VPN and edge‑device configurations.
- Cloud and infrastructure providers under pressure
- Amazon Web Services confirmed that drone strikes physically damaged three data center facilities in the UAE and Bahrain, contributing to service‑degradation and highlighting the intersection of physical and cyber risk.
- Regional cloud and hosting providers have reported sustained DDoS and intrusion‑attempt waves, forcing them to invest in additional mitigation capacity.
- Financial and energy sectors in the crosshairs
- Banks in Kuwait, Jordan, and the broader Gulf have been targeted with DDoS and fraud‑related campaigns, even as customer‑facing services remain largely operational.
- Energy and utilities sectors—already accustomed to APT‑style targeting—are now explicitly warned of potential sabotage or ransom‑style operations tied to regional escalation.
🚨🇮🇱 It appears that Iranian hackers broke into Israel's Nuclear Research Center and stole 197 gigabytes of data.
— Hackmanac (@H4ckmanac) November 11, 2024
Any confirmation? pic.twitter.com/RRUVsr4R1D
Israel detained CNN crew and reporter, after they were released they said that Israeli authorities were able to access their phones without using a password or Face ID before taping the cameras.
Tape was placed over the phone camera of the journalist, with numbers written on the tape.
What this means for your organization’s security posture
Given the current landscape, a defensive reset is warranted, especially for organizations with any of the following:
- Internet‑facing assets in or near the Middle East
- Cloud or colocation dependencies in the Gulf
- Supply‑chain or OT‑linked partners in critical‑infrastructure sectors
Key mitigation steps include:
- Reduce internet‑facing exposure
- Limit or remove public access to operational technology (OT) and industrial control systems.
- Harden VPNs, firewalls, and web‑facing apps with multi‑factor authentication, zero‑trust zoning, and strict egress controls.
- Strengthen monitoring and detection
- Increase logging and monitoring for unusual login patterns, credential‑dumping, and lateral‑movement‑style behavior, which are hallmarks of Iranian APT activity.
- Apply behavioral analytics to detect early‑stage reconnaissance and benign‑looking phishing campaigns that may precede more disruptive operations.
- Prepare for high‑velocity incident response
- Ensure runbooks exist for DDoS, ransomware‑style incidents, and OT‑related breaches, with clear escalation paths to legal, comms, and executive leadership.
- Pre‑stage backups and segmentation plans to minimize business impact if a disruptive cyber operation does succeed.
- Review third‑party and supply‑chain risk
- Map dependencies on cloud providers, regional hosting, and critical‑infrastructure partners, and confirm their own incident‑response and mitigation capabilities.

🚨🚨 Iran and Israel War Cybertracker #2 🚨🚨
— CyberKnow (@Cyberknow20) June 17, 2025
17 June 2025 update for hacktivist activity related to the ongoing #iranisraelwar
- There are already over 100 hacktivist groups who are active from this geopolitical flashpoint.
- There are four pro-India hacktivist groups… pic.twitter.com/v8KEnbvcbd
The long‑term shape of the Middle East’s cyber order
The 2026 Iran–Israel–U.S. conflict is not an isolated incident. It sits within a broader trajectory of cyber escalation across the Middle East, where Tehran, Riyadh, Abu Dhabi, and Tel Aviv have all invested heavily in cyber capabilities.
What is new is the scale of cyber‑enabled disruption tied to kinetic operations, the blurring of APT and hacktivist lines, and the explicit integration of cyber effects into broader war plans.
For cybersecurity professionals, this reinforces a simple truth: in the 2020s, all major conflicts are cyber‑enabled conflicts. The Middle East is simply the most visible theater of that shift.
🚨 🇮🇷 NEW RESEARCH: Mapping Iranian APT Infrastructure During Geopolitical Escalationhttps://t.co/MRizgF4R3W
— Hunt.io (@Huntio) March 4, 2026
Tensions between the U.S., Israel, and Iran have escalated in recent weeks. When geopolitical conflicts reach this level, cyber operations rarely lag behind.
In this…
How to stay ahead
As the bombs and missiles eventually subside, the cyber risk will persist. State‑linked groups will seek to maintain footholds, hacktivist communities will keep leveraging the conflict for visibility, and criminal actors may exploit the chaos for opportunistic attacks.
Organizations that treat this as a timeout‑worthy event rather than a one‑off crisis will be better positioned to withstand the next wave. That means:
- Embedding conflict‑aware threat modeling into your security strategy
- Treating geopolitical escalation as a routine input to your risk assessments
- Building partnerships with regional and global threat‑intelligence providers to stay ahead of evolving Iranian and proxy‑linked tactics
The war in the Middle East may be measured in missile strikes and casualty counts, but the cyber war will be measured in resilience, preparation, and response. For your blog’s audience—cybersecurity leaders, architects, and operators—this is the challenge of the decade.