Third Time's a Pattern: Panera Bread's Decade of Data Disasters

The fast-casual chain has now suffered three major data breaches since 2018—and the lawsuits are piling up
When does a data breach stop being an "incident" and start being institutional negligence?
For Panera Bread, that question isn't hypothetical anymore. It's the central thesis of three class action lawsuits filed in the final days of January 2026, after the notorious cybercriminal group ShinyHunters breached the company's systems and made off with approximately 14 million records affecting 5.1 million customers.
This is Panera's third major security disaster in eight years. The first, in 2018, exposed 37 million customer records through a website vulnerability that went unpatched for eight months—even after researchers warned the company directly. The second, in March 2024, was a ransomware attack that knocked out the chain's entire IT infrastructure and compromised the Social Security numbers of 147,321 employees.
Now, in 2026, ShinyHunters has demonstrated just how little Panera learned from those previous catastrophes. The data was stored unencrypted. The attack vector—voice phishing targeting single sign-on credentials—is well-documented and increasingly common. And once again, the company's response has been characterized by opacity and understatement.
At a certain point, you have to ask: is Panera Bread a restaurant company with a cybersecurity problem, or a cybersecurity liability that happens to sell sandwiches?

What Happened This Time: ShinyHunters and the SSO Vishing Campaign
The Panera Bread data breach 2026 began, like so many modern attacks, with a phone call.
In January 2026, operatives affiliated with ShinyHunters—one of the most prolific and sophisticated cybercriminal groups operating today—called Panera employees posing as IT support staff. The attackers were smooth, professional, and prepared. They knew enough about Panera's internal systems to sound legitimate. And they had a specific target: Microsoft Entra single sign-on credentials.
Single sign-on (SSO) has become the skeleton key of modern enterprise security. When properly implemented, it streamlines authentication and reduces password fatigue. When compromised, it gives attackers the keys to the kingdom—often with persistent access that survives individual password resets.
ShinyHunters' vishing (voice phishing) campaign was devastatingly effective. According to the group's own statements to BleepingComputer and The Register, the attack proceeded in a predictable but difficult-to-defend-against pattern:
- Initial Contact: Attackers called Panera employees, impersonating internal IT support
- Credential Harvesting: Victims were convinced to enter their credentials on convincing fake SSO login pages
- MFA Bypass: Real-time phishing kits captured not just passwords but multi-factor authentication tokens simultaneously
- Session Hijacking: Stolen session tokens allowed attackers to bypass authentication controls entirely
This wasn't a one-off attempt. Panera was simply one target in what threat intelligence firms have described as an "ongoing" campaign affecting over 100 organizations. Other confirmed victims include Match Group (the parent company of Tinder, Hinge, and OkCupid), SoundCloud, Crunchbase, Betterment, CarMax, and Edmunds.
The campaign was sophisticated enough to warrant a formal warning from Okta on January 22, 2026, and has been tracked by Mandiant/Google Threat Intelligence under the designations UNC6040 and UNC6240. Silent Push threat researchers have documented the technical infrastructure, noting the use of custom phishing kits designed specifically to defeat multi-factor authentication in real time.
By late January, after failed ransom negotiations with Panera, ShinyHunters did what they always do: they leaked the stolen data on their dark web leak site, accompanied by a terse note explaining that "these files were leaked on the ShinyHunters DLS because the victim did not pay a ransom or cooperate and comply with the ShinyHunters group."
The compressed archive totaled 760 megabytes. Inside were the personal details of millions of Americans who had simply wanted to order a bread bowl.
What Was Stolen: 14 Million Records, Zero Encryption
The scope of the ShinyHunters Panera breach is significant, though Panera itself has been reluctant to provide specific figures. According to Have I Been Pwned—the authoritative breach notification service operated by security researcher Troy Hunt—the stolen dataset contains:
| Metric | Count |
|---|---|
| Total Records | ~14 million |
| Unique Accounts | 5.1 million |
| Unique Email Addresses | 5.1 million |
| Panera Employee Emails | 26,000+ |
The types of personal information compromised include:
- Full names
- Email addresses
- Phone numbers
- Physical/home addresses
- Account details
- Birth dates
- Usernames
Panera has emphasized—perhaps hoping it would provide some comfort—that login credentials, payment card information, and financial data were not part of the breach. This is true, but it misses the point entirely. The stolen data is more than sufficient to enable identity theft, targeted phishing attacks, and long-term exploitation.
But here's where the Panera Bread data breach 2026 goes from unfortunate to indefensible: according to the class action lawsuits filed against the company, the stolen data was not encrypted.
The Cipriani lawsuit is explicit on this point: "Defendant failed to adequately protect the plaintiff's and class members' private information—and failed to even encrypt or redact this highly sensitive information."
This is 2026. Database encryption is not cutting-edge security research. It's table stakes. It's been table stakes for over a decade. The fact that Panera was storing 14 million customer records in plain text—accessible to anyone who could reach the underlying database—represents a fundamental failure of security hygiene.
When data is encrypted at rest, a breach still represents a security failure, but the stolen data is at least scrambled. Attackers must invest significant additional effort to make it usable. When data is stored in plain text, a breach immediately yields actionable intelligence. There's no buffer, no second chance, no time to mount a response before the damage is done.
Panera had every reason to know better. This is the same company that, in 2018, was found to have been exposing customer data in plain text on their website for eight months. They settled a class action over that incident. They presumably implemented reforms. And yet here we are again, with another unencrypted database, another catastrophic breach, and another set of customers whose personal information is now circulating on the dark web.
The Lawsuits: Three Class Actions and Counting
The Panera class action lawsuit machinery activated almost immediately after ShinyHunters went public with their claims. Within four days of the breach disclosure, three separate lawsuits had been filed in the U.S. District Court for the Eastern District of Missouri:
| Case | Plaintiff | Case Number | Filed |
|---|---|---|---|
| First | Armen Keleshian | Unknown | January 29, 2026 |
| Second | Michael Cardin | 4:26-cv-00125 | January 30, 2026 |
| Third | Paige Cipriani | 4:26-cv-00126 | January 30, 2026 |
All three lawsuits advance similar legal theories, alleging that Panera failed in its fundamental duty to protect customer data:
Negligence: The lawsuits argue that Panera failed to implement reasonable security measures—particularly inexcusable given the company's history of breaches. A company that has already been sued over data security failures has heightened notice of its obligations.
Breach of Implied Contract: When customers share personal information with a business, there's an implicit understanding that the business will protect that information. The lawsuits argue Panera violated this implicit agreement.
Unjust Enrichment: Panera collected and monetized customer data—using it for marketing, loyalty programs, and operational analytics—while failing to invest adequately in protecting it. The company profited from data it couldn't be bothered to secure.
Invasion of Privacy: The unauthorized disclosure of personal information to cybercriminals constitutes an invasion of privacy under various state laws.
The lawsuits seek compensatory damages, injunctive relief requiring improved security measures, and—critically—lifetime identity theft protection services for affected customers. Legal representation includes attorneys from Gray, Ritter & Graham P.C., Lynch Carpenter LLP, McShane & Brady LLC, and Emery Reddy P.C.
Both lawsuits define the potential class as "anyone in the United States whose PII was compromised in the Panera data breach." With 5.1 million unique accounts affected, this is a substantial class—and one that's likely to grow as more details emerge.
For Panera, this represents not just legal liability but strategic distraction. Class action litigation is expensive, time-consuming, and damaging to brand reputation. And this isn't Panera's first rodeo—they're still processing the aftermath of the $2.5 million settlement from the 2024 ransomware attack.
Panera's Breach History: A Pattern of Failure
To understand why the ShinyHunters Panera breach matters, you need to understand the context. This isn't an isolated incident. It's the third act in a security tragedy that has been unfolding since 2018.
2018: The Website Data Leak (Eight Months, 37 Million Records)
In August 2017, security researcher Dylan Houlihan discovered something alarming about panerabread.com: customer records were accessible in plain text through the website's public-facing infrastructure. No authentication required. No encryption in place. The data was simply there, waiting to be scraped.
Houlihan did the responsible thing: he reported the vulnerability directly to Panera. According to his account—later corroborated by legendary security journalist Brian Krebs—Panera's director of information security dismissed the report as "likely a scam."
The vulnerability persisted for eight months.
In April 2018, after growing frustrated with Panera's inaction, Houlihan contacted Krebs, who published a detailed exposé on KrebsOnSecurity. The public disclosure finally forced Panera to act—though their initial "fix" was laughable, merely requiring users to log in before accessing the same plaintext data.
When the dust settled, the scope was staggering: 37 million customer records had been exposed. The data included names, email addresses, physical addresses, birthdays, the last four digits of credit cards, and loyalty card numbers. All of it in plain text. All of it indexable and scrapable with basic automated tools.
Panera initially claimed the exposure affected "thousands" of records. This was either deliberate deception or catastrophic incompetence—take your pick.
2024: The Ransomware Attack (147,321 Employees Compromised)
On March 23, 2024, Panera Bread's IT infrastructure collapsed. Online ordering went dark. Point-of-sale systems at restaurants nationwide stopped functioning. In-store kiosks became expensive paperweights. Internal employee systems became inaccessible.
The culprit was ransomware—though Panera was initially reluctant to confirm the specific nature of the attack. As systems came back online over the following days and weeks, a clearer picture emerged: attackers had stolen employee personal information, including Social Security numbers, from 147,321 current and former Panera workers.
The class action lawsuits came quickly, and by August 2025, Panera had agreed to a $2.5 million settlement. Affected employees were entitled to up to $500 for ordinary out-of-pocket costs, up to $6,500 for extraordinary losses like identity theft, and $25 per hour for time spent addressing breach-related issues.
2026: ShinyHunters (14 Million Records, 5.1 Million Customers)
And now here we are. Third verse, same as the first—only worse.
The ShinyHunters attack represents everything Panera should have learned from the previous two incidents. Voice phishing targeting SSO credentials? That's a documented attack vector with established defenses. Unencrypted customer data? That's the exact same failure that exposed 37 million records in 2018. Inadequate response and communication? That's been Panera's pattern since Dylan Houlihan first tried to warn them nearly a decade ago.
Security researchers have a term for organizations like Panera: repeat offenders. These are companies that get breached, settle the lawsuits, implement minimal reforms, and then get breached again. Threat actors love repeat offenders. They're soft targets with proven security weaknesses and—crucially—demonstrated willingness to pay rather than fix underlying problems.
As Cory Michal, CSO of AppOmni, told Mashable: "The big lesson is Panera's repeated compromises. The fact it's already had to settle class-action claims over alleged failures to protect consumer data show how difficult it is for large, distributed organizations to consistently operationalize SaaS and identity security at scale."
That's a diplomatic way of saying: Panera keeps getting hit because Panera doesn't learn.
ShinyHunters: Profile of a Prolific Threat Actor
Understanding the Panera Bread data breach 2026 requires understanding ShinyHunters—one of the most active and sophisticated cybercriminal groups operating today.
Origins and Evolution
ShinyHunters emerged in 2019 and became publicly active in 2020. The group takes its name from the Pokémon gaming community, where "shiny hunting" refers to the obsessive pursuit of rare variant Pokémon. In cybercriminal terms, ShinyHunters pursues rare and valuable data.
The group initially focused on direct database breaches—exploiting vulnerabilities in web applications and cloud services to extract customer data. Over time, their tactics have evolved toward identity infrastructure attacks, third-party compromises, and increasingly sophisticated social engineering.
ShinyHunters operates on a consistent model: breach, extort, leak. They infiltrate target organizations, exfiltrate valuable data, demand ransom payments, and leak the data publicly when victims refuse to pay. This creates multiple monetization opportunities—ransom payments from victims who comply, and data sales to other criminals when victims don't.

The Track Record
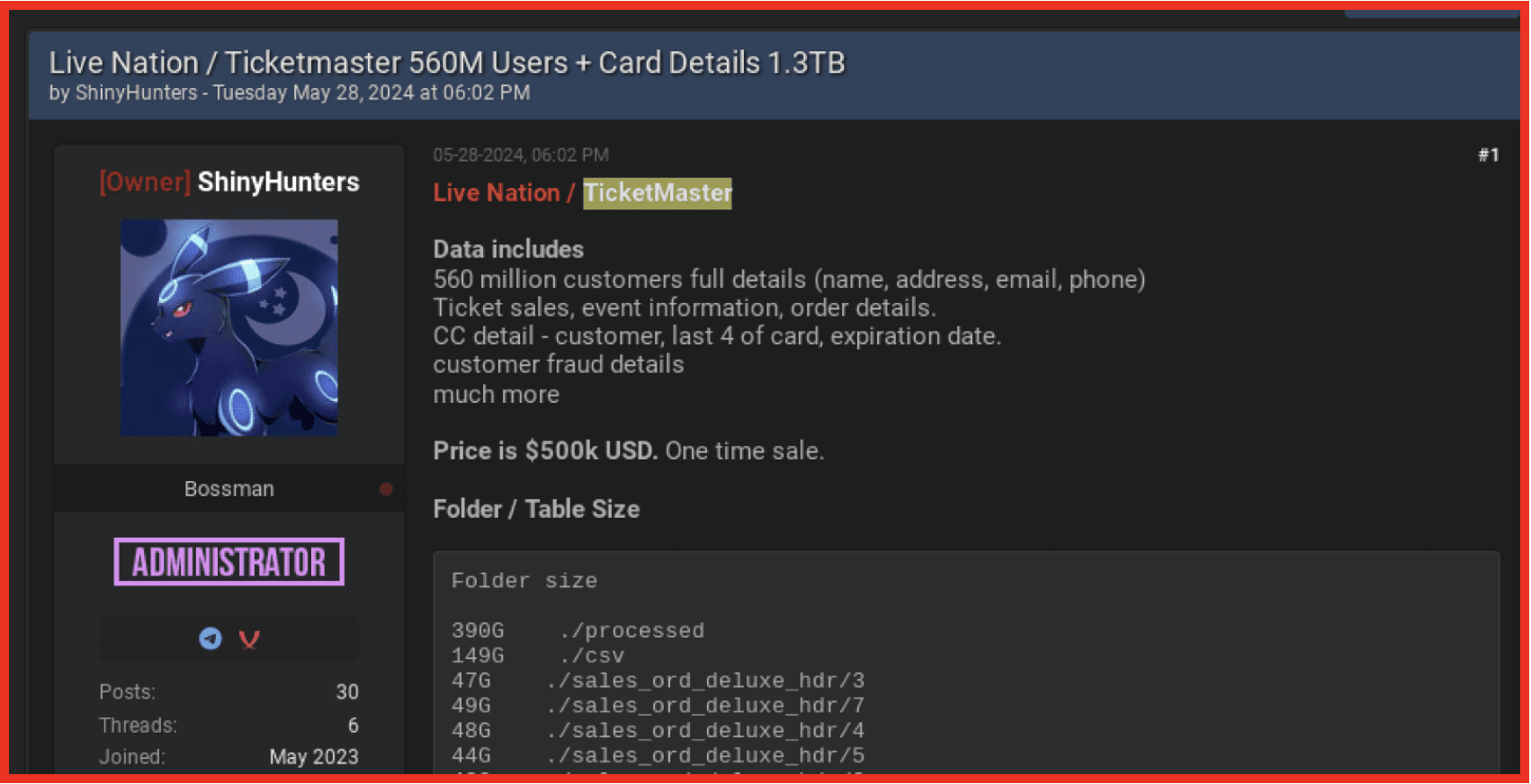
ShinyHunters' breach portfolio reads like a who's who of data security failures:
2020: Tokopedia (91 million accounts), Wishbone (full database), Microsoft (500GB of source code), Wattpad (270 million records)
2021: AT&T Wireless (70 million subscribers—their first AT&T breach), Bonobos (7+ million records), Aditya Birla Fashion (5.4 million emails)
2023: Pizza Hut Australia (1+ million customers)
2024: AT&T Wireless again (110 million customers—AT&T reportedly paid $370,000 in ransom), Ticketmaster via Snowflake (560 million users, 1.3TB of data), Santander (30 million customers across Spain, Chile, and Uruguay), PowerSchool (education data)
2025: LVMH (Louis Vuitton, Dior, Tiffany), Google (corporate Salesforce instance), Qantas (5.7 million customers), Jaguar Land Rover, Kering (Gucci, Balenciaga—43+ million records), Pornhub (94GB/200 million records via Mixpanel), SoundCloud (29.8 million accounts)
2026: Panera Bread (14 million records), Match Group (10 million records), Crunchbase, Betterment, and counting
Several patterns emerge from this history:
SSO and Identity Focus: ShinyHunters has increasingly targeted identity infrastructure rather than individual applications. Compromise SSO credentials once, access everything.
Third-Party Targeting: Many of ShinyHunters' biggest breaches came through third-party platforms—Snowflake, Mixpanel, Salesforce. Attacking the supply chain amplifies impact.
Repeat Victimization: AT&T has been hit twice. Organizations with poor security culture become recurring targets.
Voice Phishing Expertise: The current SSO vishing campaign represents a strategic evolution, using human social engineering to defeat technical controls like multi-factor authentication.
Affiliations
Threat intelligence researchers have documented connections between ShinyHunters and other notorious groups, including Scattered Spider (known for the MGM and Caesars attacks) and Lapsus$ (the group that hit Microsoft, Nvidia, and Samsung before key members were arrested). This network effect means that tactics, techniques, and even compromised credentials flow between groups, amplifying the threat.

Why Panera Keeps Getting Hit: Structural Failures
The Panera Bread data breach 2026 isn't random bad luck. It's the predictable result of structural failures that have persisted across three separate incidents.
Failure 1: Unencrypted Data Storage
The class action lawsuits are explicit: Panera failed to encrypt customer data. This is the same failure that characterized the 2018 breach. After settling a class action over unencrypted data, Panera apparently continued storing customer information in plain text.
Why does this keep happening? Several possibilities:
Technical Debt: Large organizations often accumulate legacy systems that predate modern security standards. Retrofitting encryption is expensive and disruptive.
Cost Prioritization: Encryption at rest adds computational overhead and complexity. Organizations focused on short-term costs may defer these investments.
Siloed Responsibility: In distributed organizations, different teams manage different data stores. Without centralized security governance, encryption standards become inconsistent.
Whatever the reason, the result is the same: when attackers reach Panera's data, they find it ready to use.
Failure 2: Inadequate Social Engineering Defenses
Voice phishing works because humans are trusting. Employees want to be helpful. When someone calls claiming to be from IT, the natural response is to cooperate—especially if the caller seems to know what they're talking about.
Defending against vishing requires a combination of:
- Security awareness training that specifically covers voice-based attacks
- Verification procedures requiring callbacks to known numbers
- Technical controls that limit what can be accomplished via social engineering
- Culture that empowers employees to verify requests without fear of seeming unhelpful
It's unclear what, if any, of these defenses Panera had in place. What is clear is that they weren't enough.
Failure 3: Security as Afterthought
The most damning pattern across Panera's three breaches is the consistent characterization of security as something to address after problems emerge, rather than something to build into operations from the start.
In 2018, Panera dismissed a researcher's report as a "scam" and left a vulnerability unpatched for eight months. In 2024, the ransomware attack suggested inadequate endpoint protection and backup procedures. In 2026, unencrypted data and successful vishing attacks suggest that previous lessons simply weren't learned.
Security isn't a product you buy or a project you complete. It's a culture you build. Organizations that treat security as a checkbox—rather than an ongoing commitment—become the soft targets that threat actors love.

Failure 4: Repeat Offender Status
There's a self-reinforcing aspect to Panera's security failures. Each breach increases the company's attractiveness to threat actors. ShinyHunters didn't target Panera randomly—they targeted an organization with a documented history of security failures, known data assets, and demonstrated willingness to settle lawsuits rather than invest in prevention.
Once you're on the list of soft targets, getting off the list requires more than minimal compliance. It requires demonstrated, sustained, publicly verifiable security improvement. Panera has not provided this.
What Affected Customers Should Do
If you've ever created an account with Panera Bread, used their loyalty program, or placed an online order, you should assume your information may have been compromised. Here's what to do:
Immediate Actions
1. Monitor for Phishing Attempts
With email addresses, phone numbers, and physical addresses exposed, expect targeted phishing attempts. Be suspicious of:
- Emails claiming to be from Panera about "verifying" your account
- Text messages about loyalty points or special offers
- Phone calls asking for personal information
Attackers now have enough context about you to make their approaches convincing. Verify any communication by contacting Panera directly through official channels.
2. Check Have I Been Pwned
Visit haveibeenpwned.com and enter your email address. The site will tell you if your email appears in the Panera breach (and any others). Sign up for breach notifications to be alerted about future exposures.
3. Enable Multi-Factor Authentication Everywhere
While the Panera breach didn't expose passwords, attackers may attempt credential stuffing—using your email address to try passwords from other breaches. Enable MFA on all important accounts, especially:
- Banking and financial services
- Social media
- Any account using the same email address as your Panera account
4. Consider a Credit Freeze
With names, addresses, and birth dates exposed, identity thieves have the building blocks for synthetic identity fraud. A credit freeze prevents new accounts from being opened in your name. It's free to place and lift freezes with all three credit bureaus:
Longer-Term Vigilance
Monitor Financial Statements: Review bank and credit card statements monthly for unauthorized transactions. Set up transaction alerts if your financial institutions offer them.
Watch for IRS Issues: Stolen PII can be used for tax fraud. File your taxes early to prevent someone else from filing in your name.
Beware of Confusion Scams: Panera is currently processing the settlement from the 2024 ransomware attack. Scammers may exploit confusion between the two incidents to conduct phishing attacks. Verify any settlement communications through official court documents.
Join the Class Action: If you received notification that your data was compromised, you may be eligible to join the class action lawsuits. Keep any communications from Panera as documentation.
Panera's Response: Too Little, Too Late
Panera's official response to the breach has been characteristically muted. Their public statement acknowledges the incident in the vaguest possible terms:
"Panera identified and took steps to address an incident involving access to data in a SaaS application. We determined how this occurred and strengthened controls for that application. The data involved is contact information, and we notified law enforcement."
This statement is notable for what it doesn't include:
- No acknowledgment of ShinyHunters or the scale of the attack
- No specific details about what "strengthened controls" means
- No timeline for customer notification
- No offer of identity protection services
- No explanation of why data was stored unencrypted
As of this writing—nearly two weeks after the breach became public—Panera has not filed formal data breach notices with state attorneys general. Depending on applicable state laws, this may represent a compliance failure in addition to the underlying security failure.
The contrast with best-practice breach response is stark. Responsible organizations:
- Acknowledge breaches promptly and specifically
- Provide clear information about what data was compromised
- Offer identity protection services proactively
- Explain what steps they're taking to prevent recurrence
- Communicate transparently with affected individuals
Panera has done none of these things.
Conclusion: Pattern Recognition
Three breaches in eight years. 37 million records in 2018. 147,000 employees in 2024. 14 million records in 2026. Unencrypted data. Dismissed warnings. Delayed responses. Legal settlements followed by new lawsuits.
At what point does pattern recognition kick in?
The Panera Bread data breach 2026 isn't a story about sophisticated hackers defeating cutting-edge defenses. ShinyHunters' vishing campaign is well-documented, with warnings from Okta and other security organizations predating the Panera attack. The attack vector—social engineering targeting SSO credentials—has known mitigations. And the unencrypted data storage that made the breach catastrophic is a failure so basic that it beggars belief.
This is a story about organizational culture. About a company that treats security as a cost center rather than a core competency. About executives who settle lawsuits without addressing underlying problems. About customers who trust businesses with personal information and discover, years later, that their trust was misplaced.
For the 5.1 million Panera customers whose information is now circulating on the dark web, the damage is done. They'll spend years monitoring credit reports, fielding phishing attempts, and wondering which of those attempts will succeed. That's the human cost of Panera's pattern of failure.
For Panera Bread, the question is whether they'll finally treat this as the crisis it is—or whether they'll settle the lawsuits, issue reassuring press releases, and wait for ShinyHunters or their successors to come calling again.
History suggests we know the answer.
Key Takeaways
- Panera Bread suffered its third major data breach in eight years when ShinyHunters stole 14 million records in January 2026
- The attack used voice phishing to compromise Microsoft Entra SSO credentials, part of a broader campaign affecting 100+ organizations
- Stolen data was not encrypted, according to class action lawsuits filed against the company
- Three class action lawsuits have been filed, seeking damages and lifetime identity protection for affected customers
- Panera's response has been minimal, with no formal breach notifications filed and no identity protection services offered
- Affected customers should monitor for phishing, check Have I Been Pwned, enable MFA, and consider credit freezes
Have you been affected by the Panera Bread data breach? The class action lawsuits are currently seeking plaintiffs. Contact the representing law firms for information about joining the case.