UNC3886 Hits All 4 Singapore Telcos: Inside the Largest Multi-Agency Cyber Defense Operation

When a nation-state adversary targets every single telecommunications provider in a country simultaneously, it's not reconnaissance—it's preparation for something bigger.
On February 9, 2026, Singapore's Minister for Digital Development and Information Josephine Teo revealed details of what security officials are calling one of the most sophisticated cyber espionage campaigns ever mounted against a nation's telecommunications infrastructure. China-linked Advanced Persistent Threat (APT) group UNC3886 successfully penetrated all four of Singapore's major telecommunications operators—Singtel, StarHub, M1, and Simba Telecom—in a deliberate, targeted, and meticulously planned campaign that required the largest multi-agency cyber defense operation in the nation's history to contain.
The attack, first publicly disclosed in July 2025 by Coordinating Minister for National Security K Shanmugam, triggered Operation CYBER GUARDIAN: an unprecedented eleven-month defensive operation involving over 100 cyber defenders from six government agencies. The campaign's scope, sophistication, and strategic targeting send a clear message to critical infrastructure operators worldwide: telecommunications networks have become the crown jewels of nation-state cyber espionage, and adversaries are investing heavily in capabilities designed to compromise them.
The Attack: Zero-Days and Advanced Tradecraft
Initial Access Through Zero-Day Exploitation
UNC3886 demonstrated the hallmarks of a well-resourced, patient adversary with deep technical capabilities. According to Singapore's Cyber Security Agency (CSA) and the Infocomm Media Development Authority (IMDA), the threat actor deployed advanced tools and zero-day exploits to bypass perimeter defenses.
In one documented instance, UNC3886 exploited a zero-day vulnerability in a perimeter firewall to gain initial access into Singapore's telecommunications networks. The CSA described this as "finding a new key no one else had found to unlock the doors"—a vulnerability for which no security patch existed at the time of exploitation.
Once inside, the threat actor demonstrated sophisticated persistence mechanisms. They deployed rootkit malware designed to maintain persistent access while covering their tracks and evading detection. These rootkits made comprehensive security checks extraordinarily challenging, requiring cyber defenders to conduct painstaking forensic analysis across entire network architectures.
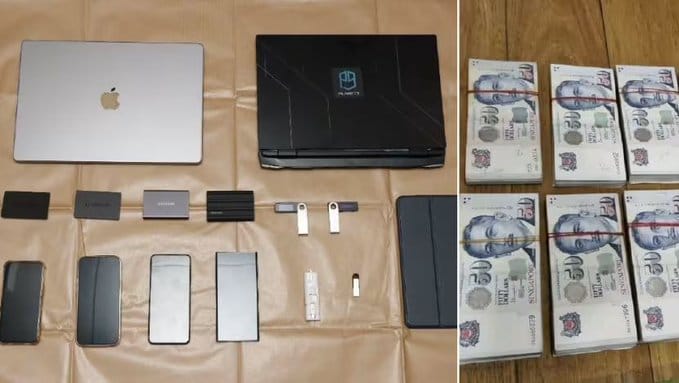
The threat actor successfully exfiltrated a small amount of technical data, believed to be primarily network-related information intended to advance their operational objectives. In one alarming instance, UNC3886 gained limited access to critical systems—though investigators emphasize they did not penetrate far enough to disrupt services.
What Was Protected
Despite the sophisticated intrusion, Singapore's defense-in-depth architecture held at critical junctures. The most sensitive and critical systems, including 5G core networks, were physically and logically segregated from compromised segments. This architectural decision—isolating crown jewel systems in separate, hardened environments—proved decisive in preventing catastrophic damage.
Crucially, there is no evidence to date that sensitive or personal customer data such as customer records were accessed or exfiltrated. Telecommunications services including internet availability remained uninterrupted throughout the incident. Unlike the devastating breaches that have struck telecommunications operators in other nations, Singapore's layered defenses prevented the worst-case scenarios.
Who Is UNC3886? The Ghost in the Machine
Attribution and Historical Activity
UNC3886 was first identified in 2022 by Google-owned Mandiant as a China-nexus cyber espionage group. The "UNC" designation stands for "uncategorized"—Mandiant's nomenclature for threat actors that haven't been definitively linked to a specific umbrella group but demonstrate consistent tactics, techniques, and procedures (TTPs) across multiple intrusions.
Don't let the "uncategorized" label fool you. UNC3886 is among the most sophisticated cyber espionage groups observed by Western intelligence agencies. They are known to target critical sectors including government, telecommunications, technology, aerospace, defense, energy, and utilities across the United States, Europe, and Asia.
Technical Capabilities That Set Them Apart
What makes UNC3886 particularly dangerous is their demonstrated ability to compromise the hardest targets in the cybersecurity ecosystem: network edge devices and virtualization infrastructure that typically lack endpoint detection and response (EDR) agents or robust security monitoring.
Mandiant's research reveals UNC3886's alarming technical depth:
Zero-Day Exploitation Portfolio: The group has exploited multiple zero-day vulnerabilities across leading enterprise technologies:
- CVE-2022-41328 (FortiOS): Exploited to download and execute backdoors on Fortinet FortiGate devices
- CVE-2022-22948 (VMware vCenter): Exploited to obtain encrypted credentials from vCenter's PostgreSQL database
- CVE-2023-20867 (VMware Tools): Exploited to execute unauthenticated Guest Operations from ESXi hosts to guest virtual machines
- CVE-2023-34048 (VMware vCenter): Exploited since late 2021 for unauthenticated remote command execution
- CVE-2025-21590 (Juniper Networks Junos OS): Process injection to circumvent Veriexec protections
Advanced Persistent Rootkits: UNC3886 deploys customized versions of publicly available rootkits including REPTILE and MEDUSA, modified to evade detection and establish multiple layers of persistence. Their operational security is meticulous—they replace default configuration strings, modify file paths, and implement custom encryption to frustrate signature-based detection.
Custom Malware Ecosystem: The group maintains a suite of purpose-built malware:
- MOPSLED: A shellcode-based modular backdoor with HTTP and custom binary protocol support
- RIFLESPINE: A cross-platform backdoor leveraging Google Drive for command and control, using legitimate cloud services to blend malicious traffic with normal business operations
- VIRTUALSHINE, VIRTUALPIE, VIRTUALSPHERE: A family of backdoors exploiting VMware's Virtual Machine Communication Interface (VMCI) for covert host-to-guest and guest-to-guest communications
- TINYSHELL variants: Heavily customized backdoors deployed on Juniper routers with active and passive backdoor functions
Living Off the Land: UNC3886 demonstrates deep understanding of compromised infrastructure, using legitimate administrative tools and trusted third-party services (GitHub, Google Drive) for command and control to avoid raising suspicions.
Emphasis on Credential Theft
A defining characteristic of UNC3886 operations is their obsessive focus on collecting and utilizing valid credentials for lateral movement. They deploy backdoored SSH clients and daemons to intercept credentials, compromise Terminal Access Controller Access-Control System Plus (TACACS+) authentication servers, and harvest service account credentials from virtualization management platforms.
This approach allows them to move through enterprise networks as authenticated users, bypassing many security controls that flag suspicious executables or network connections but trust legitimate credentials.

Operation CYBER GUARDIAN: Singapore's Response
Unprecedented Multi-Agency Coordination
When Singapore's telecommunications operators detected suspicious activity and notified IMDA and CSA in March 2025, authorities launched what would become Operation CYBER GUARDIAN—Singapore's largest coordinated cyber incident response effort to date, spanning more than eleven months.
The operation brought together over 100 cyber defenders from six government agencies:
- Cyber Security Agency of Singapore (CSA): Overall coordination and threat intelligence
- Infocomm Media Development Authority (IMDA): Telecommunications sector oversight
- Centre for Strategic Infocomm Technologies (CSIT): Advanced technical analysis and capabilities
- Digital and Intelligence Service (DIS): Singapore Armed Forces' cyber intelligence arm
- Government Technology Agency (GovTech): Government systems security
- Internal Security Department (ISD): Counter-intelligence and threat assessment
This whole-of-government response reflects Singapore's national doctrine of cyber defense, which emphasizes that government agencies and the private sector must come together to collectively defend cyberspace. The doctrine guides capability development across the cyber ecosystem, defines roles different parties play in cyber defense, and prescribes coordinated actions during incidents.
Defensive Actions and Containment
Under Operation CYBER GUARDIAN, authorities worked closely with telecommunications operators to:
Restrict Lateral Movement: Implementing network segmentation and access controls to limit UNC3886's ability to expand their foothold across telecommunications infrastructure.
Close Access Points: Identifying and remediating the zero-day vulnerabilities and misconfigurations the threat actor used for initial access and persistence.
Ensure Systems Remain Safe: Conducting comprehensive security validation across compromised networks to verify no additional backdoors or persistence mechanisms remained.
Expand Monitoring Capabilities: Deploying enhanced detection systems and threat hunting operations to identify renewed intrusion attempts.
Joint Threat Hunting: Conducting proactive searches for indicators of compromise across all four telecommunications operators simultaneously.
Penetration Testing: Validating that remediation measures were effective through adversarial simulation exercises.
The Human Cost
Minister Teo acknowledged the extraordinary effort required from Singapore's cyber defenders, referring to "lost weekends and mental exhaustion" during the operation. This human element often goes unrecognized in cyber defense: the sustained pressure of defending against a patient, sophisticated adversary while maintaining normal business operations.
The defenders' vigilance prevented catastrophic outcomes. As Minister Teo emphasized, "So far, the attack by UNC3886 has not resulted in the same extent of damage as cyberattacks elsewhere. This is not a reason to celebrate. Rather, it is to remind ourselves that the work of cyberdefenders matters."
Why Telecommunications? The Strategic Value of Telco Access
The Foundation of Digital Society
Telecommunications networks occupy a unique position in modern society—they are simultaneously critical infrastructure and a surveillance goldmine. They power the digital economy, transmit vast amounts of sensitive information, and provide the connectivity essential for banking, healthcare, transportation, and government services.
If threat actors succeed in compromising telecommunications infrastructure, the potential consequences cascade across every sector of society. As Minister Teo warned, a successful attack could have had knock-on effects on banking, transport, and healthcare services—"everything that requires a phone or internet connection would then be affected."
Global Pattern of Telecommunications Targeting
Singapore's experience is not isolated. Telecommunications operators worldwide have become priority targets for nation-state adversaries:
Salt Typhoon (United States, 2024-2025): A massive Chinese espionage campaign infiltrated multiple major U.S. telecommunications providers, potentially accessing sensitive military and law enforcement information. U.S. investigators determined the campaign targeted some 80 nations globally, marking one of the most extensive telecommunications compromises ever documented. Security experts have described Salt Typhoon as "one of the most damaging series of cyberattacks ever undertaken against the United States."

The attack enabled Chinese operatives to track millions of Americans' locations in real time, record phone calls at will, and read text messages. U.S. Senate testimony revealed the breach occurred "in large part because telecommunications companies failed to implement rudimentary—rudimentary!—security measures."
SK Telecom (South Korea, April 2025): A cyberattack exposed SIM data of nearly 27 million users, demonstrating the catastrophic scale of customer data exposure possible in telecommunications breaches.
Australia (November 2025): Australian security officials warned that Chinese government-linked groups including Salt Typhoon and Volt Typhoon had attempted to access Australia's critical infrastructure, including telecommunications networks, for espionage and potential sabotage purposes.
The Intelligence Value
Telecommunications access provides nation-state adversaries with capabilities that traditional espionage methods cannot match:
Metadata Analysis: Even without decrypting communications, access to call detail records, messaging metadata, and location data reveals social networks, travel patterns, and behavioral analysis of high-value targets.
Targeted Surveillance: The ability to intercept specific communications of government officials, military personnel, corporate executives, journalists, and dissidents.
Supply Chain Visibility: Understanding which organizations communicate with whom, revealing business relationships, government contractor networks, and supply chain dependencies.
Prepositioned Access: Establishing persistent access to telecommunications infrastructure provides a launchpad for future operations, whether intelligence collection or disruptive cyberattacks.
Lawful Intercept Abuse: Many telecommunications systems include lawful intercept capabilities for law enforcement. Adversaries who compromise these systems gain access to surveillance capabilities built into the infrastructure.
China's Telecommunications Espionage Strategy
A Pattern, Not an Anomaly
UNC3886's Singapore operations fit within a broader pattern of Chinese cyber espionage focused on telecommunications infrastructure. The People's Republic of China (PRC) has consistently prioritized telecommunications access as part of its strategic intelligence collection.
In January 2025, the U.S. Treasury Department sanctioned Sichuan Juxinhe Network Technology Co., a Sichuan-based cybersecurity company, accusing it of "direct involvement in the Salt Typhoon cyber group" and ties to China's Ministry of State Security. This rare public attribution directly links Chinese government intelligence agencies to telecommunications compromises.
Beyond Espionage: Prepositioned Access for Disruption
While current operations appear focused on intelligence collection, prepositioned access to telecommunications infrastructure could serve more disruptive purposes in future conflicts. The same access that enables surveillance could be leveraged to:
- Disrupt communications during a crisis or conflict
- Manipulate routing to intercept or redirect traffic
- Degrade service quality to undermine confidence in digital infrastructure
- Conduct information operations by selectively blocking or modifying communications
As Minister Teo noted, "They could deploy more tools to disrupt telecoms and internet services," highlighting that espionage access can be weaponized for disruption when strategic circumstances change.
The Economic Security Dimension
Singapore's position as an international financial and logistics center makes telecommunications security a matter of economic security. "Businesses may shy away from Singapore if they are unsure about our systems—whether the systems are clean, resilient and safe," Minister Teo warned.
This economic dimension extends beyond Singapore. Nations and corporations make location decisions based partially on confidence in digital infrastructure security. Successful telecommunications compromises undermine that confidence and can drive businesses to relocate critical operations.
Lessons for Other Nations
1. Defense in Depth Is Not Optional
Singapore's architectural decision to physically and logically segregate the most critical systems—including 5G core networks—from less critical infrastructure prevented catastrophic damage. Even when UNC3886 gained limited access to critical systems, the segregation prevented them from achieving their ultimate objectives.
Lesson: Critical infrastructure operators must implement defense in depth with crown jewel systems isolated in hardened environments, not merely firewalled but architecturally separated with different authentication mechanisms, monitoring systems, and access controls.
2. Early Detection and Reporting Saves Lives
Singapore's telecommunications operators reported anomalies to CSA even though "suspicious activities detected by the telcos in March 2025 did not reach the threshold required for sounding the alarm." This early communication allowed authorities to launch Operation CYBER GUARDIAN before the threat actor achieved their objectives.
Lesson: Critical infrastructure sectors need clear channels for reporting suspicious activity to government cybersecurity agencies before incidents meet formal breach notification thresholds. "See something, say something" culture can mean the difference between containment and catastrophe.
3. Whole-of-Government Response Requires Pre-Built Coordination
Singapore's success in mounting a coordinated response involving six government agencies and four private telecommunications operators didn't happen by accident. It resulted from years of investment in:
- Clear doctrine defining roles and responsibilities
- Pre-existing relationships between agencies and private sector
- Regular exercises and capability development
- Established communication channels and escalation procedures
Lesson: Nations cannot improvise multi-agency coordination during a crisis. The relationships, procedures, and capabilities must be developed and exercised before a sophisticated adversary forces you to use them.
4. Zero-Day Vulnerabilities Are the New Normal
UNC3886's use of multiple zero-day vulnerabilities across different vendor platforms highlights that critical infrastructure operators face adversaries who invest in capabilities that bypass all known defenses.
Lesson: Security strategies cannot rely solely on patching known vulnerabilities. Organizations must implement:
- Behavioral detection that identifies anomalous activity even when using unknown exploits
- Network segmentation that limits what an adversary can access even after initial compromise
- Monitoring of network edge devices and virtualization infrastructure where EDR agents cannot be deployed
- Threat hunting programs that proactively search for indicators of compromise
5. The Fight Continues After "Remediation"
Minister Teo emphasized that "despite best efforts, there is no guarantee against future, continuing attempts to gain access to Singapore's critical infrastructure." APTs are backed by countries with formidable resources in manpower and technology, and they will not give up easily.
Singapore authorities expanded monitoring capabilities and deployed active threat hunting to detect renewed UNC3886 access attempts. Telecommunications operators implemented ongoing interventions including joint threat hunting, penetration testing, and continuous capability development.
Lesson: Incident response is not a one-time event with a clear end date. When facing nation-state adversaries, defenders must assume the threat actor will attempt to regain access and maintain heightened vigilance indefinitely.
6. Private Sector Accountability Is Essential
Minister Teo delivered a pointed message to critical infrastructure operators: "You are at the front lines of the battle against cyberthreat actors. Your actions, or inaction, can determine whether we succeed or fail in protecting our critical infrastructure, and our national security."
She urged operators to continue investing in upgrading systems and capabilities, emphasizing that security is not solely a government responsibility.
Lesson: Governments worldwide must establish clear cybersecurity requirements for critical infrastructure with accountability mechanisms. The Salt Typhoon compromise of U.S. telecommunications providers occurred in part due to failure to implement "rudimentary security measures"—an unacceptable outcome when national security hangs in the balance.
The Broader Threat Landscape
Telecommunications as Tier-One Targets
The targeting of telecommunications infrastructure by multiple Chinese APT groups (UNC3886, Salt Typhoon, Volt Typhoon) represents a coordinated strategic prioritization by PRC intelligence services. These are not opportunistic compromises but deliberate campaigns with significant resources allocated to developing capabilities for telecommunications access.
As Dmitri Alperovitch, chairman of Silverado Policy Accelerator, testified to Congress about Salt Typhoon: it was "one of the most consequential campaigns against the U.S. ever" with "profound impacts on national security."
The Virtualization Blind Spot
UNC3886's emphasis on compromising virtualization platforms (VMware vCenter, ESXi) and network edge devices (Fortinet FortiGate, Juniper routers) exploits a significant gap in most security architectures. These systems:
- Lack traditional endpoint protection (EDR, antivirus)
- Are trusted by nature—they manage other systems
- Provide access to credentials for managed systems
- Often run embedded operating systems with limited logging
- Rarely receive the security attention focused on servers and workstations
This blind spot is not accidental—UNC3886 clearly studied enterprise security architectures and deliberately targeted the gaps.
The End-of-Life Problem
Mandiant's investigation of UNC3886's Juniper router compromises revealed the affected devices were running end-of-life hardware and software. Legacy systems that no longer receive security updates become attractive targets for nation-state adversaries who can develop exploits without concern about vendor patches.
Critical infrastructure operators face difficult decisions about upgrading or replacing expensive network equipment, but the cost of operating end-of-life systems in a threat environment populated by groups like UNC3886 far exceeds the capital expenditure of modernization.
What Comes Next
Singapore's Path Forward
CSA announced it will progressively introduce initiatives to raise the capability level across Singapore's cyber ecosystem, enabling better and more timely responses against cyber threats. The telecommunications operators are putting in place ongoing interventions including:
- Joint threat hunting between operators and government agencies
- Regular penetration testing to validate defensive measures
- Continuous capability development and training
- Information sharing on threats and indicators of compromise
Minister Teo emphasized that successful cyberattacks can affect trust and confidence in Singapore as an international financial and logistics center, making cybersecurity a matter of economic competitiveness as well as national security.
Global Implications
Every nation with critical telecommunications infrastructure should view Singapore's experience as a preview of threats they will face—or may already be facing without detection. The sophistication of UNC3886's campaign, the resources required to detect and contain it, and the ongoing nature of the threat provide a sobering assessment of the cyber threat landscape.
The telecommunications sector globally must recognize it operates in a target-rich environment for the world's most capable adversaries. Half-measures and checkbox compliance are insufficient when facing threat actors with the patience, sophistication, and resources of UNC3886.
Conclusion: A Warning and a Roadmap
Singapore's disclosure of the UNC3886 campaign provides both a warning and a roadmap. The warning: telecommunications infrastructure is under systematic attack by sophisticated nation-state adversaries with deep technical capabilities and unlimited patience. The roadmap: coordinated whole-of-government and private sector response, defense in depth architecture, early detection and reporting, and sustained vigilance can contain even the most advanced threats.
But there's no sugar-coating the reality Minister Teo articulated: "In short, the fight continues, and we must all do our part."
UNC3886 will attempt to regain access to Singapore's telecommunications infrastructure. Other nation-state groups are simultaneously targeting telecommunications operators worldwide. The techniques that succeeded in Singapore will be adapted and deployed against other nations. Zero-day vulnerabilities will be developed and stockpiled. Rootkits will be customized. Legitimate tools will be weaponized.
The question is not whether telecommunications operators will be targeted—that is certain. The question is whether defenders will detect the intrusion in time, respond with coordination and capability, and prevent catastrophic outcomes.
Singapore demonstrated that with investment, coordination, and determination, even a small nation can defend against a superpower's cyber espionage apparatus. But as Operation CYBER GUARDIAN makes clear, the cost is measured in hundreds of defenders working thousands of hours over nearly a year to contain a single campaign.
That is the reality of cyber defense in the age of nation-state threats. And UNC3886 is far from the only ghost in the machine.
About UNC3886: First identified by Mandiant in 2022, UNC3886 is a China-nexus advanced persistent threat group known for targeting network edge devices, virtualization infrastructure, and critical information infrastructure with zero-day exploits. The group has demonstrated operations across North America, Europe, Asia, and Oceania targeting government, telecommunications, technology, aerospace, defense, and energy sectors.
About Operation CYBER GUARDIAN: Singapore's largest coordinated cyber incident response operation, involving over 100 defenders from CSA, IMDA, CSIT, DIS, GovTech, and ISD working over eleven months to contain UNC3886's access to all four major telecommunications operators.
This analysis is based on official disclosures from Singapore's Cyber Security Agency and Infocomm Media Development Authority, Mandiant threat intelligence reports, and public reporting from The Straits Times, Channel News Asia, The Hacker News, and other sources.