Your Breach Funded Tomorrow's Attack: Inside the Self-Reinforcing Supply Chain Cybercrime Economy
Every ransom paid, every credential stolen, every database breached—they don't disappear into the void. They fuel a $10.5 trillion shadow economy that's growing faster than legitimate tech. And supply chain attacks are the engine driving it all.
The Uncomfortable Truth Security Leaders Won't Say Out Loud
Here's something no CISO wants to admit at board meetings: your organization's breach didn't just hurt you. It funded the next attack on someone else.
When Acme Corp pays a $2.3 million ransom to decrypt their servers, that money doesn't evaporate. Within 72 hours, portions flow to:
- Initial Access Brokers who will breach three more networks this month
- Malware developers refining the next zero-day exploit
- Bulletproof hosting providers spinning up command-and-control infrastructure
- Money launderers reinvesting in cryptocurrency mixers
- Recruiters hiring developers away from legitimate security firms
The cybercrime economy isn't just big—it's self-reinforcing. Each successful attack generates capital that makes future attacks easier, cheaper, and more likely to succeed.
And at the heart of this vicious cycle sits a particularly dangerous category: supply chain attacks.
Why Supply Chain Attacks Are the Ultimate Force Multiplier
Traditional attacks are retail operations. One breach, one victim, one payout.
Supply chain attacks are wholesale. Compromise one vendor, one library, one update mechanism—and suddenly you have access to thousands of victims simultaneously.
Consider the economics:
| Attack Type | Typical Cost to Execute | Potential Victims | ROI Multiplier |
|---|---|---|---|
| Targeted phishing | $500-2,000 | 1-5 | 1x |
| Ransomware-as-a-Service | $1,000-3,000 | 1-20 | 10x |
| Supply chain compromise | $50,000-500,000 | 1,000-100,000 | 100-1,000x |
When APT29 (Russia's SVR) invested resources into compromising SolarWinds' build environment, they gained access to approximately 18,000 organizations with a single operation. That includes the U.S. Treasury, Commerce, and Homeland Security departments.
The investment was significant. The return was incalculable.
This is why supply chain attacks have surged 431% between 2021 and 2023, according to the 2025 Cowbell Cyber Insurance Report. They're simply the most efficient investment a criminal or nation-state operator can make.
The Money Flow: Tracing Where Your Breach Proceeds Go
Understanding the cybercrime economy requires following the money. Here's how proceeds from a typical enterprise breach circulate through the ecosystem:
Stage 1: The Initial Breach (Week 1)
An Initial Access Broker (IAB) compromises your network. Maybe they exploited an unpatched VPN. Maybe they bought credentials from a previous breach. Maybe someone clicked a link.
The IAB spent approximately $800 on infrastructure and $200 on credentials from a previous breach.
Total investment: $1,000
Stage 2: Access Sale (Week 2-3)
The IAB lists your corporate network on a dark web marketplace:
- RDP access: $500
- VPN credentials with MFA bypass: $1,500
- Domain admin access: $3,500
A ransomware affiliate purchases the Domain Admin listing for $3,500.
The IAB's profit: $2,500 (250% ROI)
Stage 3: Ransomware Deployment (Week 4-5)
The affiliate deploys ransomware using a RaaS (Ransomware-as-a-Service) subscription. The RaaS operator provided:
- Customized ransomware payload
- Negotiation portal
- Cryptocurrency payment infrastructure
- "Customer support" for victims
The affiliate's cost: $3,500 (access) + $500 (tools/infrastructure) = $4,000
Stage 4: The Ransom (Week 6-8)
You negotiate. You pay $1.2 million in Bitcoin to recover your data and prevent publication of stolen files.
Distribution of your $1.2 million:
| Recipient | Amount | Percentage |
|---|---|---|
| Ransomware affiliate | $960,000 | 80% |
| RaaS operator | $240,000 | 20% |
Stage 5: Profit Reinvestment (Week 9+)
Here's where the cycle perpetuates. The affiliate—now flush with cash—reinvests:
- $100,000 → More network access purchases from IABs
- $50,000 → Premium zero-day exploits from grey market brokers
- $30,000 → Developer salary for custom tooling
- $20,000 → Infrastructure (bulletproof hosting, VPNs, domains)
- $760,000 → Personal profit / laundering
The RaaS operator reinvests their $240,000 into:
- $80,000 → Developer salaries for ransomware improvements
- $40,000 → Infrastructure expansion
- $30,000 → Recruiting new affiliates
- $90,000 → Personal profit / organizational reserves
The Cycle Continues
Within 90 days of your payment:
- 3-5 new organizations are compromised using access purchased with your money
- The ransomware strain that hit you has been updated with better evasion capabilities
- New affiliates have been recruited and trained
- The ecosystem is stronger than before your breach
Your breach didn't just hurt you. It made the entire cybercrime ecosystem more capable.
The 2026 Supply Chain Attack Landscape
By the Numbers
| Metric | 2024 | 2025 | 2026 (Projected) |
|---|---|---|---|
| Supply chain attacks (global) | 2,400 | 3,100 | 4,200 |
| Third-party involvement in breaches | 15% | 30% | 40%+ |
| Malicious open source packages | 512,847 | 650,000 | 845,000+ |
| Average dwell time (supply chain) | 287 days | 243 days | ~200 days |
| Average recovery cost | $3.8M | $4.2M | $4.8M |
Sources: Verizon DBIR 2025, Sonatype State of the Software Supply Chain, IBM Cost of a Data Breach Report
Recent High-Profile Supply Chain Incidents
February 2026: Healthcare Claims Processor Cascade A regional healthcare claims processing vendor was compromised via a trojanized software update. Because the vendor processed claims for 847 healthcare providers, the breach exposed PHI for an estimated 12 million patients across 23 states. The initial intrusion cost attackers approximately $45,000 in exploit development. The collective impact to the healthcare ecosystem: $340 million in regulatory fines, remediation, and lawsuits.
January 2026: Financial Services API Provider Attackers compromised a popular API authentication library used by fintech applications. The malicious code harvested API keys and authentication tokens from 2,100 financial applications for 47 days before detection. Estimated direct losses: $890 million in fraudulent transactions.
December 2025: Open Source Observability Tool A maintainer account for a popular monitoring tool was compromised via SIM-swap attack. The attacker injected cryptomining code into a routine update. Because the tool was deployed in production environments, mining operations ran on victim infrastructure for 23 days, consuming an estimated $14 million in cloud computing resources across 4,000 organizations.
The Attack Surface You Can't See
Your Software Supply Chain: A Probability Problem
The average enterprise application contains 530 open source dependencies. Each dependency is a potential attack surface.
Here's the math that keeps security leaders awake:
- If each dependency has a 0.1% chance of being compromised in any given year
- And you have 530 dependencies per critical application
- And you have 50 critical applications
- That's 26,500 dependency-years of exposure annually
- Resulting in a ~23% probability of at least one compromised dependency per year
This isn't fear-mongering. It's statistics.
And the actual compromise rate for popular packages may be higher than 0.1%. In 2024 alone, researchers identified 512,847 malicious packages in public registries.
The Transitive Trust Problem
The 3CX supply chain attack of 2023 demonstrated something terrifying: supply chain attacks can cascade.
The attack chain:
- Trading Technologies' X_TRADER software was trojanized
- A 3CX employee downloaded the compromised software
- Attackers stole credentials via the backdoor
- They used those credentials to access 3CX's build systems
- 600,000+ organizations received malicious 3CX updates
Your vendor's vendors are your attack surface. And your vendor's vendor's vendors. The trust chain extends further than any security team can map.
Nation-State Patience
The XZ Utils backdoor, discovered in March 2024, revealed the ultimate supply chain attack capability: social engineering of open source trust.
An attacker operating as "Jia Tan" spent over two years:
- Making legitimate contributions to the xz-utils compression library
- Building reputation within the open source community
- Eventually becoming a trusted maintainer
- Injecting a sophisticated backdoor using Ed448 cryptography
The backdoor was discovered by pure chance—a Microsoft engineer noticed SSH connections were slightly slower than expected.
Had it reached stable Linux distributions, it would have provided backdoor access to the majority of Linux servers worldwide.
Investment required: Two years of patient work by a skilled operator. Potential access gained: Millions of servers globally.
This is the ROI calculation nation-states are making. And the private criminal ecosystem is learning from them.
The Economic Incentives Are Working Against Us
Defender Economics vs. Attacker Economics
The fundamental problem: attackers have better economics.
Defender Costs (Annual, Large Enterprise):
- Security tools and platforms: $2-8 million
- Security team salaries: $3-12 million
- Compliance and audit: $1-3 million
- Training and awareness: $200-500K
- Incident response retainers: $200-800K
- Total: $6-24 million
Attacker Costs (Per Successful Campaign):
- Initial access (via IAB): $1,000-5,000
- Tooling and infrastructure: $500-3,000
- RaaS subscription: 20% of proceeds
- Total: $1,500-8,000 + profit share
The economics get worse when you consider:
- Defenders must protect everything. Attackers only need one way in.
- Defenders must be right 100% of the time. Attackers only need to succeed once.
- Defenders' budgets are fixed. Attackers reinvest profits into better capabilities.
The IAB Marketplace: Supply Chain Access on Demand
Initial Access Brokers have industrialized the breach business. Current dark web pricing (February 2026):
| Access Type | Average Price | Median Sale Time |
|---|---|---|
| Basic RDP credentials | $150-400 | 3 days |
| VPN access | $500-1,500 | 5 days |
| Corporate email access | $300-800 | 2 days |
| Domain Administrator | $2,000-8,000 | 7 days |
| MSP/IT Provider access | $8,000-25,000 | 14 days |
| Software vendor access | $15,000-100,000 | 21 days |
Notice the pricing hierarchy. Software vendor access commands the highest prices because of the supply chain multiplier effect.
The market has 380+ active IABs (up 45% from 2024), and competition has driven basic access prices down 60% over two years.
Translation for enterprise defenders: Network access to your organization can probably be purchased for less than a nice dinner in Manhattan.
Breaking the Cycle: Strategic Interventions
The self-reinforcing cybercrime economy won't collapse on its own. But security leaders can take strategic action to reduce their contribution to the cycle and improve their defensive posture.
Intervention 1: Make Ransomware Payments Unnecessary
Every dollar not paid to ransomware operators is a dollar that doesn't fund future attacks.
The goal isn't "never pay ransoms"—it's "never need to pay."
Investments that matter:
- Immutable, air-gapped backups tested monthly
- Ransomware-resistant architecture (segmentation, least privilege)
- Incident response playbooks rehearsed quarterly
- Recovery time objectives (RTOs) measured in hours, not days
The ROI calculation: If your backup and recovery capability costs $2 million annually but prevents a potential $5 million ransom payment, that's not just a $3 million savings—it's $5 million denied to the criminal ecosystem.
Intervention 2: Starve the IAB Marketplace
If nobody is buying access, fewer people will sell it.
Reduce your value as a target:
- Assume breach: Design systems that limit blast radius
- Zero Trust architecture: Even with Domain Admin, attackers can't easily move
- Deception technology: Make attackers waste time on honeypots
- Continuous validation: Attack surface management, penetration testing
Reduce your breach probability:
- Identity is the perimeter: MFA on everything, phishing-resistant where possible
- Endpoint protection: EDR on every device, including servers and developer workstations
- Patch velocity: Days, not weeks, for critical vulnerabilities
- Vendor access segmentation: Third parties get isolated access, not network keys
Intervention 3: Know Your Supply Chain
You can't defend what you don't understand.
Minimum viable supply chain security:
- Software Bill of Materials (SBOM): Generate for your 10 most critical applications
- Dependency scanning: Automated CVE correlation for all packages
- Vendor inventory: Which third parties have network access? How much?
- Build pipeline audit: Who can modify what you ship to customers?
Advanced supply chain security:
- SLSA Level 3+: Hardened build platforms, signed provenance
- Reproducible builds: Verify that source produces identical binary
- Behavioral monitoring: Profile normal software behavior, alert on deviations
- Continuous vendor assessment: Move beyond annual questionnaires
Intervention 4: Collective Defense
The cybercrime ecosystem succeeds because attackers collaborate effectively. Defenders... don't.
Start collaborating:
- Threat intelligence sharing: ISACs, industry groups, trusted circles
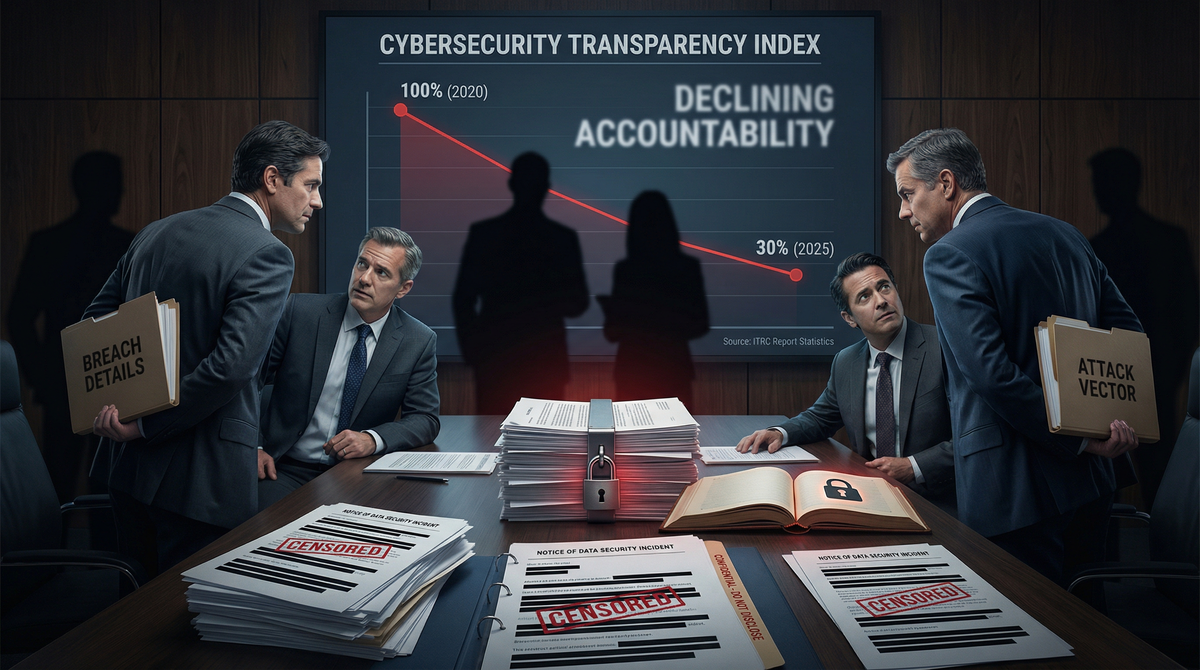
- Incident disclosure: If you're breached, others can learn from you
- Supply chain coordination: Require SBOMs from vendors, share with customers
- Tool sharing: Open source security tools benefit everyone
The uncomfortable truth: Your competitors getting breached makes you less safe, not more. Their breach proceeds fund attacks on you.
The Board Conversation: Translating Economics to Strategy
Reframing Risk
Don't say: "We need to implement zero trust architecture and software composition analysis."
Do say: "Right now, criminal organizations are investing millions in capabilities specifically designed to breach companies like ours. Every company that pays a ransom funds more sophisticated attacks. We have a choice: invest in defenses that make us hard targets, or eventually contribute to the cycle ourselves."
The Metrics That Matter
Traditional security metrics:
- Vulnerability counts
- Patch compliance percentages
- Security tool coverage
Economic impact metrics:
- Cost to attack us (how much would an IAB charge for our access?)
- Time to detection (how long could attackers operate before we notice?)
- Recovery capability (would we need to pay, or could we recover independently?)
- Supply chain exposure (how many vendors could compromise us?)
Investment Priorities
Based on the economic analysis, highest-ROI security investments:
- Backup and recovery — The nuclear option against ransomware coercion
- Identity protection — The most common initial access vector
- Supply chain visibility — You can't protect what you can't see
- Detection engineering — Assume breach, detect early, limit impact
- Segmentation — Limit blast radius, reduce attacker ROI
The Uncomfortable Conclusion
Every organization that pays a ransom, every credential sold, every supply chain compromise—they all feed the same machine.
We're not just defending individual organizations. We're participating in an economic system that's currently tilted in the attackers' favor.
The good news: economics can be changed. If enough organizations invest in resilience, reduce their breach probability, eliminate their need to pay ransoms, and collaborate on defense—the attacker ROI starts to fall.
The bad news: we're not there yet. The cybercrime economy is growing faster than legitimate tech. Supply chain attacks are becoming more sophisticated and more common.
The choice for security leaders isn't whether to engage with this reality—it's how.
You can continue treating security as a compliance checkbox, accepting that breaches are inevitable and ransoms are just another cost of doing business.
Or you can recognize that every dollar denied to the cybercrime economy makes everyone safer—including you.
The supply chain cybercrime economy is self-reinforcing. But it can be weakened. One organization's resilience at a time.
Immediate Action Items
This Week
- [ ] Review ransomware response capability: Can you recover without paying?
- [ ] Identify your 3 most critical vendors: What access do they have?
- [ ] Check IAB pricing: Search for your industry/size to understand attacker economics
This Month
- [ ] Generate SBOMs for 5 critical applications
- [ ] Audit backup recovery time: Conduct actual restoration test
- [ ] Map third-party access: Network diagrams showing vendor connections
- [ ] Review identity hygiene: MFA coverage, credential exposure monitoring
This Quarter
- [ ] Implement continuous vendor monitoring
- [ ] Conduct supply chain tabletop exercise
- [ ] Build detection capabilities for supply chain scenarios
- [ ] Join or form industry threat sharing group
This analysis was prepared by the Breached.Company research team. For real-time breach intelligence and supply chain security insights, follow us on Twitter/X or subscribe to our weekly briefing.





